Connecting Your IoT Device Securely: SSH Behind A Firewall
Are you finding it tough to reach your smart gadgets when they are tucked away behind a network firewall? It's a common puzzle for many, especially as more and more smart devices become part of our daily lives, both at home and for work. Getting to your Internet of Things (IoT) devices, like a Raspberry Pi or a custom sensor, often means dealing with network restrictions that keep them safe but also out of easy reach. This can be a real headache when you need to check on things, update software, or simply get some data.
The challenge of connecting to an IoT device behind a firewall is something many folks encounter, whether they are hobbyists tinkering with home automation or professionals managing a fleet of remote sensors. Firewalls are there for good reasons, of course; they act like a digital bouncer, stopping unwanted visitors from getting into your private network. Yet, this security measure can make it quite tricky to perform necessary maintenance or gather information from your devices when you are not physically present, which is a bit of a bummer.
Happily, there are smart ways around this, and using SSH (Secure Shell) is often the best path forward. SSH offers a secure way to communicate with your devices, creating a protected tunnel for your commands and data. We'll look at how you can set up SSH to reach your IoT device, even when a firewall stands in the way, so you can keep things running smoothly, no matter where you are. It's actually quite useful.
Table of Contents
- Understanding the Challenge: IoT Devices and Firewalls
- SSH: The Secure Connection Friend
- Methods for SSH Access Through a Firewall
- Setting Up SSH on Your IoT Device
- Managing SSH Keys and Configuration Files
- Troubleshooting Common SSH Issues
- Keeping Your IoT SSH Connections Safe
- Frequently Asked Questions
- Final Thoughts on IoT Access
Understanding the Challenge: IoT Devices and Firewalls
When you have an IoT device, like a smart thermostat or a security camera, it usually sits inside your home or office network. This network, in turn, is protected by a firewall, which is a bit like a guard at the gate. This setup, while good for security, can make it surprisingly hard to connect to your device from outside, say, when you're at a coffee shop or traveling. It's almost like the device is speaking a different language that the outside world doesn't understand directly.
What is a Firewall?
A firewall is basically a network security system that watches and controls incoming and outgoing network traffic based on predefined security rules. It establishes a barrier between a trusted internal network and untrusted external networks, such as the internet. For instance, your home router often has a built-in firewall that protects all the devices connected to it. This really helps keep things safe.
It decides which connections are allowed and which are blocked, based on things like port numbers, IP addresses, and communication protocols. Think of it as a bouncer at a club, letting in only those with the right pass. So, if you try to connect to your IoT device from outside, the firewall might just say "nope" because it doesn't recognize your connection as something it should let through, which is a bit of a hurdle.
Why IoT Devices Are Behind Firewalls
IoT devices are often behind firewalls for very good reasons. The main one is security. Many IoT devices, especially older ones or those from less reputable makers, might not have the strongest security features built right in. They could have weak passwords, unpatched software, or even hidden vulnerabilities. Placing them behind a firewall adds a crucial layer of protection, shielding them from direct attacks from the internet. This is a pretty sensible approach, you know.
Another reason is how home networks typically work. Most home networks use something called Network Address Translation (NAT). This means many devices inside your home share one public IP address that the internet sees. Your router handles all the traffic, directing it to the correct device inside. Without specific instructions, the router doesn't know where to send an incoming SSH connection request, so it just drops it, which is rather common.
SSH: The Secure Connection Friend
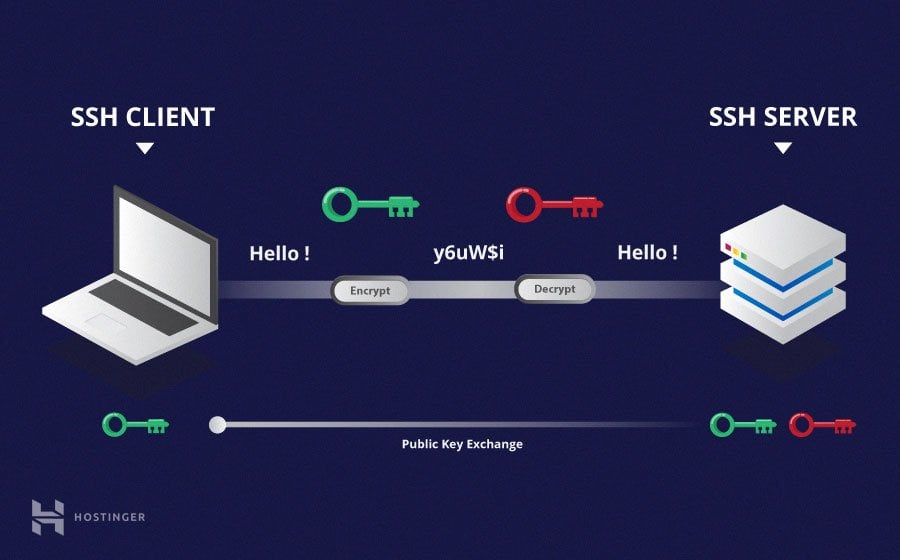
SSH, or Secure Shell, is a network protocol that gives users a secure way to access a computer over an unsecured network. It's widely used by system administrators to manage systems and applications remotely, allowing them to log in, run commands, and move files. For IoT devices, SSH is an incredibly useful tool because it provides a protected channel for remote management, even when your device is far away. It's like having a secret, safe path directly to your gadget, which is pretty neat.
How SSH Works Its Magic
SSH works by setting up an encrypted connection between a client (your computer) and a server (your IoT device). When you initiate an SSH connection, the client and server first agree on encryption keys, making sure that all communication between them is scrambled and private. This means that even if someone were to intercept your data, they wouldn't be able to read it. This is a really important security feature, actually.
The connection is authenticated using either passwords or, more commonly and securely, SSH keys. Once authenticated, you get a command-line interface (CLI) on your IoT device, just as if you were sitting right in front of it. You can run commands, transfer files, and even forward graphical applications (X11 forwarding), though that last bit can be a little tricky if not set up correctly, as I've found that `display` not being set means X11 isn't forwarding, and you need to look for "requesting x11 forwarding" in the output to confirm it, which is a useful tip.
SSH Keys for Better Security
While password authentication is possible with SSH, using SSH keys is significantly more secure and convenient. An SSH key pair consists of two parts: a private key, which you keep secret on your computer, and a public key, which you place on the IoT device you want to connect to. When you try to connect, the device challenges your client to prove it has the corresponding private key, without ever sending the private key itself over the network. This is a much stronger way to prove who you are, you know.
This method removes the risk of weak passwords and brute-force attacks. Plus, you don't have to type a password every time, which is a big time-saver. Generating these keys is fairly straightforward. On Linux or macOS, you typically use `ssh-keygen`. For Windows, if you're using OpenSSH through PowerShell, the process is similar. After generating, you often copy the public key to the device. I've had to do this for GitLab and GitHub, where you `pbcopy < ~/.ssh/id_rsa.pub` to get it onto your clipboard and then paste it into the settings, which is pretty handy. Managing multiple keys can be a bit of a dance, too, especially figuring out how to tell your SSH client which key to use for which connection, as the documentation sometimes isn't clear on explicitly using only a certain key.
Methods for SSH Access Through a Firewall
Getting your SSH connection past a firewall can be done in several ways, each with its own benefits and things to consider. The best method for you will depend on your specific network setup, your comfort with network configurations, and the level of security you need. It's not a one-size-fits-all situation, so you have options, which is good.
Port Forwarding: The Direct Approach
Port forwarding, also known as port mapping, is arguably the most straightforward way to allow external access to a device behind a firewall. You configure your router to direct incoming traffic on a specific port to a specific IP address and port on your internal network. For instance, you might tell your router that any connection coming in on public port 2222 should be sent to your IoT device's internal IP address (e.g., 192.168.1.100) on its SSH port (usually 22). This essentially creates a direct path through the firewall. This is a fairly common setup.
While simple, port forwarding does open a specific port on your router to the internet, which means it's visible to anyone scanning for open ports. Because of this, it's really important to ensure your IoT device has strong security measures in place, like SSH key authentication and a non-root user for SSH access. You should also consider changing the default SSH port (22) on your IoT device to a different, less common port to reduce automated scanning attempts. It's a small step that can make a difference, you know.
Reverse SSH Tunneling: A Clever Trick
Reverse SSH tunneling is a more advanced but incredibly powerful method, especially when you can't set up port forwarding on the firewall or router that protects your IoT device. With a reverse tunnel, your IoT device initiates an SSH connection outwards to a publicly accessible server (often called a "jump host" or "relay server") that you control. This connection creates a tunnel, and then you can connect to that public server, which effectively acts as a bridge back to your IoT device through the established tunnel. It's a bit like your IoT device calling home and leaving a door open for you. This is a very neat solution.
This method is particularly useful if your IoT device is behind a strict firewall or a NAT setup that you can't change, like in a corporate network or some public Wi-Fi spots. The IoT device makes an *outbound* connection, which firewalls usually allow, and then maintains that connection. You then connect to your public server, and through that server, you can reach your IoT device. It's a bit more involved to set up initially, but it offers a lot of flexibility and can be quite secure, too. You just need that publicly accessible server, which might be a small cloud instance.
VPN: A Private Road
Using a Virtual Private Network (VPN) is another excellent way to access your IoT devices securely behind a firewall. A VPN creates an encrypted tunnel over the internet, making it seem as though your remote computer is directly on the same local network as your IoT device. Once you connect to your home or office VPN server, all your network traffic goes through that server, and you can then access any device on that network as if you were physically there. This is a very robust security option.
Setting up a VPN server on your home router (if it supports it) or on a dedicated device like a Raspberry Pi can provide a secure and comprehensive way to access all your internal network resources, not just one IoT device. It means all your traffic is encrypted, and your remote computer gets an IP address within your home network's range. This can be a bit more complex to set up initially than simple port forwarding, but it offers a much higher level of security and convenience for accessing multiple devices. It's a bit like having your own private highway to your home network, you know.
Cloud-Based Solutions for IoT
For those who prefer a less hands-on approach with network configurations, cloud-based IoT platforms offer managed solutions for remote device access. Services like AWS IoT Core, Google Cloud IoT Core (though some services are changing), or Azure IoT Hub provide secure ways for your devices to connect to the cloud. You then interact with your devices through the cloud platform's dashboard or APIs, without needing to directly manage SSH connections or firewall rules. This is a pretty popular option for larger deployments.
These platforms often use MQTT or other protocols for device communication, abstracting away the underlying network complexities. While they might not use SSH directly for device interaction, they provide secure and scalable ways to manage and monitor your IoT fleet from anywhere. This approach simplifies a lot of the network setup, but it does mean relying on a third-party service and potentially incurring costs. It's a good choice if you're looking for something that just works, more or less.
Setting Up SSH on Your IoT Device
Before you can connect to your IoT device using SSH, you need to make sure SSH is actually running on the device itself. Most Linux-based IoT devices, like Raspberry Pis, come with SSH capabilities, but it might not be enabled by default. Getting this right is the first big step, you know.
Enabling SSH on the Device
The exact steps to enable SSH vary slightly depending on your IoT device's operating system. For Raspberry Pi OS, for example, you can enable SSH through the `raspi-config` tool or by simply placing an empty file named `ssh` (no extension) into the boot partition of the SD card before first boot. If the device is already running, you can connect a keyboard and monitor, then open a terminal and run `sudo systemctl enable ssh` and `sudo systemctl start ssh`. This gets the SSH server going. It's pretty straightforward, really.
Once SSH is enabled, it's a good idea to change the default password for the user you'll be using (e.g., 'pi' on a Raspberry Pi) if you haven't already. This is a critical security step. You should also consider creating a new, non-root user for SSH access instead of using the default administrator account, as this adds another layer of security. It's a small change that makes a big difference, you know.
Configuring SSH for Remote Access
After enabling SSH, you might want to adjust its settings for better security or functionality. The main configuration file for the SSH server is typically located at `/etc/ssh/sshd_config`. You'll need root privileges to edit this file. Some common changes include: changing the default SSH port from 22 to a different, higher number (e.g., 2222), disabling password authentication in favor of key-based authentication, and disallowing root login. These steps significantly improve your device's security posture. It's a very good idea to do this.
For example, to change the port, you would find the line `#Port 22` and change it to `Port 2222` (remember to remove the '#' to uncomment it). To disable password authentication, look for `PasswordAuthentication yes` and change it to `PasswordAuthentication no`. After making any changes to `sshd_config`, you must restart the SSH service for them to take effect, usually with `sudo systemctl restart ssh`. This ensures your new settings are active, you know.
Managing SSH Keys and Configuration Files
Effective management of SSH keys and your SSH client configuration file can make connecting to your IoT devices much smoother and more secure. This is where a lot of the practical work happens, actually. It really helps to keep things organized.
Generating and Using SSH Keys
If you haven't already, generate an SSH key pair on your local computer. You can do this using the `ssh-keygen` command in your terminal. It will ask you where to save the keys and if you want to set a passphrase. A passphrase adds an extra layer of security to your private key, which is a very good idea. For instance, you might run `ssh-keygen -t rsa -b 4096 -C "your_email@example.com"`. This creates a strong RSA key pair, you know.
Once generated, your public key (usually `id_rsa.pub`) needs to be copied to your IoT device. The `ssh-copy-id` command is the easiest way to do this: `ssh-copy-id user@your_iot_device_ip`. If `ssh-copy-id` isn't available or you're doing it manually, you can copy the contents of your public key file and paste it into the `~/.ssh/authorized_keys` file on your IoT device. Just make sure the permissions on `~/.ssh` and `authorized_keys` are correct (700 for the directory, 600 for the file) to keep things secure. I've found that sometimes, especially on Google Cloud Platform VMs, the key gets picked up and saved under a username, which can be a bit confusing if you thought it was just metadata, and you're trying to connect with a different user, which is a bit of a quirk.
Editing Your SSH Config File
The SSH configuration file (`~/.ssh/config`) on your local machine is a powerful tool for simplifying your SSH connections and managing multiple keys. You can set up aliases, specify different keys for different hosts, and define various connection parameters. This means you don't have to type long commands every time. To create or edit this file, you can type `notepad ~/.ssh/config` on Windows using PowerShell, or `nano ~/.ssh/config` on Linux/macOS. This is a very handy file to know about.
Here's an example of what you might put in your `config` file for an IoT device:
Host myiotdevice HostName your_iot_device_public_ip_or_domain Port 2222 User iotuser IdentityFile ~/.ssh/id_rsa_iot_key ForwardAgent yes
With this setup, you can simply type `ssh myiotdevice` in your terminal, and SSH will automatically use the correct hostname, port, user, and the specified SSH key (`id_rsa_iot_key`). This is incredibly convenient, especially if you're dealing with multiple devices or different SSH keys, as I've had to do when trying to use `id_rsa_test` for a specific Git server. This variable sounds like what I am looking for, but it is not always defined or clear in its application, which can be a bit frustrating. This file really helps organize your connections.
Troubleshooting Common SSH Issues
Even with careful setup, you might run into problems when trying to SSH into your IoT device. Don't worry, many issues have common solutions. It's like a puzzle, you know.
Connectivity Problems
If you're getting a "Connection refused" or "Connection timed out" error, here are a few things to check. First, make sure your IoT device is actually powered on and connected to the network. Second, confirm that the SSH server (sshd) is running on your IoT device. You can often check its status with `sudo systemctl status ssh` if you can access the device locally. Third, double-check your firewall rules, both on your router (for port forwarding) and on the IoT device itself (if it has its own firewall like `ufw`). A wrong port or a blocked connection is a pretty common culprit. Sometimes, the issue is simply a typo in the IP address or port number, which is a surprisingly frequent occurrence.
Authentication Failures
If SSH connects but then denies your access, it's usually an authentication problem. Make sure you're using the correct username for the device. If you're using password authentication, verify the password. If you're using SSH keys, ensure your public key is correctly placed in the `~/.ssh/authorized_keys` file on the IoT device and that the permissions on that file and the `~/.ssh` directory are set correctly (600 for `authorized_keys`, 700 for `~/.ssh`). Also, confirm that your private key on your local machine has the right permissions (usually 600). I've had times where I added a key to Google Cloud Platform VM, and it picked the username and saved the key under it, which was a bit different from what I expected, thinking it was just a metadata key for general access. This can make you scratch your head a bit.
X11 Forwarding Notes
For those trying to forward graphical applications, if you run `ssh` and the `display` variable is not set, it means SSH is not forwarding the X11 connection. To confirm that SSH is forwarding X11, you need to check for a line containing "requesting x11 forwarding" in the output of your SSH connection attempt with the `-v` (verbose) flag. This variable sounds like what I am looking for, but it is not always defined in the way you might expect, which can be a little confusing. Make sure your local machine has an X server running (like XQuartz on macOS or VcXsrv on Windows) and that your SSH client command includes the `-X` or `-Y` flag for X11 forwarding. It's a slightly more advanced feature, so it might need a bit more fiddling.
Keeping Your IoT SSH Connections Safe
Security is paramount when you're allowing remote access to your IoT devices. A compromised device can become a doorway into your entire network. So, being careful here is really important. Here are some key practices to keep your SSH connections secure:
- Use SSH Keys, Not Passwords: This is the golden rule. SSH keys are far more secure than passwords, especially if you use a strong passphrase for your private key.
- Disable Password Authentication: Once you have SSH key authentication working, disable password authentication in your `sshd_config` file. This stops brute-force attacks dead in their tracks.
- Change the Default SSH Port: Moving SSH from port 22 to a non-standard port (e.g., 2222, 22022) reduces the noise from automated scanning bots. It's not a security panacea, but it helps.
- Use Non-Root Users: Always connect with a regular user account that has limited privileges, and use `sudo` for administrative tasks only when needed. This limits the damage if your
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know