SSH IoT Device Management: Keeping Your Connected Tech Safe And Sound
In our world today, where smart gadgets are practically everywhere, keeping them running smoothly and, very importantly, safe is a big job. Think about all those little devices that collect information or do things around us, from smart home sensors to industrial equipment. They often need someone to check on them, change their settings, or fix something if it goes a bit wrong. This is where the idea of managing these devices from a distance comes into play, and it’s a very practical way to stay on top of things, you know.
Typically, someone looking after these smart devices uses a special computer program or a web application. This allows them to see how each device is doing from one central spot, a kind of digital control center. From this point, they can make changes, and that’s pretty handy, really. But how do you do all this without putting your devices at risk?
This is where a method called Secure Shell, or SSH, steps in as a truly helpful answer. With SSH, getting to your IoT devices from far away is quite safe, it’s not hard to set up, and it’s pretty reliable. This guide will explain how to make the most of this method, and it’s actually simpler than it sounds.
Table of Contents
- Why SSH is a Must for IoT Device Management
- Setting Up SSH for Your IoT Gadgets
- Keeping Your IoT SSH Connections Safe
- Everyday Uses of SSH in IoT
- Frequently Asked Questions About IoT SSH
- Conclusion
Why SSH is a Must for IoT Device Management
When you have smart devices spread out, perhaps across a building or even different cities, checking on them one by one can be quite a chore. This is where the idea of monitoring them remotely becomes really helpful. It means you can keep an eye on how these smart gadgets are working together without having to be right next to them, which is pretty convenient, too.
The Core Idea Behind SSH
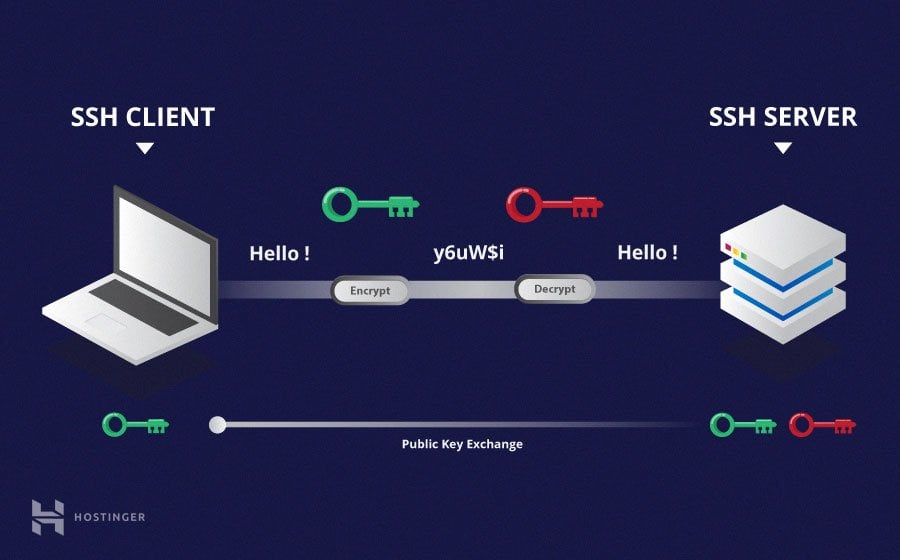
At its heart, SSH is a network method that uses codes to keep things secret. It’s mainly used to get into networked devices and servers in a safe way. While SSH first started as a secure way to do things, its usefulness has grown a lot, and it’s now seen as one of the most important tools for safe remote access, so it’s quite popular.
It helps you connect to a device over a network and send commands as if you were sitting right in front of it. This connection is encrypted, meaning that any information going back and forth is scrambled, which makes it very hard for someone else to peek at what you are doing. This is a big plus, as a matter of fact, especially when dealing with important device settings.
Making Remote Access Secure
IoT devices are often out in the open, or at least not behind the same strong protections as your main office computers. This means they are more likely to be targets for people who want to do harm. SSH provides a secure pathway to these devices, which is quite important. It’s like having a secret, protected tunnel directly to your device, which is a good way to think about it.
Remote IoT SSH connections are a really good way to keep an eye on and manage your IoT devices from a distance in a safe manner. You get to securely connect to an IoT device and reach its functions and settings. This gives you full control and helps you fix problems with ease, so it’s pretty powerful.
What SSH Helps You Do
With SSH, you can access your IoT devices from far away, which is very helpful for many tasks. This includes getting to the device’s functions, changing settings, and even fixing things if they go wrong. For example, if you have a sensor that needs a software update, you can send that update through SSH without having to visit the sensor itself, which saves a lot of time and effort, you know.
For IT teams, using SSH with IoT devices means they can jump onto any device on the network. From there, they can handle things like sending out updates, setting up new configurations, or even troubleshooting if something goes wrong. This makes managing a large number of devices much simpler, and it’s quite efficient.
Setting Up SSH for Your IoT Gadgets
Getting SSH ready for your IoT devices involves a few steps to make sure everything connects properly and securely. This part is about making sure you can actually reach your devices when you need to, and that’s pretty vital, really.
Getting Ready for Connection
First, you need to make sure your IoT device is set up to accept SSH connections. This usually means enabling the SSH service on the device itself. Sometimes, this involves changing a setting in the device’s software or running a specific command. It’s a bit like opening a specific door on your device so SSH can come in, so you need to be careful with it.
You might also need to set up network rules, like port forwarding on your router, if your device is behind a home or office network. This helps the SSH connection find its way to your device from the internet. It’s a technical step, but it’s often necessary for outside access, you know.
Handling SSH Keys
One of the most secure ways to connect with SSH is by using SSH keys instead of just passwords. An SSH key pair has two parts: a private key that stays on your computer and a public key that goes on the IoT device. When you try to connect, these keys work together to prove who you are without sending a password over the network, which is much safer, honestly.
With remote IoT SSH key management, you can manage and find all your authentication keys and SSH login files from a central spot. This helps you securely connect and manage machines. This is very helpful when you have many devices and need to keep track of who can access what, so it’s a big organizational benefit.
Sometimes, you might add an SSH key to a cloud platform’s virtual machine, and it might pick up a username and save the key under it. You might think it’s just a simple piece of data, but it’s actually tied to the user. It’s good to know how to explicitly use only a specific key if you have many, which can be a bit confusing sometimes.
Configuring Your Access
For Windows users, especially when using OpenSSH through PowerShell, you can set the host name and port in a config file. This file helps you save connection details so you don't have to type them every time. You just edit or create this file by typing a command, and it makes connecting much quicker, which is pretty neat.
If a device you often connect to changes its IP address, you might get warnings about a "man in the middle" attack when you try to use SSH. This happens because your computer remembers the old IP and its digital fingerprint. When the IP changes, the fingerprint doesn't match, and SSH warns you. You'll need to update your known hosts file to fix this, and that’s a very important security step.
Keeping Your IoT SSH Connections Safe
Security is a very big deal when it comes to IoT devices, as they are often more exposed than other parts of your network. Making sure your SSH connections are safe is a core part of keeping your entire IoT setup protected, and it’s something you really need to focus on.
Best Practices for Security
To keep your IoT safe from unwanted access, you should follow some important security tips for SSH remote access. These tips help you protect your IoT devices. For instance, always use strong, unique passwords if you're not using keys, and change default usernames if possible. This makes it much harder for someone to guess their way in, you know.
Also, consider limiting who can connect to your devices. You can set up firewalls to only allow SSH connections from specific IP addresses. This adds another layer of protection, making it harder for unauthorized people to even try to connect, which is a good idea.
Watching Out for Warnings
SSH is designed to warn you about potential security issues. For example, if a device's digital fingerprint changes unexpectedly, SSH will give you a warning about a possible "man in the middle" attack. Pay close attention to these warnings. They are there to alert you to something unusual, and it’s very important not to ignore them, honestly.
If you get such a warning, investigate it right away. It could be a legitimate change, like a server update, or it could mean someone is trying to interfere with your connection. Knowing how to check for things like X11 forwarding, which SSH might or might not be doing, can also help you confirm your connection's behavior, and that’s quite useful for troubleshooting.
Centralized Key Control
Managing SSH keys across many IoT devices can become complicated very quickly. Using a system for centralized SSH key management allows you to keep all your authentication keys and login files in one secure place. This helps you manage access for all your devices more easily, and it’s a much more organized way to handle things.
This kind of system helps you discover all keys, revoke access when someone leaves your team, or update keys across your entire fleet. It reduces the chance of old, forgotten keys becoming a security risk, which is a pretty common problem without good management.
Everyday Uses of SSH in IoT
SSH isn't just for setting things up; it's a tool you'll use constantly for the day-to-day work of managing your IoT devices. It makes many routine tasks much simpler and faster, which is quite a benefit, really.
Updating and Changing Settings
One of the most common things you'll do with SSH is send updates to your devices. Whether it's a new software version, a security patch, or just a small bug fix, SSH lets you push these changes to devices remotely. This means you don't have to physically visit each device to update its software, which is a huge time-saver, you know.
You can also use SSH to change configurations on devices. For example, if a sensor needs to report data more frequently, you can log in via SSH and adjust that setting. This kind of immediate control is very powerful, and it helps keep your devices working exactly as you need them to.
Fixing Problems from Afar
When something goes wrong with an IoT device, SSH is often your first line of defense for troubleshooting. You can connect to the device, check its logs, see what processes are running, or even restart services. This remote access helps you figure out what’s happening and often fix it without needing to send someone out to the device's location, which is incredibly efficient, honestly.
For instance, if a device isn't sending data, you can SSH in to check its network connection or restart the data-sending application. This ability to diagnose and fix issues from anywhere is a big reason why SSH is so valuable for IoT management, and it really makes a difference.
Building Automated Tasks
You can use SSH in scripts to automate many tasks. For example, you could write a small program that connects to all your devices at night and pulls their log files for analysis. Or, you could have a script that checks device health every hour and alerts you if something seems off. This kind of automation saves a lot of manual effort, and it’s pretty smart.
This is where creating a bash script from one server that executes commands on another server via SSH comes in handy. You can use your private key file from the first server to connect to the second. This allows for automated, secure command execution, which is very useful for large-scale operations, and it simplifies things quite a bit.
Frequently Asked Questions About IoT SSH
People often have questions about using SSH for IoT devices, covering how it works, its security implications, and the best ways to manage connected devices remotely. Here are some common ones, and they’re good to think about.
How does SSH work for IoT devices?
SSH works by creating a secure, encrypted connection between your computer and the IoT device. When you initiate an SSH connection, the client (your computer) and the server (the IoT device) go through a process to agree on encryption methods and verify each other's identity. Once this is done, all communication, including commands you send and responses you get, travels securely through this encrypted tunnel. It’s like having a private conversation over a public phone line, and it’s very effective.
What are the main security concerns with IoT SSH access?
The main security concerns include using weak passwords, which can be easily guessed. Another worry is not managing SSH keys properly, which could lead to unauthorized access if a private key is compromised. Devices with old software versions that have security flaws are also a risk. Additionally, not keeping an eye on your network for unusual activity or "man in the middle" warnings can leave your devices open to attack. It’s all about staying vigilant, you know.
Can I manage all my IoT devices from one place using SSH?
Yes, you can certainly manage many IoT devices from a single location using SSH. This is often done through scripts that automate connections to multiple devices, or by using centralized management tools that leverage SSH in the background. With proper SSH key management and network configuration, you can effectively oversee and control a large fleet of IoT devices from your central digital control center. It makes large-scale operations much more feasible, and it’s a very practical approach.
Learn more about secure remote access on our site, and link to this page for further insights into IoT security.
Conclusion
Using SSH for IoT device management is a smart and safe way to handle your connected gadgets. It gives you the power to monitor, control, and fix issues from anywhere, which is incredibly convenient. By understanding how SSH works, setting it up correctly, and following good security habits, you can keep your IoT devices running smoothly and protected from unwanted visitors. It’s a very important tool for anyone dealing with smart technology today, and it helps a lot with peace of mind.
For more technical details on SSH, you might find information on the OpenSSH website helpful.
Keeping up with these practices ensures your IoT setup remains secure and efficient, which is what we all want, after all. This approach, as of today, May 15, 2024, remains a cornerstone for dependable IoT operations.
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know