Unlock Free SSH IoT Platform Solutions For Secure Remote Access
Are you looking to connect your small gadgets and sensors, perhaps some smart home devices or even tiny industrial bits, without spending a lot of money? It’s a pretty common wish, especially when you think about all the little computers out there that need to talk to each other safely. You might have heard about needing a special platform for this, and maybe you thought it would cost a fortune. Well, that’s not always the case, and there are some really clever ways to get things done without a big budget.
Many folks, you know, just want to get their projects going. They want to check on a sensor in the garden or maybe control a light from far away. The idea of setting up a whole system can feel a bit much, particularly if you are just starting out or working with a tight budget. So, the good news is, there are indeed free ways to make your devices connect and communicate in a safe way, and that's something pretty cool to think about.
This article is all about how you can use something called SSH, which is a very familiar tool for many, to build your very own free IoT platform. We'll talk about why it's a smart choice, how to get it going, and some common little bumps you might hit along the way. You will see how simple it can be, and how it really helps keep your things secure, which is very important these days.
Table of Contents
- Why SSH is Your Go-To for Free IoT Management
- Setting Up Your Free SSH IoT Platform
- Overcoming Common SSH IoT Challenges
- Practical Applications and Real-World Use
- Frequently Asked Questions
- Conclusion
Why SSH is Your Go-To for Free IoT Management
When you think about managing devices that are far away, or even just across the house, you need a way to connect that is both easy and safe. SSH, which stands for Secure Shell, is a really good fit for this, and it’s something you can use without paying anything. It’s a pretty standard tool for connecting to computers, so it makes sense to use it for your smaller IoT gadgets too, you know.
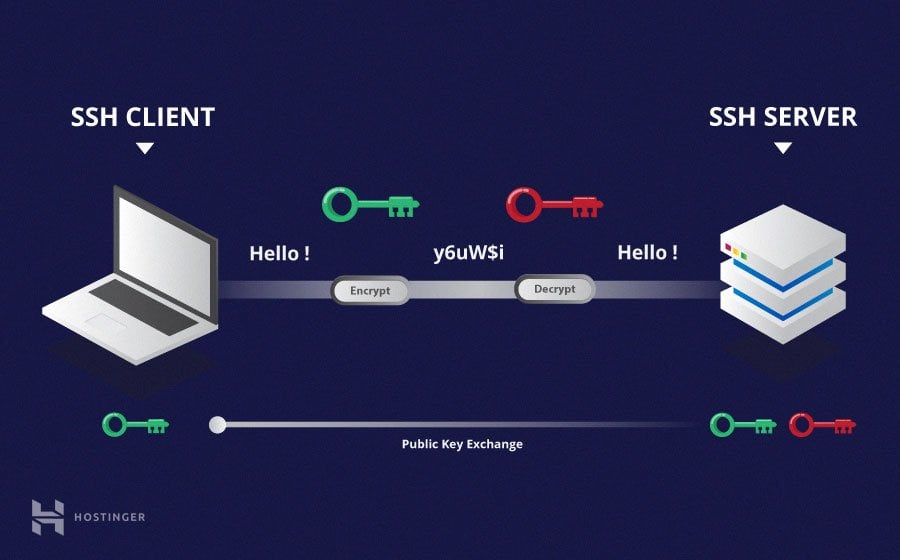
The Security Advantage
Security is a big deal these days, especially with so many devices connected to the internet. SSH helps keep your connections private and safe from prying eyes. It encrypts all the information that goes back and forth, so whatever commands you send or data you get back, it stays scrambled from others. This is a very important feature, frankly, when you are dealing with things that might be in your home or a business setting.
It uses strong methods to prove who you are, often with something called SSH keys. These keys are like super-secure digital fingerprints. Instead of a simple password that someone might guess, you have a pair of keys: one public, one private. The private key stays secret on your computer, and the public key goes on the device you want to connect to. This way, the device knows it’s really you trying to get in, and not some unwanted visitor. This setup, you see, makes it much harder for bad actors to get access to your things.
Cost-Effectiveness and Open Source
One of the best things about using SSH for your IoT setup is that it costs you nothing. SSH is an open-source tool, which means it's free to use, modify, and distribute. You don't need to sign up for expensive services or pay monthly fees to manage your devices. This makes it a really attractive option for hobbyists, small businesses, or anyone trying to keep their expenses down, so it's quite popular for that reason.
Because it's open source, there's a huge community of people who use it and contribute to it. This means there's a lot of help available online if you run into a problem, and the software itself is always getting better. This collaborative spirit means you get a very powerful tool that's constantly being improved by many different people, and that's a pretty good deal, actually.
Remote Access and Control
SSH lets you connect to your devices from anywhere in the world, as long as you have an internet connection. This is incredibly useful for IoT. You could be on vacation and still check on your home sensors, or you could manage a fleet of devices spread across different locations. It gives you direct control over your devices, letting you run commands, transfer files, and even troubleshoot issues as if you were sitting right in front of them.
Think about it: you can send commands to your Raspberry Pi to turn on a light, read sensor data, or restart a program, all from your laptop or phone. This ability to reach out and touch your devices remotely is, in some respects, what makes IoT so powerful. It's a pretty neat trick, really, to have that kind of reach.
Setting Up Your Free SSH IoT Platform
Getting your SSH IoT setup going isn't as hard as it might sound. It mostly involves generating some keys and making a few simple changes to files on your computer and your IoT devices. It's a bit like setting up a secret handshake between your computer and your little gadgets, you know.
Getting Started with SSH Keys
The very first step is usually to create your SSH keys. This is a one-time thing for your main computer. You will typically open a terminal or PowerShell window and use a command like `ssh-keygen`. This makes two files: your private key, which you keep very safe, and your public key, which you will put on your IoT devices.
Once you have your public key, you need to copy it to your IoT device. For instance, if you're using a Raspberry Pi, you might use `ssh-copy-id` or simply copy the contents of your public key file into the `~/.ssh/authorized_keys` file on the Pi. To get your public key easily, you can, in terminal, enter this command with your SSH file name: `pbcopy < ~/.ssh/id_rsa.pub`. This will copy the file to your clipboard. Now, you can open your GitHub account, go to settings, then SSH and GPG keys, and paste it there if you are connecting to Git services, or just paste it directly into your device's authorized keys file. Sometimes, the documentation is not clear on how to explicitly use only that key, but usually, SSH will try keys in a specific order, or you can specify it with the `-i` flag.
I remember adding an SSH key to a Google Cloud Platform VM, and it picked the username and saved the key under it, while I thought it was merely a metadata key. This can be a bit confusing at first, so it’s good to be aware that SSH keys can behave differently depending on the platform or system you are using, which is just something to keep in mind, you know.
Configuring SSH for Your Devices
After your keys are in place, you might want to adjust some settings for easier connections. This often means creating or editing an SSH config file on your main computer. For Windows users, if you are using OpenSSH through PowerShell, you can set the host name and port in a config file. You would edit or create the file now by typing something like `notepad ~/.ssh/config` in PowerShell.
Inside this file, you can set up shortcuts for your devices. For example, you might have an entry like this:
Host my_iot_sensor HostName 192.168.1.100 User pi Port 22 IdentityFile ~/.ssh/my_iot_key With this, you can just type `ssh my_iot_sensor` instead of the full command, and SSH will know exactly how to connect, using the right user, port, and even a specific key if you have many. This makes connecting to your many devices much simpler, which is pretty handy, actually.
Scripting for Automation
One of the really powerful things you can do with SSH is automate tasks. Instead of manually typing commands every time, you can write simple scripts to do things for you. For instance, you could be creating a bash script from server 1 that will execute some commands on server 2 via SSH. This is where the magic of a free IoT platform really starts to show. You can have your main computer check on all your sensors at certain times, or send commands based on conditions.
To SSH to server 2 using your private key file from server 1, your script might look something like `ssh -i /path/to/your/private_key_file user@server2_ip "command_to_run"`. This lets you chain commands together or perform regular checks without any manual effort. It’s a very efficient way to manage things, so it helps a lot with repetitive jobs.
Overcoming Common SSH IoT Challenges
While SSH is great, you might run into a few little bumps along the way. Knowing about these ahead of time can save you some head-scratching. These are just some common things that come up for people, you know.
Dealing with X11 Forwarding
Sometimes, you might want to run a graphical program on your IoT device and have it show up on your main computer's screen. This is called X11 forwarding. If you run SSH and the display is not set, it means SSH is not forwarding the X11 connection. You might see a message indicating that this variable sounds like what you are looking for, but it is not defined, which can be a bit confusing.
To confirm that SSH is forwarding X11, check for a line containing "requesting X11 forwarding" in the output of your SSH connection attempt, perhaps by adding `-v` for verbose output. You also need to make sure X11 forwarding is enabled in your SSH client and server configurations. It's a pretty specific setting, but once you know about it, it's usually easy to fix, you know.
Handling IP Changes and Security Warnings
IoT devices, especially in a home network, might sometimes change their IP address. When this happens, if one of the servers you frequently log into via SSH has changed its IP address, you might get "man in the middle attack" warnings when you try to use SSH via Windows PowerShell or any other client. This happens because SSH remembers the old IP address associated with the device's unique key, and when the IP changes, it thinks something suspicious is going on.
To fix this, you usually need to remove the old entry from your `known_hosts` file. SSH will tell you which line to remove in the warning message. It's a security feature that is, in a way, doing its job, even if it causes a temporary inconvenience. This is just something that pops up every now and then, so it's good to be ready for it.
Understanding SSH Capabilities
Sometimes, you might want to know what specific security methods your SSH client or server supports, like which MACs, ciphers, and key exchange algorithms it supports. You might want to find out dynamically instead of having to look at the source code or documentation. This can be useful for troubleshooting connection issues or making sure you are using the strongest available options.
OpenSSH 5.7 introduced the `KexAlgorithms` option, which allows selection of which key exchange methods are used. You can add a `KexAlgorithms` knob to the client and server configuration to allow selection of these methods. You can also use commands like `ssh -Q cipher` or `ssh -Q mac` to query what your client supports. Knowing these details can help you fine-tune your security settings, which is pretty useful for a free IoT platform, to be honest.
Practical Applications and Real-World Use
So, what can you actually do with a free SSH IoT platform? Quite a lot, it turns out! From simple home projects to more involved monitoring tasks, SSH provides a solid foundation. These examples show how versatile it can be, you know.
DIY Smart Home Projects
If you are into building your own smart home, SSH is a fantastic tool. You can use a Raspberry Pi or a similar small computer as a central hub, connecting to various sensors and actuators around your house. For instance, you could have a temperature sensor reporting data to your Pi, and then SSH into the Pi from your phone to check the readings. You could even send a command to turn on a smart plug connected to a lamp.
This approach gives you complete control and privacy, unlike some commercial smart home systems that rely on cloud services. It's a truly personalized system, and you get to decide exactly how everything works. This kind of hands-on control is very satisfying for many people, so it's a popular way to go.
Remote Sensor Monitoring
Imagine you have sensors in a remote location, maybe checking the water level in a tank or the temperature in a greenhouse. Running a cable is not always practical. With an IoT device connected via cellular or Wi-Fi and managed by SSH, you can access those sensors from anywhere. You can write a script on the device to collect data periodically and then SSH in to retrieve the logs or view the current status.
This is especially useful for projects where you need to collect environmental data over long periods. You can set up alerts, too, so if a reading goes above a certain point, the device can send you an email or a message, all managed through your SSH connection. It’s a very practical way to keep an eye on things when you are not there, you see.
Small-Scale Industrial IoT
For small businesses or workshops, SSH can be a cost-effective way to implement basic industrial IoT. You could monitor the status of machinery, track production counts, or even control simple processes remotely. A small device attached to a machine could report its operational status, and you could SSH in to check if it's running, or perhaps even trigger a shutdown if something looks wrong.
This approach avoids the need for expensive proprietary systems and gives you the flexibility to adapt the solution to your specific needs. It’s a very direct way to get data and control over your equipment, which is pretty valuable for smaller operations, you know. To learn more about secure remote access on our site, and link to this page for more secure IoT tips.
Frequently Asked Questions
Here are some common questions people have about using SSH for IoT:
Can I use SSH to manage multiple IoT devices at once?
Yes, absolutely. You can use scripts on your main computer to connect to many devices in sequence, running commands or gathering data from each one. This is how you build a simple, free IoT platform that scales to your needs. It's pretty straightforward to set up, too.
Is SSH secure enough for all IoT applications?
For many personal and small-scale commercial IoT applications, SSH provides a very good level of security. It uses strong encryption and authentication methods. However, for extremely critical systems, like those controlling power grids or medical devices, you might want to look into even more specialized security protocols and frameworks, but for most uses, it’s quite good, you know.
What if my IoT device doesn't have a screen or keyboard?
That's perfectly fine! Most IoT devices, like Raspberry Pis or ESP32 boards, are designed to be used "headless," meaning without a screen or keyboard. You connect to them remotely using SSH from your computer. All the commands and interactions happen through the terminal, which is, in some respects, how they are meant to be used.
Conclusion
Using SSH as the backbone for your free IoT platform is a really smart move. It gives you security, flexibility, and remote control, all without any cost. From setting up your SSH keys and configuring your devices to automating tasks with scripts, you have a powerful set of tools at your fingertips. You can manage everything from simple home gadgets to more complex sensor networks. It's a pretty empowering way to approach your projects, actually.
Even when you hit a small snag, like dealing with X11 forwarding or those "man in the middle" warnings when an IP address changes, there are clear ways to fix them. Knowing how to query SSH for its capabilities, like which ciphers it supports, also gives you more control over your setup. It's all about making your devices talk to each
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know