SSH IoT Anywhere: Free IP Address Solutions For Remote Access
Getting to your Internet of Things (IoT) devices, no matter where they are, can feel like a real puzzle. You want to check on things, send new instructions, or just see what's happening. Yet, so many IoT gadgets sit behind tricky network setups, without their own easy-to-reach public IP addresses. This makes traditional remote access a tough nut to crack, very often.
Imagine your smart home devices, or perhaps some sensors out in a field, just doing their thing. You might need to adjust a setting or pull some data. But how do you connect to them directly and safely when they don't have a fixed, public address you can just type in? This is where the idea of "ssh iot anywhere ip address free" comes into its own, you see.
We're going to explore how Secure Shell (SSH) can be your best friend for this kind of remote management. We'll look at ways to connect to your IoT gadgets securely, even when their internet address changes or they're tucked away behind a router. It's about making things work smoothly, basically, without needing to pay for special IP addresses or fancy services.
Table of Contents
- Understanding the IoT Remote Access Challenge
- The Cleverness of SSH Tunnels and Reverse SSH
- Setting Up SSH for Your IoT Devices
- Getting Past Dynamic IP Obstacles
- Keeping IoT SSH Connections Safe
- Going Beyond Basic SSH: Advanced Tips for IoT
- Frequently Asked Questions
- Get Connected Today
Understanding the IoT Remote Access Challenge
Connecting to IoT devices can be a real head-scratcher. Most of these small gadgets don't get their own public IP address. They often sit behind a home router, using a private address. So, trying to connect directly from outside your home network is, well, pretty much impossible, you know.
Then there's the issue of dynamic IP addresses. Your home internet provider often changes your public IP address every now and then. This means the address you used yesterday might not work today, which is a bit of a nuisance, as a matter of fact.
Firewalls add another layer of complexity. They are there to protect your network, but they also block incoming connections. Getting through them usually means setting up "port forwarding," which can be a bit fiddly and, frankly, sometimes a security worry. This is where the challenge really sits.
Sometimes, when an IP address changes, your SSH client might give you a warning. It might say something about a "man in the middle attack." This happens because your computer remembers the old IP and its digital fingerprint. When the IP is new, the fingerprint doesn't match, and the warning pops up, which is pretty much a safety feature.
This warning, while helpful, can be quite confusing if you don't know why it's appearing. It's not always an actual attack, but rather a sign that something about the connection's identity has shifted. So, you need to know how to handle it, basically.
The Cleverness of SSH Tunnels and Reverse SSH
SSH tunnels are a rather clever way to get around these IP address problems. Think of it like creating a secret, secure pathway through the internet. This pathway lets your IoT device talk to you, even if it doesn't have a public IP address, which is quite handy.
A "reverse SSH tunnel" is especially useful for IoT. Instead of you connecting to the device, the device connects out to a middle server, sometimes called a "jump host." This middle server then acts as a bridge. So, you connect to the middle server, and it sends your commands through the tunnel to your IoT device, more or less.
This setup means your IoT device doesn't need a public IP. It just needs to be able to make an outgoing connection to the middle server. Many cloud providers offer small, inexpensive, or even free-tier virtual machines that can serve as this jump host. This makes the "free IP address" part of "ssh iot anywhere ip address free" quite achievable, you know.
Using a jump host also helps with firewalls. Since the IoT device is initiating the connection outwards, it usually bypasses strict incoming firewall rules. This simplifies things a great deal, honestly.
There are services that provide this jump host functionality, sometimes for free for basic usage. They manage the server for you, making it even simpler to set up your remote connections. So, this is a very practical approach, to be honest.
Setting Up SSH for Your IoT Devices
Getting SSH ready for your IoT devices involves a few key steps. It's about setting up the secure keys and making sure your computer knows how to talk to them. This can feel a little technical at first, but it's quite straightforward once you get the hang of it, you know.
Generating and Handling SSH Keys
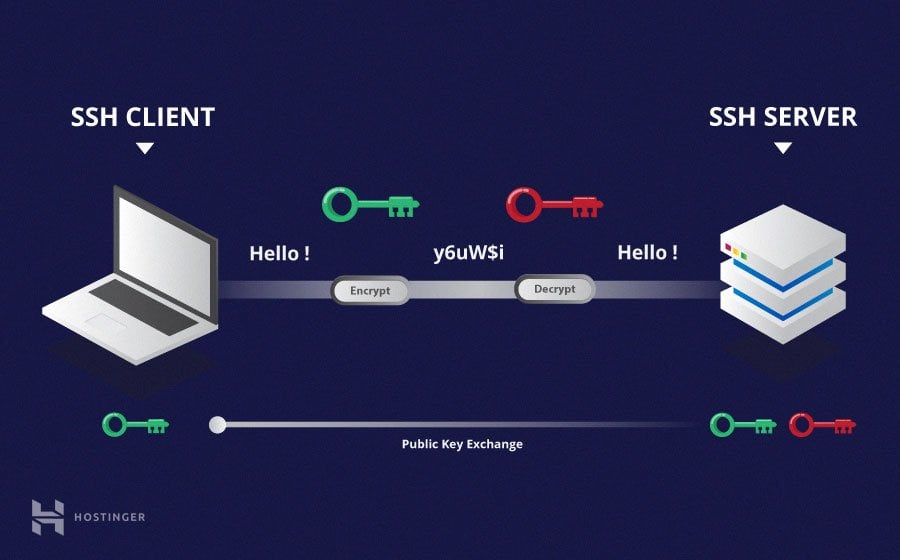
SSH keys are like digital passports for your connections. You have a public key and a private key. The public key goes on your IoT device or the jump host, and you keep the private key safe on your computer. They work together to prove who you are, which is pretty important for security.
To create a public key, you often use a command like `ssh-keygen`. Once you have it, you might need to copy it. For example, on a Mac or Linux machine, you can use `pbcopy < ~/.ssh/id_rsa.pub` to put it right onto your clipboard. This makes it easy to paste into web interfaces, as a matter of fact.
When you add an SSH key to a cloud platform's virtual machine, like on Google Cloud Platform, it often picks up a username from the key itself. You might think it's just a piece of data, but it can influence the default username for your connection. This is something to be aware of, actually.
If you have several IoT devices or different projects, you might want to use multiple SSH keys. For instance, you could have one key named `id_rsa_test`. To use this with a regular Git server or a specific IoT device, you'll need to tell your SSH client which key to use. This is where your SSH configuration file comes in handy, you see.
The documentation for using specific keys isn't always super clear. But you can usually specify the key file directly in your SSH command with the `-i` option. For example, `ssh -i ~/.ssh/id_rsa_test user@host` would tell SSH to use that particular key. This helps a great deal, honestly.
Arranging SSH on Windows
If you're using Windows, OpenSSH through PowerShell is a great tool. You can set up hostnames and ports in a configuration file. This file is typically located at `C:\Users\YourUsername\.ssh\config`. If it's not there, you can just create it, which is pretty simple.
To make or change this file, you can use a text editor. Just type `notepad C:\Users\YourUsername\.ssh\config` in PowerShell and press Enter. This will open the file, or create it if it doesn't exist, so you can add your settings, you know.
Inside this `config` file, you can define shortcuts for your connections. For example, you might have a section like this:
Host myiotdevice HostName 192.168.1.100 Port 22 User pi IdentityFile ~/.ssh/id_rsa_iotThis means you can just type `ssh myiotdevice` instead of remembering the IP, port, and username. It makes connecting much faster and easier, which is very convenient.
For using multiple SSH keys, you'd add more `Host` entries with different `IdentityFile` paths. This lets you manage connections to various devices or services, each with its own key, which is pretty neat. This setup works well with a typical Git server too, by the way.
Writing Scripts for Remote Commands
Sometimes you need to run commands on an IoT device automatically. Maybe you have a server that needs to tell another device to do something. You can create a bash script on one server to execute commands on another via SSH. This is a very common use case, you know.
To do this, you'll need to make sure the first server has the private key for the second device. You can use the `-i` option again in your script to specify the key file. For instance, a line in your script might look like `ssh -i /path/to/your/private_key user@remote_server "command_to_run"`. This tells SSH exactly which key to use for that specific connection, which is really helpful.
This method is very useful for automating tasks, like collecting data, deploying updates, or restarting services on your IoT devices. It means you don't have to manually log in every time, which saves a lot of effort, actually.
Make sure the private key file on the first server has the correct permissions so only the necessary user can read it. This is a vital security step. Otherwise, others might be able to use your key, and you certainly don't want that, you know.
Getting Past Dynamic IP Obstacles
Dynamic IP addresses are a common problem for remote access. Your internet service provider changes your public IP address from time to time. This means the address you use to connect to your home network or IoT devices can suddenly be different, which is a bit of a pain.
One popular way around this is using Dynamic DNS (DDNS) services. These services give you a fixed hostname, like `myiotdevice.dyndns.org`. When your home IP address changes, a small program on your router or an IoT device updates the DDNS service with the new IP. So, you always connect using the same hostname, and the DDNS service points you to the correct, current IP. There are free DDNS options available, which is pretty cool.
Another approach involves using cloud-based SSH tunneling services. These services provide a stable public endpoint for your IoT device to connect to. Your device initiates an outgoing SSH connection to this cloud server. Then, you connect to that same cloud server, and it routes your SSH session to your device through the pre-established tunnel. Some of these services offer free tiers for limited usage, which is very useful for testing or small projects.
These solutions effectively give your IoT device a consistent "address" even when its underlying IP changes. It makes remote management much more reliable. So, you don't have to constantly check your IP, which is a big relief, you know.
Choosing between DDNS and a cloud-based tunnel depends on your setup. DDNS is great if you can configure your router or have a device always running on your network. Cloud tunnels are good if your device can only make outgoing connections or if you prefer not to mess with router settings. Both help you achieve "ssh iot anywhere ip address free" in different ways, really.
Keeping IoT SSH Connections Safe
Security is super important when you're connecting to your IoT devices over SSH. You want to make sure no one else can listen in or pretend to be your device. There are ways to check what your SSH connection is doing and how to handle warnings, you know.
Checking SSH Capabilities
It's useful to know what security methods your SSH client and server support. You might want to find out what MACs (Message Authentication Codes), ciphers, and key exchange algorithms (kexalgorithms) are being used. This helps you understand the strength of your connection, which is quite important.
You can ask SSH to tell you this information dynamically instead of looking through its source code. OpenSSH version 5.7, for example, brought in the `kexalgorithms` option. This lets you choose which key exchange methods are used for both the client and server. So, you can pick stronger ones if you want, or perhaps older ones if you need to connect to an older device, you know.
To see what an SSH client supports, you can often run a command like `ssh -vvv user@host` and look through the verbose output. It will list the supported algorithms and the ones being negotiated. This gives you a clear picture of the security parameters in play, which is pretty handy, actually.
Adding a `kexalgorithms` setting to your SSH client or server configuration file lets you control this. For example, in your `~/.ssh/config` file, you could add `KexAlgorithms curve25519-sha256@libssh.org,ecdh-sha2-nistp521`. This forces SSH to use specific, often stronger, methods. It gives you more control over your connection's safety, you see.
Handling IP Changes and Warnings
When an IoT device or a server you connect to changes its IP address, your SSH client might give you a warning. It might say something like "REMOTE HOST IDENTIFICATION HAS CHANGED!" This is SSH's way of telling you that the host's identity (its digital fingerprint) doesn't match what it remembers for that IP. This can happen if the IP truly changed, or, in a very rare case, if someone is trying to intercept your connection, which is why it's a "man in the middle attack" warning, you know.
If you know the IP address has genuinely changed, you need to update your `known_hosts` file. This file, usually located at `~/.ssh/known_hosts`, stores the fingerprints of servers you've connected to. When the warning appears, SSH often tells you which line in the file to remove. You can open the file with a text editor and delete that specific line, which is pretty straightforward.
Alternatively, you can use the `ssh-keygen -R hostname` command to remove the old entry automatically. For instance, `ssh-keygen -R myiotdevice.dyndns.org` would clear the old record. After removing the old entry, the next time you connect, SSH will ask you to confirm the new host's fingerprint, and you can accept it. This updates your `known_hosts` file with the new, correct information, basically.
It's important to be careful with these warnings. Always verify that the IP change is legitimate before accepting a new fingerprint. If you're unsure, it's better to investigate before connecting. Your IoT device's security depends on it, you see.
Going Beyond Basic SSH: Advanced Tips for IoT
SSH can do more than just give you a command line. It has some rather useful features that can make managing your IoT devices even better. These include forwarding graphical interfaces and handling file transfers, you know.
If your IoT device has a graphical application that you want to run and see on your computer, SSH can forward the X11 connection. This means the application runs on the IoT device, but its display appears on your desktop. If you run SSH and the display isn't set, it means SSH isn't forwarding the X11 connection. To confirm that SSH is forwarding X11, you'd check for a line containing "requesting X11 forwarding" in the verbose SSH output. You usually enable this with the `-X` option when you connect, like `ssh -X user@host`. This is quite useful for debugging graphical tools on small devices.
For transferring files, SFTP (SSH File Transfer Protocol) is your friend. It uses SSH for secure file copying. However, connecting to an SFTP server using Windows File Explorer can be a bit tricky. The explorer has an option to connect to an FTP server, but not directly to an SFTP server. This means you might need a third-party SFTP client like WinSCP or FileZilla. These tools make it easy to drag and drop files securely to and from your IoT devices, which is very helpful, you know.
Sometimes, when you're trying to figure out a specific SSH setting or troubleshooting, you might come across mentions of variables that seem perfect but aren't defined. This variable sounds like what I am looking for, but it is not defined. This often means you're looking for a specific configuration option that might be part of a newer SSH version, or perhaps it's a setting on the server side that you don't control. It can be a bit frustrating, but often a quick search for the exact setting you need can clear things up. Or, you might need to update your SSH client or server software, which is pretty common.
Understanding these extra features of SSH can really expand what you can do with your IoT devices remotely. It's about getting the most out of your secure connection. So, exploring these options is definitely worth your time, honestly.
Frequently Asked Questions
Here are some common questions people have about SSH and IoT devices, more or less.
How do I SSH into a device with a dynamic IP address?
You can use a Dynamic DNS (DDNS) service. This service gives your device a constant hostname. When your device's IP address changes, it updates the DDNS service. So, you always connect using the same hostname, and the DDNS service points to the current IP, which is very convenient, you know.
Can I SSH into my IoT device without port forwarding?
Yes, you can. The best way is to use a reverse SSH tunnel. Your IoT device makes an outgoing connection to a publicly accessible server (a jump host). Then, you connect to that jump host, and it forwards your SSH session to your IoT device through the tunnel. This avoids needing to open ports on your home router, which is pretty neat.
Are there free services for SSH tunneling to IoT devices?
Yes, there are. Some cloud providers offer free tiers for small virtual machines that can act as your jump host. Additionally, some specialized services provide free basic SSH tunneling or remote access for a limited number of devices. You'll need to look around a bit to find one that fits your needs, but they definitely exist, you know.
Get Connected Today
Setting up SSH for your IoT devices, even without a fixed IP address, is totally achievable. By using SSH tunnels, managing your keys, and understanding configuration files, you can get reliable remote access. This means you can keep an eye on your gadgets, send commands, and make updates from anywhere. Learn more about SSH solutions on our site, and connect to this page for more tips.
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know