SSH Raspberry Pi IoT Tutorial: Connecting Your Smart Devices Securely
Ever wondered how to truly take control of your Raspberry Pi projects, especially when they are tucked away in some corner, perhaps running a smart home gadget or a sensor network? Well, getting connected remotely is a very big piece of that puzzle. This guide is all about showing you how to use SSH, which is a really neat way to talk to your Raspberry Pi from another computer, wherever you happen to be. It's pretty much the go-to method for managing those little computers without needing a screen or keyboard hooked up directly.
You see, for anyone building Internet of Things (IoT) things with a Raspberry Pi, remote access is a total must-have. Whether you are checking on a garden watering system, adjusting a home automation setup, or just doing some quick updates, SSH lets you do it all from afar. It keeps your connection safe and sound, too, which is a rather good thing when you are dealing with your home network or even something out in the wild, so to speak.
Right now, as of early 2024, more and more people are putting these small, capable computers into all sorts of smart devices. Knowing how to use SSH effectively is, in a way, like having a secret key to your digital kingdom. This tutorial will walk you through the steps, making sure you feel pretty comfortable with getting your Pi online and under your command, using methods that are both easy to grasp and very secure.
Table of Contents
- Setting Up Your Raspberry Pi for SSH
- Connecting to Your Raspberry Pi via SSH
- Making SSH More Secure with Key-Based Authentication
- Advanced SSH Tricks for IoT Projects
- Troubleshooting Common SSH Issues
- Frequently Asked Questions about SSH Raspberry Pi IoT Tutorial
- Conclusion
Setting Up Your Raspberry Pi for SSH
Before you can start talking to your Raspberry Pi through SSH, you have to get it ready. This usually means making sure the operating system is on there and that SSH itself is turned on. It's a pretty straightforward process, actually.
Initial Pi Setup
First off, you need to get Raspberry Pi OS onto your Pi. You can use the Raspberry Pi Imager tool, which is pretty handy for this. Just pick your Pi model, choose the operating system, and then select your SD card. It does most of the hard work for you, so it's almost like magic.
Once the operating system is on the SD card, put it into your Raspberry Pi. Connect a screen, keyboard, and mouse for this first boot. Go through the initial setup steps, like setting your country, language, and a new password. The default username is usually 'pi', so you will want to remember that, too.
Enabling SSH
By default, SSH might not be turned on, especially with newer versions of Raspberry Pi OS. There are a few ways to get it going. One common way is through the Raspberry Pi Configuration tool, which you can find in the Preferences menu. Just open it up, go to the 'Interfaces' tab, and make sure SSH is set to 'Enabled'. That's one simple way, anyway.
Another way, if you are setting up a headless Pi (meaning no screen), is to create an empty file named 'ssh' (no extension) in the boot partition of your SD card before you put it into the Pi. When the Pi boots up, it sees that file and turns SSH on automatically. This is quite useful for IoT projects where you might not have a display readily available, so it really helps.
Finding Your Pi's IP Address
To connect to your Pi, you need to know its IP address on your network. If you have a screen hooked up, you can open a terminal window on the Pi and type `hostname -I`. This command will show you the IP address, which is generally what you are looking for. It's a quick way to get that bit of information.
If your Pi is running headless, you can often find its IP address by checking your router's connected devices list. Many routers have a web interface where you can see all the devices currently on your network. Look for something named 'raspberrypi' or a similar hostname. Sometimes, you can also use network scanning tools on your computer, like `nmap`, to find devices on your network, which is pretty neat.
Connecting to Your Raspberry Pi via SSH
Once your Raspberry Pi has SSH enabled and you know its IP address, you are ready to make that first connection. The way you do this depends a little on what kind of computer you are using to connect from.
From Linux/macOS
Connecting from a Linux or macOS computer is quite straightforward because these operating systems come with SSH built-in. Just open up your terminal application. Then, you can type a simple command to connect. For example, if your Pi's IP address is `192.168.1.100` and the username is `pi`, you would type `ssh pi@192.168.1.100`. It's really that simple, you know.
The first time you connect to a new Pi, your computer will ask if you want to accept the host's key. You should type 'yes' to this. After that, it will ask for the password for the 'pi' user. Type that in, and if all goes well, you will be logged into your Raspberry Pi's command line. It's a rather satisfying moment, actually.
From Windows with OpenSSH
Windows 10 and 11 come with OpenSSH client built-in, which is very helpful. You can use PowerShell or Command Prompt. The command is the same as for Linux/macOS: `ssh pi@192.168.1.100`. If you are wondering how to set the host name and port in a config file for Windows, using OpenSSH through PowerShell, it's pretty much the same as on other systems. You will create or edit a file named `config` inside your `.ssh` folder. This file is typically found at `C:\Users\YourUsername\.ssh\config`. We will talk more about this config file later, as a matter of fact.
If you don't have OpenSSH client, you might need to add it through Windows Features. Just search for "Manage optional features" in Windows settings, and then add "OpenSSH Client". This makes connecting from Windows very similar to connecting from other operating systems, which is good for consistency.
Dealing with Host Key Warnings
Sometimes, when you try to connect via SSH, especially if you have changed your Raspberry Pi's operating system or if its IP address has changed, you might get a warning about a "REMOTE HOST IDENTIFICATION HAS CHANGED!" This is a security feature, so it's a good thing. It means the SSH client on your computer sees a different "fingerprint" for the server than it remembered. So, now I'm getting man in the middle attack warnings when I try to use SSH via Windows PowerShell, and it's because the server I frequently log into via SSH has changed its IP address, you see.
To fix this, you need to remove the old, stored key for that IP address from your computer's `known_hosts` file. The warning message itself will usually tell you which line number in the `known_hosts` file to remove. You can open that file with a text editor and delete the line. On Linux/macOS, this file is at `~/.ssh/known_hosts`. On Windows, it's at `C:\Users\YourUsername\.ssh\known_hosts`. After you remove the line, you can try connecting again, and it should ask you to accept the new key, which is what you want.
Making SSH More Secure with Key-Based Authentication
While password-based SSH is okay for getting started, using SSH keys is a much more secure and convenient way to connect. It's highly recommended for any IoT project, really.
Why Use SSH Keys?
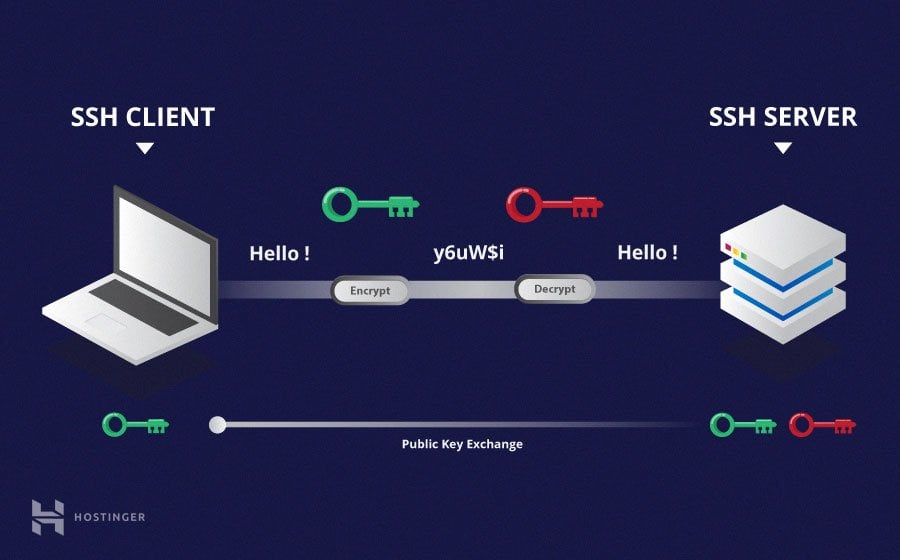
SSH keys work in pairs: a private key that stays on your computer and a public key that goes on your Raspberry Pi. When you try to connect, your computer uses the private key to prove who it is to the Pi, which then checks it against the public key. This is much safer than passwords because keys are very long and complex, so they are incredibly hard to guess. Plus, you do not have to type a password every time, which is rather nice.
Generating SSH Keys
You can make a new SSH key pair using the `ssh-keygen` command in your terminal or PowerShell. Just type `ssh-keygen` and press Enter a few times to accept the default location and no passphrase (though adding a passphrase makes it even more secure). This will create two files in your `~/.ssh` directory: `id_rsa` (your private key) and `id_rsa.pub` (your public key). It's a very standard process.
Copying Your Public Key to the Pi
Once you have your public key, you need to get it onto your Raspberry Pi. The easiest way is with the `ssh-copy-id` command: `ssh-copy-id pi@192.168.1.100`. This command will ask for your Pi's password, and then it will put your public key in the right place on the Pi. It's a pretty handy tool, honestly.
If `ssh-copy-id` is not available, you can copy the public key manually. First, get the public key onto your clipboard. In terminal, enter this command with your SSH file name: `pbcopy < ~/.ssh/id_rsa.pub` (on macOS) or `cat ~/.ssh/id_rsa.pub | clip` (on Windows PowerShell). This will copy the file to your clipboard. Then, SSH into your Pi with your password. Once in, edit or create the file now by typing `nano ~/.ssh/authorized_keys`. Paste your public key into this file, save it, and exit. Make sure the permissions on `~/.ssh` are `700` and on `authorized_keys` are `600` on your Pi. This helps keep things secure, you know.
Using Multiple SSH Keys
Sometimes, you might want to use different SSH keys for different purposes. For example, you might have one key for personal projects and another for work. So, now I want to use multiple SSH keys (so my key will get the name `id_rsa_test`), and I need to configure the `.ssh/config` file under Windows so that it works with a usual Git server. The documentation is not clear on how to explicitly use only that key, but the config file makes it pretty clear, in a way.
You can tell SSH which key to use for specific connections by adding entries to your `~/.ssh/config` file. For example:
Host my-git-server Hostname git.example.com User git IdentityFile ~/.ssh/id_rsa_test Host my-raspberry-pi Hostname 192.168.1.100 User pi IdentityFile ~/.ssh/id_rsa_pi With this setup, you can simply type `ssh my-git-server` or `ssh my-raspberry-pi`, and SSH will automatically use the correct key. This makes managing different connections very easy, and it's rather convenient.
SSH Keys on Cloud Platforms
When you are working with cloud virtual machines (VMs) for your IoT backend, like Google Cloud Platform or AWS, adding SSH keys is a common practice. I added an SSH key to the Google Cloud Platform VM, and it picked the username and saved the key under it, while I thought it was merely a metadata key, and was attempting to connect with the default user. This can be a bit confusing at first. Generally, cloud providers associate your public key with a specific username on the VM. Here is what my dashboard looks like, and I am not really sure where to add an SSH key, but usually, there is a dedicated section for SSH keys or metadata when you create or edit a VM instance. This is a very important step for secure cloud connections.
Always check your cloud provider's specific instructions for adding SSH keys. They often have a dedicated spot in their web console for this. Once added, you can connect to your cloud VM just like you would to your Raspberry Pi, using the associated username and your private key. It's a pretty standard approach across different cloud services.
Advanced SSH Tricks for IoT Projects
SSH can do much more than just log you into a remote shell. There are some really powerful features that are quite useful for IoT development and management.
SSH Configuration File (.ssh/config)
The `~/.ssh/config` file is your friend for making SSH connections simpler and more consistent. As mentioned earlier, you can set hostnames, usernames, and specific identity files. How do I set the host name and port in a config file for Windows, using OpenSSH through PowerShell? You do it in this very file. Edit or create the file now by typing `notepad C:\Users\YourUsername\.ssh\config` in PowerShell, or `nano ~/.ssh/config` on Linux/macOS. This file lets you define shortcuts and specific settings for each of your remote machines, which is incredibly handy.
For example, if your Raspberry Pi is on a non-standard port or has a long IP address, you can simplify it:
Host mypi Hostname 192.168.1.100 User pi Port 2222 Now, instead of typing `ssh -p 2222 pi@192.168.1.100`, you can just type `ssh mypi`. This makes your life a bit easier, honestly, especially with many devices.
SSH from Server to Server
Sometimes, your IoT setup might involve multiple Raspberry Pis or a Pi talking to another server. However, I would be creating a bash script from server 1 that will execute some commands on server 2 via SSH. How do I SSH to server 2 using my private key file from server 1? This is a very common scenario, you know.
To do this, you need to make sure the private key for server 2 is available on server 1. You can copy the private key file to server 1, but make sure its permissions are set correctly (e.g., `chmod 600 ~/.ssh/id_rsa_server2`). Then, in your bash script on server 1, you can use the `-i` option to specify the private key:
ssh -i ~/.ssh/id_rsa_server2 user@server2_ip "command_to_execute" This lets you automate tasks between your devices, which is pretty powerful for a complex IoT system, so it really helps.
X11 Forwarding for Graphical Apps
If you have a graphical application running on your Raspberry Pi that you want to see on your desktop computer, SSH can help with something called X11 forwarding. This means the graphical output from the Pi gets sent over the SSH connection to your display. If you run SSH and display is not set, it means SSH is not forwarding the X11 connection, which can be a bit frustrating.
To enable X11 forwarding, you add the `-X` option to your SSH command: `ssh -X pi@192.168.1.100`. To confirm that SSH is forwarding X11, check for a line containing "requesting X11 forwarding" in the output of your SSH connection, especially if you run it with verbose output (`ssh -v -X`). You will also need an X server running on your local computer (like XQuartz for macOS or VcXsrv for Windows). This is quite useful for debugging graphical interfaces on your Pi without a direct monitor, so it's a very neat trick.
Understanding SSH Algorithms
SSH uses various algorithms for key exchange (kexalgorithms), ciphers (for encryption), and MACs (for integrity checking). Is there a way to make SSH output what MACs, ciphers, and kexalgorithms that it supports? I'd like to find out dynamically instead of having to look at the source. Openssh 5.7 introduced the kexalgorithms option, and you can add a kexalgorithms knob to the client and server configuration to allow selection of which key exchange methods are used. This is important for security and compatibility, you know.
You can see what your SSH client supports by running `ssh -Q key` for key exchange algorithms, `ssh -Q cipher` for ciphers, and `ssh -Q mac` for MACs. If you need to specify a particular algorithm for a connection, you can do so in your `~/.ssh/config` file or directly on the command line. For example,
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know