Securing Your Gadgets: An SSH IoT Tutorial For Today's Connected World
Getting your smart devices to talk to you safely, especially when they're far away, feels like a big puzzle for many. It's almost like trying to whisper secrets across a crowded room, hoping only the right person hears. This guide is all about making that happen with something called SSH, a really helpful tool for keeping your internet-connected things secure.
People often worry about who can get into their home or business devices, and that's a fair concern. With so many smart gadgets around, from tiny sensors to bigger control units, making sure they're locked down is a top priority. You know, you want to check on your device, but you don't want just anyone else checking on it too.
This tutorial will walk you through setting up a safe way to reach your IoT devices. We'll look at how SSH helps you do this, covering the basics and some handy tips for both beginners and folks who have done this a few times. It's pretty important to get this right, as a matter of fact, especially with so many devices now talking to the internet.
Table of Contents
- Why SSH for Your IoT Devices?
- Getting Ready: Your SSH Toolkit
- Making Your SSH Keys
- Connecting to Your IoT Device: The First Time
- Advanced SSH Tips for IoT Management
- Keeping Your IoT Connections Safe
- Frequently Asked Questions About SSH and IoT
Why SSH for Your IoT Devices?
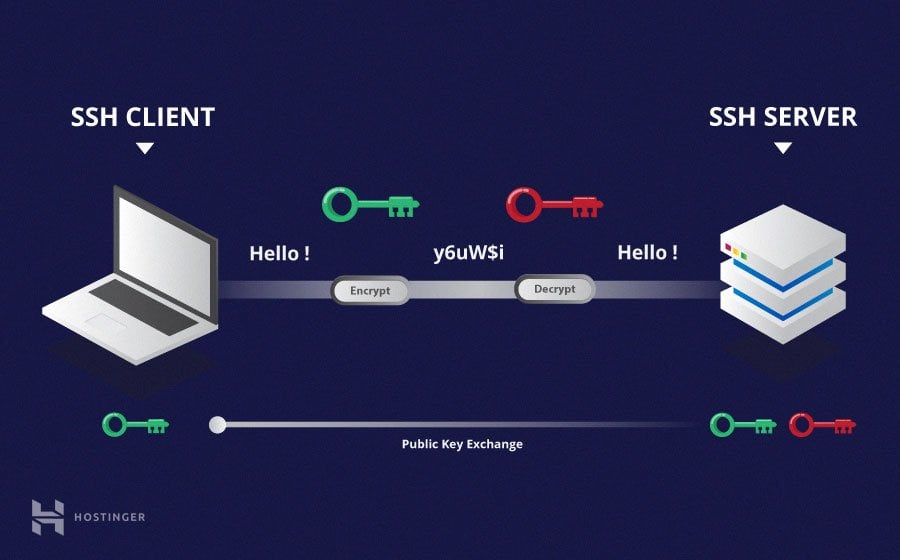
SSH, which stands for Secure Shell, is a way to get into another computer over a network in a safe manner. Think of it like a secret tunnel for your commands and information. For IoT devices, this means you can send instructions, check on things, or even change settings from your main computer, wherever you happen to be.
It's very important for keeping your tiny gadgets from being easily accessed by others. Unlike older, less safe methods, SSH scrambles all the information sent back and forth. This makes it really hard for anyone to peek at what you are doing or control your devices without permission.
The main idea is to use keys instead of just passwords. These keys are like super long, complex passwords that are nearly impossible to guess. One part stays on your computer, and the other part goes on the IoT device. When they match up, you're allowed in.
Getting Ready: Your SSH Toolkit
Before you can start talking to your IoT devices, you need a few things set up. It's kind of like gathering your tools before starting a building project. You'll need your IoT device ready and your main computer prepared for the connection.
Picking Your Device
Most small computers used for IoT, like Raspberry Pi boards or other single-board computers, come with SSH capabilities built in or can have them added pretty easily. You'll want to make sure your device is powered on and connected to your network, either by Wi-Fi or an Ethernet cable. You might need to enable SSH on the device itself, which is often a quick setting change.
Setting Up Your Computer
If you're using a Linux or macOS computer, SSH is typically already there. You just open your terminal program and you're good to go. For Windows users, it's a bit different. You can use OpenSSH, which is often included with newer versions of Windows, or you might install a tool like PuTTY. If you're using PowerShell, you can usually run SSH commands right there.
Making Your SSH Keys
This is where the real security comes in. Instead of typing a password every time, you'll use a pair of special files, your SSH keys. One is private, and you keep it secret; the other is public, and you share it with your devices. It's a very good way to keep things secure.
Generating New Keys
On your computer, you'll open your terminal or PowerShell and type a command to create these keys. It usually looks something like `ssh-keygen`. This command will ask you where to save the keys and if you want a passphrase for your private key. A passphrase is a good idea, as a matter of fact, because it adds another layer of protection.
Once you run the command, you'll get two files, like `id_rsa` (your private key) and `id_rsa.pub` (your public key). These are usually stored in a hidden folder called `.ssh` in your user directory. For Windows, this would be something like `C:\Users\YourUsername\.ssh`.
Copying Keys to Your IoT Device
After you have your keys, you need to put the public part on your IoT device. There's a command for this, `ssh-copy-id`, which automates the process. If that's not available, you can copy the contents of your `id_rsa.pub` file manually. For example, in a terminal, you could use `pbcopy < ~/.ssh/id_rsa.pub` to copy the public key to your clipboard.
Then, you'd log into your IoT device using a password for the first time, and paste the key into a file called `authorized_keys` inside the `.ssh` folder of the user you want to connect as. This makes sure that only your computer, with its matching private key, can get in.
Connecting to Your IoT Device: The First Time
With your keys in place, you're ready to make that first secure connection. It's a moment of truth, really, where all your setup work pays off. This step is pretty straightforward, but it's good to know what to expect.
Basic Connection Steps
Open your terminal or PowerShell. Then, you type `ssh username@your_device_ip_address`. Replace `username` with the user account on your IoT device (often `pi` for a Raspberry Pi), and `your_device_ip_address` with the actual network address of your device. If everything is set up right, you should be logged in without needing a password.
You might see a message asking if you want to accept the device's "fingerprint" the very first time you connect. This is normal. Type "yes" to continue. This step helps confirm you're talking to the right device and not some imposter.
Handling Common Connection Snags
Sometimes, things don't go perfectly on the first try. If you get an error, check a few things. Is the IP address correct? Is SSH enabled on your IoT device? Are your keys in the right place on both your computer and the device? It's usually a small detail that needs fixing.
One common issue, as I was saying, is getting an error about permissions on your private key file. Your private key should only be readable by you. On Linux/macOS, you can fix this with `chmod 400 ~/.ssh/id_rsa`. For Windows, you'd adjust the file permissions through the file properties.
Advanced SSH Tips for IoT Management
Once you're comfortable with basic connections, there are ways to make your life even easier, especially when dealing with multiple devices or specific needs. These tips help you customize your SSH setup.
Using a Config File for Easier Access
Typing the full `ssh username@ip_address` command every time can get old. You can set up a special file, `config`, in your `.ssh` folder to store connection details. This file lets you give your devices short, memorable names. So, for example, instead of typing a long address, you just type `ssh my_iot_sensor`.
To do this, you'll edit or create the file by typing `notepad ~/.ssh/config` in PowerShell for Windows, or `nano ~/.ssh/config` in a Linux/macOS terminal. Inside this file, you'd add entries like this:
Host my_iot_sensor HostName 192.168.1.100 User pi Port 22 IdentityFile ~/.ssh/id_rsa_sensor
This variable sounds like what I am looking for, but it is not defined. This is how you set the host name and port in a config file for Windows, using OpenSSH through PowerShell, just like you would on other systems. The `IdentityFile` line is very useful if you use different keys for different devices, which is a good security practice.
Managing Multiple SSH Keys
As your collection of IoT devices grows, you might want to use different SSH keys for different purposes. For instance, you might have one key for your home automation devices and another for your workshop gadgets. This adds another layer of security. So, I mean, if one key gets into the wrong hands, only a small part of your setup is at risk.
When you generate new keys, you can give them different names, like `id_rsa_home_iot` or `id_rsa_workshop`. Then, in your `~/.ssh/config` file, you simply point to the correct `IdentityFile` for each `Host` entry. This is how you configure the `.ssh/config` file under Windows, that it works with a usual Git server or any other SSH connection that needs a specific key.
I added an SSH key to the Google Cloud Platform VM, and it picked the username and saved the key under it, while I thought it was merely a metadata key, and was attempting to connect with the wrong user. This highlights why naming your keys clearly and specifying them in your config file is so helpful. The documentation is not clear on how to explicitly use only that key, sometimes, so the config file becomes your best friend.
Forwarding X11 Connections for Graphical Apps
Sometimes, your IoT device might be running a program with a graphical interface that you want to see on your computer screen. SSH can forward these graphical displays using something called X11 forwarding. This lets you run an application on the remote device and have its window pop up on your local desktop.
To enable this, you usually add `-X` to your SSH command: `ssh -X username@your_device_ip_address`. If you run ssh and display is not set, it means ssh is not forwarding the X11 connection. To confirm that ssh is forwarding X11, check for a line containing "requesting X11 forwarding" in the output of your connection attempt, often when you add `-v` for verbose output.
SFTP and Windows Explorer: A Quick Note
I require one of my clients to connect to an SFTP server using Windows File Explorer. The explorer has an option to connect to an FTP server but not an SFTP server directly. This is a common point of confusion. Windows File Explorer doesn't natively support SFTP connections in the same way it does for FTP.
For SFTP, which uses SSH for secure file transfers, you'll typically need a dedicated SFTP client like WinSCP or FileZilla. These programs provide a graphical interface for moving files securely between your Windows computer and your IoT device, using your SSH keys for authentication. Here is what my dashboard looks like when trying to connect to an SFTP server, and it's not really sure where to add an SSH key in Windows Explorer itself.
Keeping Your IoT Connections Safe
Security isn't a one-time setup; it's an ongoing process. Always use strong passphrases for your SSH keys. Keep your private keys absolutely secret and never share them. Regularly update the software on both your computer and your IoT devices to patch any security weaknesses. It's a pretty big deal to stay on top of this.
Consider disabling password-based SSH logins on your IoT devices once you have key-based authentication working. This makes it so only people with your specific SSH key can get in, which is much safer. Also, limit the user accounts on your IoT devices to only what's needed. Less access means less risk, basically.
For more on general network security, you might want to look at this guide on network security. It offers broader insights that can help keep your entire home or business network safer, which, you know, includes your IoT gadgets.
Frequently Asked Questions About SSH and IoT
Here are some common questions people have when setting up SSH for their smart devices:
What if I lose my SSH private key?
If you lose your private key, you won't be able to connect to devices that only have its public counterpart. You'll need to generate a new key pair and then add the new public key to all your IoT devices. It's a bit of a hassle, so keep your private key safe and perhaps backed up in a very secure way.
Can I use SSH to access my IoT device from outside my home network?
Yes, you can, but it needs more setup. You'll likely need to configure port forwarding on your home router to send SSH traffic to your IoT device's local IP address. This can be a security risk if not done carefully, so consider using a VPN or a cloud-based service for more secure remote access.
Why am I getting "Permission denied (publickey)" when connecting?
This error usually means your SSH client tried to use your private key, but the IoT device didn't accept it. Common reasons include the public key not being correctly placed in the `authorized_keys` file on the device, incorrect file permissions on the `authorized_keys` file (it should be `600` or `rw-------`), or the private key on your computer having incorrect permissions. It could also mean you're trying to connect with the wrong username for that specific key.
Learn more about secure connections on our site, and link to this page IoT Security Best Practices.
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know