Securing Your Smart Home: An SSH IoT Device Firewall Tutorial
Keeping your smart gadgets safe from digital intruders is, you know, a pretty big deal these days. With so many devices connecting to the internet, from smart lights to security cameras, each one can, in a way, be a potential doorway for unwanted access. This guide will walk you through how to use SSH, a truly powerful tool, to help build a stronger defense around your IoT devices. We're talking about making them less vulnerable and more secure, which is, honestly, a very good thing for everyone with smart tech at home or in a small business setting.
You might have some little devices, perhaps a Raspberry Pi running your home automation or a custom sensor array, and you want to manage them remotely. That's where SSH comes in, providing a secure way to connect. But what happens if someone tries to sneak in? That's where a firewall, working hand-in-hand with SSH, becomes really important. It’s about setting up boundaries, you know, like a digital bouncer for your tiny computers.
We'll look at how to set up SSH securely, how to manage those tricky SSH keys, and then, too, how to put some basic firewall rules in place. This isn't just about stopping bad guys; it's also about making sure your devices only do what you want them to do, and only allow connections from places you trust. It's a bit like making sure your front door has a good lock and only the right people have the key, which is, in some respects, a simple idea but very effective.
Table of Contents
- Why IoT Security Matters
- Understanding SSH for IoT Devices
- Setting Up SSH Keys for Your IoT Device
- Configuring SSH for Better Security
- Implementing a Basic Firewall for SSH
- Troubleshooting and Advanced Tips
- Frequently Asked Questions
- Wrapping Things Up
Why IoT Security Matters
IoT devices are, you know, everywhere these days. From smart thermostats to little cameras, they make our lives more convenient. But, they also, sometimes, come with security weaknesses. An unprotected IoT device can be a pretty easy target for bad actors, allowing them to sneak into your home network, steal data, or even use your devices for bigger attacks. It's like leaving a window open for everyone to see inside, which is, honestly, a bit unsettling. A strong defense, including a solid SSH setup and a firewall, can really help keep these digital doors locked tight.
Understanding SSH for IoT Devices
What is SSH?
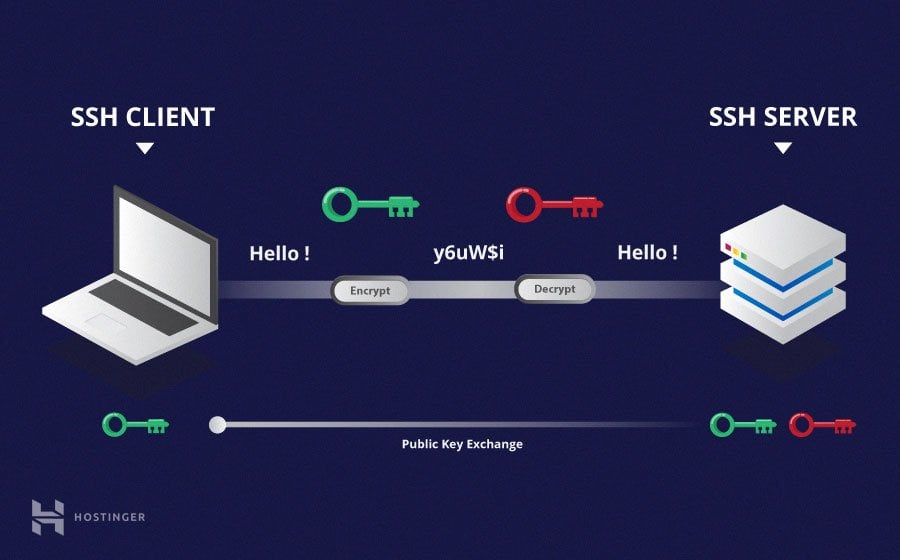
SSH, or Secure Shell, is a protocol that lets you connect to a remote computer, like your IoT device, over an insecure network, but in a very secure way. It provides a strong, encrypted channel for communication. This means that anything you send or receive, like commands or files, stays private. It's a bit like having a secret, coded language for talking to your devices, so only you and your device can understand what's being said, and that, is that, a pretty neat trick.
The Role of SSH Keys
While you can use passwords with SSH, using SSH keys is a much, much safer approach. An SSH key pair has two parts: a private key and a public key. You keep the private key secret on your computer, and you put the public key on the IoT device you want to connect to. When you try to connect, the two keys "talk" to each other to confirm your identity without ever sending your private key over the network. This makes it incredibly difficult for someone to guess or steal your login credentials. It's like having a very unique, unforgeable digital signature for yourself, which, you know, adds a lot of peace of mind.
Setting Up SSH Keys for Your IoT Device
The first step in securing your IoT device with SSH is getting your key pair ready. This process is pretty straightforward, and it really boosts your security. You want to make sure your keys are strong and kept safe. This is, basically, your digital identity for your device, so handle it with care.
Generating SSH Keys
On your local computer, you'll open a terminal or PowerShell window to create your keys. You typically use a command like `ssh-keygen`. This command asks you where to save the key and if you want a passphrase. A passphrase adds an extra layer of security to your private key, which is, honestly, a really good idea. If someone ever gets hold of your private key, they still can't use it without the passphrase. It's like putting a safe around your key, which, in some respects, is a very clever move.
Copying Your Public Key to the IoT Device
Once you have your key pair, you need to get the public key onto your IoT device. The `ssh-copy-id` command is, perhaps, the easiest way to do this if you're on a Linux or macOS system. You just run `ssh-copy-id username@your_iot_device_ip`, and it handles the rest. If you're on Windows using PowerShell, you might need to do it a bit differently. A common way is to manually copy the content of your public key file, which usually ends in `.pub`. For example, you might use a command like `cat ~/.ssh/id_rsa.pub` to display the content, then copy it. As someone mentioned, "In terminal enter this command with your ssh file name pbcopy < ~/.ssh/id_rsa.pub this will copy the file to your clipboard now open you github account go to settings > ssh and gpg keys >." While that specifically talks about GitHub, the core idea of copying the public key to your clipboard is the same for your IoT device. You then paste this key into the `~/.ssh/authorized_keys` file on your IoT device. You can use a text editor like `nano` or `vi` on the device itself to "Edit or create the file now by typing" the appropriate command, like `nano ~/.ssh/authorized_keys`. Just make sure the permissions on that file are correct (usually 600) so only the owner can read or write to it, because, you know, security.
Managing Multiple SSH Keys
Sometimes, you might want to use different SSH keys for different devices or services. For instance, you might have one key for your personal IoT projects and another for work-related servers. As someone else wondered, "Now I want to use multiple ssh keys (so my key will get the name id_rsa_test, so how do I configure the.ssh/config file under windows, that it works with a usual git server". This is where the SSH configuration file comes in handy. On Windows, this file is typically located at `C:\Users\YourUsername\.ssh\config`. If it doesn't exist, you can just create it. You can define specific settings for different hosts here. For example, you might add entries like this:
Host myiotdevice HostName 192.168.1.100 User pi IdentityFile ~/.ssh/id_rsa_iot Port 2222 Host anotherdevice HostName another.example.com User admin IdentityFile ~/.ssh/id_rsa_another This way, when you type `ssh myiotdevice`, SSH knows exactly which hostname, user, and "IdentityFile" (your private key) to use, which is, you know, super convenient. This answers the question "How do I set the host name and port in a config file for windows, using openssh through powershell", as this config file works seamlessly with OpenSSH through PowerShell, too.
Configuring SSH for Better Security
Beyond just using keys, there are some other settings you can tweak in your SSH configuration, both on your client computer and on the IoT device itself, to make things even more secure. These adjustments can, in a way, tighten the screws on your digital defenses.
Editing the SSH Config File on Windows
As mentioned, for Windows users, the SSH config file is a game-changer. It's usually found at `C:\Users\YourUsername\.ssh\config`. If you don't have one, just create a new text file there and save it as `config` (no file extension). You can open it with Notepad or any text editor. This file lets you set up aliases, specific ports, and even specify which private key to use for a given connection. For instance, if your IoT device uses a non-standard SSH port, you can add a `Port` line in your host entry. This helps keep your connections organized and makes connecting a lot simpler, which is, basically, a win-win.
Explicitly Using a Specific Key
Sometimes, you might want to force SSH to use a particular private key for a connection, even if you have multiple keys or a default one. This comes up when, for example, "The documentation is not clear on how to explicitly use only that key." You can do this right from the command line using the `-i` flag, like `ssh -i ~/.ssh/id_rsa_mydevice username@your_iot_device_ip`. This tells SSH to try only that specific key. It's a useful trick when you're scripting connections or troubleshooting, as someone else wanted to know, "How do I ssh to server 2 using my private key file from server 1?" You would use this `-i` flag within your bash script, too, which is, you know, a very direct way to control things.
Understanding Host Key Warnings
Have you ever seen a warning about a "man in the middle attack" when connecting via SSH? This happens when the SSH client sees that the host key of the server (your IoT device, in this case) has changed. As someone noted, "One of the servers I frequently log into via ssh has changed it's ip address, So, now I'm getting man in the middle attack warnings when I try to use ssh via windows powershell and." This warning is a security feature. It means the client thinks it might be connecting to a different machine than before, or that someone is trying to intercept your connection. If you know your device's IP or host has genuinely changed, you'll need to remove the old host key entry from your `~/.ssh/known_hosts` file. On Windows, this file is typically in `C:\Users\YourUsername\.ssh\known_hosts`. You can open it, find the line with the old IP or hostname, and delete it. Just be absolutely sure you're connecting to the correct device afterwards, because, obviously, you don't want to connect to the wrong place.
Implementing a Basic Firewall for SSH
While SSH provides a secure connection, a firewall adds another layer of protection by controlling which network traffic can reach your IoT device at all. This is, basically, like putting a gate around your device, letting only authorized traffic through. It’s a pretty important step for keeping things safe.
Firewall Basics for IoT
Most Linux-based IoT devices, like a Raspberry Pi, come with a built-in firewall system called `netfilter`, which is controlled by tools like `iptables` or `UFW` (Uncomplicated Firewall). The goal is to allow only necessary incoming connections. For SSH, this usually means allowing traffic on port 22 (the default SSH port) only from specific IP addresses you trust, or from your local network. Blocking all other incoming traffic is a pretty good default security posture, which, you know, just makes sense.
Using UFW on Linux-Based IoT Devices
UFW is a user-friendly way to manage `iptables` rules. If your IoT device runs a Debian-based Linux (like Raspberry Pi OS), UFW is often available. First, you might need to install it: `sudo apt update && sudo apt install ufw`. Then, you can set up your rules. Here are some common steps:
sudo ufw enable # Activates the firewall sudo ufw default deny incoming # Blocks all incoming connections by default sudo ufw default allow outgoing # Allows all outgoing connections sudo ufw allow ssh # Allows incoming SSH connections on port 22 If you changed your SSH port (which is, honestly, a good security practice), you'd specify that port instead, for example, `sudo ufw allow 2222/tcp`. For even tighter security, you can restrict SSH access to only your home network or a specific IP address: `sudo ufw allow from 192.168.1.0/24 to any port 22`. This means only devices on your local network can connect via SSH, which is, you know, a very strong barrier. You can check the firewall status with `sudo ufw status verbose`, which, actually, shows you all the active rules.
Advanced Firewall Considerations
For more complex setups, you might consider setting up a VPN (Virtual Private Network) to access your IoT devices. This way, your devices don't need to expose any ports directly to the internet. You connect to your VPN, and then you can securely SSH into your devices as if you were on your home network. This adds a very robust layer of security. Also, regularly updating your IoT device's operating system and SSH software is crucial, as updates often include security patches that address new vulnerabilities, which, basically, keeps you ahead of the curve.
Troubleshooting and Advanced Tips
Even with careful setup, you might run into a few snags or want to explore more advanced SSH features. Knowing how to troubleshoot and fine-tune your SSH setup can, you know, save you a lot of headaches.
Scripting SSH Connections
If you're automating tasks, you might want to run commands on your IoT device from another server using a script. As someone asked, "However, I would be creating a bash script from server 1 that will execute some commands on server 2 via ssh, How do I ssh to server 2 using my private key file from server 1?" You can do this by specifying the private key with the `-i` flag and then adding the commands directly after the SSH command. For example: `ssh -i /path/to/your/private_key user@your_iot_device_ip 'ls -l /data && echo "Done!"'`. This lets your script log in, run commands, and then disconnect, which is, honestly, very efficient for automation.
Checking SSH Capabilities
Sometimes, you might wonder what specific encryption methods or key exchange algorithms your SSH client or server supports. As someone pondered, "Is there a way to make ssh output what macs, ciphers, and kexalgorithms that it supports, I'd like to find out dynamically instead of having to look at the source." You can often get this information by running SSH with verbose output. For instance, `ssh -v your_iot_device_ip` will show a lot of detail about the connection process, including the algorithms being negotiated. Also, "Openssh 5.7 introduced the kexalgorithms option, Add a kexalgorithms knob to the client and server configuration to allow selection of which key exchange methods are used by." This means you can specify preferred algorithms in your SSH config file for stronger security, which is, you know, a good way to keep up with current security recommendations.
SFTP Connections on Windows
Accessing files on your IoT device securely often involves SFTP (SSH File Transfer Protocol). While some file explorers, as someone pointed out, "The explorer has an option to connect to a ftp server but not a sftp server," don't directly support SFTP, there are great third-party tools for Windows that do. Programs like WinSCP or FileZilla are popular choices. They allow you to connect to your IoT device using SSH keys and easily transfer files, which is, basically, a very handy feature for managing your device's files.
X11 Forwarding and Display Issues
If you're trying to run graphical applications from your IoT device and display them on your local computer, you're looking at X11 forwarding. As someone noted, "If you run ssh and display is not set, it means ssh is not forwarding the x11 connection." To enable it, you typically use the `-X` flag when connecting: `ssh -X user@your_iot_device_ip`. To confirm it's working, "To confirm that ssh is forwarding x11, check for a line containing requesting x11 forwarding in the output of." You'll see messages related to X11 forwarding in the verbose output (`ssh -v -X ...`), which is, honestly, a clear sign that it's doing its job.
Frequently Asked Questions
Here are some common questions people have about securing IoT devices with SSH and firewalls:
How do I change the default SSH port on my IoT device?
You can change the SSH port by editing the `sshd_config` file on your IoT device, typically located at `/etc/ssh/sshd_config`. Find the line that says `Port 22`, change `22` to your desired port number (e.g., `2222`), and then restart the SSH service (e.g., `sudo systemctl restart ssh`). Remember to update your firewall rules to allow traffic on the new port, which, you know, is pretty important.
Is it safe to expose my IoT device's SSH port to the internet?
Generally, it's not recommended to expose any port directly to the internet unless absolutely necessary and with strong security measures in place. If you must, ensure you're using SSH key authentication only (disable password login), change the default SSH port, and restrict access with firewall rules to only trusted IP addresses. A VPN is, arguably, a much safer alternative for remote access.
What if my SSH config variable isn't defined?
If you're trying to use a variable in your SSH config file and it seems "not defined," as someone else mentioned, it's likely that SSH doesn't recognize that specific variable name or it's not supported in your OpenSSH version. Double-check the OpenSSH documentation for the correct syntax and available options for your client version. Sometimes, what sounds like a good idea for a variable might not be an actual feature of the SSH client, which, you know, happens.
Wrapping Things Up
Securing your IoT devices with SSH and a firewall is a pretty essential step in today's connected world. By using strong SSH keys, configuring your client and server settings carefully, and implementing basic firewall rules, you can, in a way, create a much safer environment for your smart gadgets. Remember that ongoing vigilance is key; regularly update your devices and review your security settings. This proactive approach helps protect your privacy and keeps your home network secure, which is, basically, a very smart move for everyone. For more detailed security advice, you might check out resources from organizations like the National Cyber Security Centre. Learn more about home network security on our site, and link to this page for advanced IoT security practices.
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know