Securing Your Smart Devices: Understanding IoT SSH Applications
Connecting our world has become quite a big thing, hasn't it? From smart homes to industrial sensors, devices are talking to each other more than ever. This vast network of connected gadgets is what we call the Internet of Things, or IoT. According to Lewis, the Internet of Things, or IoT, is the integration of people, processes, and technology with connectable devices and sensors to enable remote monitoring, status, and control. It's a way for physical objects to share data without needing a person to step in, which is pretty neat, you know.
These devices, whether they are home appliances or factory machines, collect and exchange data over the internet. The internet of things (IoT) refers to a network of physical devices, vehicles, appliances, and other physical objects that are embedded with sensors, software, and network capabilities. It's about making our physical surroundings digitally aware, and that's a big step for how we interact with technology, in a way.
As more and more things get connected, keeping them safe becomes a really important job. This is where a tool called SSH comes into play for these IoT setups. It helps make sure that when your devices talk, their conversations stay private and secure. So, understanding how `iot ssh applications` work is pretty key for anyone dealing with these smart systems, especially today.
Table of Contents
- What is SSH and Why It Matters for IoT
- Common IoT SSH Applications in Action
- Setting Up SSH for Your IoT Devices
- Benefits of Using SSH in IoT Environments
- Challenges and Best Practices for IoT SSH
- Frequently Asked Questions About IoT SSH
- The Future of IoT Security with SSH
What is SSH and Why It Matters for IoT
SSH, or Secure Shell, is a network method that lets you operate network services safely over an unsecured network. It provides a strong cryptographic method for data communication. Think of it like a very secure tunnel for your data, so that's pretty good. This means when you connect to an IoT device using SSH, the information you send and receive is protected from prying eyes.
A Secure Channel for Your Devices
For IoT devices, which are often out in the open or in places without much physical security, SSH is incredibly useful. It helps you manage these devices remotely without worrying too much about someone listening in on your commands or stealing sensitive information. This secure connection is a big deal for keeping your smart systems safe, you know.
The Need for Security in a Connected World
The internet of things (IoT) is a vast network of objects, including sensors, home appliances, vehicles, and factory machines, that share data over the internet. As "My text" points out, the IoT involves physical objects with sensors that communicate with computers. This widespread connection means there are many points where security could be weak. SSH helps to close these gaps, making sure that each device interaction is authorized and private, which is quite important.
Common IoT SSH Applications in Action
So, how do people actually use SSH with their IoT devices? There are a few main ways that are really common and very helpful. These applications show just how versatile and important SSH is for keeping our connected world running smoothly and safely, in a way.
Remote Device Management
Imagine you have a smart sensor in a faraway location, maybe monitoring crops or checking air quality. If something goes wrong, you can't just drive out there every time. This is where SSH shines. You can log into the device from anywhere with an internet connection, check its status, restart it, or even change its settings. This saves a lot of time and effort, naturally.
Secure Data Transfer
IoT devices often collect sensitive data, like environmental readings, personal health information, or industrial performance metrics. Sending this data over an unsecured network could be risky. SSH provides a secure way to move files between your device and a server. This means your data stays private and safe from unauthorized access, which is pretty good for everyone involved.
Firmware Updates and Maintenance
Just like your phone or computer, IoT devices need updates to fix bugs or add new features. SSH lets you securely push these updates to your devices, even if they are spread out across many different places. This makes keeping your devices up-to-date much simpler and safer, you know, which is a big plus.
Setting Up SSH for Your IoT Devices
Getting SSH ready for your IoT devices might seem a bit technical at first, but it's really quite straightforward once you get the hang of it. The main idea is to make sure your devices can talk to you securely and that only you can access them, so that's the goal.
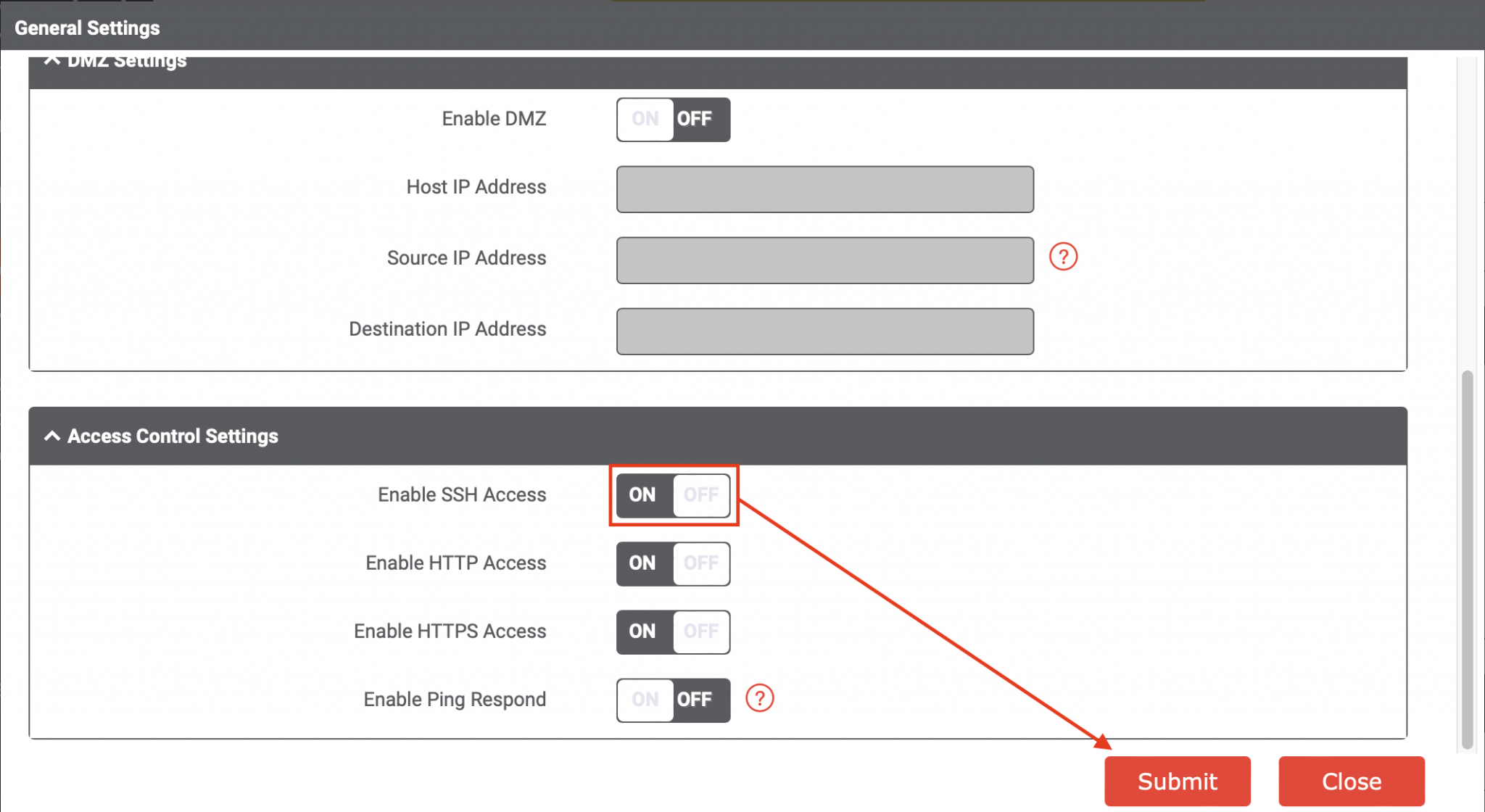
Key Considerations for Secure Setup
When setting up SSH, it's wise to use strong passwords, or even better, SSH keys. SSH keys are like a digital key and lock system that is much harder to break than a password. Also, it's a good idea to change the default SSH port on your device to something different. This makes it a little harder for automated attacks to find your device, you know, which is a smart move.
Practical Steps to Get Started
First, you'll need to make sure SSH is enabled on your IoT device. Many devices, like Raspberry Pis, have it ready to go. Then, you'll use an SSH client on your computer to connect. You'll enter the device's IP address and your login details. If you're using SSH keys, you'll need to set those up on both your computer and the device. There are many guides online that can walk you through the specifics for your particular device, for instance.
Benefits of Using SSH in IoT Environments
Using SSH with your IoT devices brings a lot of good things to the table. It's not just about security; it also makes managing your devices much easier and more flexible, which is quite nice.
One big benefit is the ability to manage devices from anywhere. Whether you're at home, in the office, or on the go, you can connect to your IoT setup and make sure everything is running right. This remote access is a huge time-saver and lets you react quickly to any issues, which is really helpful, honestly.
Another plus is the strong security it offers. With SSH, your data is encrypted, meaning it's scrambled so that only the intended recipient can read it. This helps protect sensitive information from being intercepted by bad actors. It also helps confirm that the device you are connecting to is actually the one you think it is, which adds another layer of trust, in a way.
SSH also helps with automation. You can write scripts that use SSH to perform tasks on your devices automatically, like collecting data at certain times or running updates overnight. This makes managing a large number of IoT devices much more efficient. It's a powerful tool for scaling your IoT projects, you know, and makes things pretty smooth.
Finally, SSH is widely supported and well-understood. This means there's a lot of help available if you run into problems, and many tools already work with it. It's a proven technology, so you can feel pretty confident relying on it for your IoT security needs, which is a good thing to know.
Challenges and Best Practices for IoT SSH
While SSH is very useful for IoT, there are still some things to keep in mind to make sure you're using it as safely and effectively as possible. No system is perfect, and being aware of potential issues helps a lot, you know.
Common Hurdles
One challenge can be managing SSH keys for many devices. If you have hundreds or thousands of IoT gadgets, keeping track of all the keys can get tricky. Another hurdle is making sure your devices have enough processing power to handle the encryption SSH uses. Some very small or low-power devices might struggle a bit, apparently.
Also, if a device is compromised, SSH access could be used by someone else. This is why strong authentication and careful access control are so important. It's not enough to just enable SSH; you have to manage it well, too, which is just a little extra work but worth it.
Tips for Better Security
Always use SSH keys instead of passwords if you can. Disable password login for SSH once keys are set up. Regularly update your device's firmware and SSH client software to patch any known security weaknesses. Limit who can access your devices via SSH, and only allow access from specific IP addresses if possible. This adds layers of protection that make it much harder for unauthorized people to get in, you know, which is really smart.
Consider using a VPN (Virtual Private Network) for an extra layer of security when connecting to your IoT devices remotely. This creates an encrypted tunnel for all your network traffic, not just SSH. Regularly review your device logs for any unusual activity, too. Being proactive about security can save you a lot of trouble down the line, as a matter of fact.
Frequently Asked Questions About IoT SSH
People often have questions when they start looking into using SSH for their IoT devices. Here are some common ones that might help clear things up, you know.
What is SSH in IoT?
SSH in IoT is a secure way to connect to and manage your smart devices remotely. It uses strong encryption to protect the data exchanged between your computer and the device, keeping your commands and information private. It's basically a secure remote control for your connected gadgets, in a way.
Why is SSH important for IoT security?
SSH is important because it helps keep your IoT devices safe from unauthorized access and data breaches. Without it, anyone could potentially listen in on your device's communications or even take control of it. It adds a vital layer of protection, making sure only authorized users can interact with your devices, which is pretty essential for peace of mind.
How do I use SSH for remote IoT access?
To use SSH for remote IoT access, you first need to make sure SSH is turned on on your device. Then, from your computer, you'll use an SSH client application. You'll type in a command that includes your device's network address and your login details. Once connected, you can type commands to control or check on your device, just as if you were sitting right next to it, which is very convenient.
The Future of IoT Security with SSH
As the Internet of Things keeps growing, the need for solid security methods like SSH will only become more pressing. More devices mean more potential points of weakness, and SSH offers a time-tested way to keep things locked down. It's a foundational tool for anyone serious about the safety and reliability of their connected systems, you know, and will likely remain so for a long time.
The term IoT, or Internet of Things, refers to the collective network of connected devices and the technology that facilitates communication between devices and the cloud, as well as between devices themselves, as "My text" explains. With this vast network, `iot ssh applications` will continue to be a go-to solution for secure remote management, updates, and data handling. Staying informed about the best practices and new developments in SSH for IoT will help ensure your smart world stays safe and functional. Learn more about IoT security on our site, and link to this page for more about managing your IoT devices. You can also explore general SSH practices at a site like SSH.com, which is pretty helpful.
SSH into your IoT Enterprise Gateway - NCD.io

SSH into your IoT Enterprise Gateway - NCD.io

IoT SSH Remote Access - SocketXP Documentation