What Is SSH In IoT? Protecting Your Connected Gadgets
Think about all the smart gadgets around us today. From tiny sensors watching over our homes to complex industrial machines, these devices are always talking to each other and to the internet. Keeping these conversations private and safe is, you know, a very big deal. Without proper security, someone could listen in, mess with our devices, or even take control of them. This is where a helpful tool called SSH steps in, especially for the many small computers that make up the Internet of Things, or IoT.
Securing these little devices can feel a bit tricky, almost like trying to put a big lock on a very small box. They often have limited power and storage, which means traditional security methods might be too heavy for them. Yet, the need for strong protection remains. SSH offers a way to connect to these gadgets remotely, making sure that whatever information goes back and forth stays hidden from prying eyes. It's a bit like having a secret, coded pathway directly to your device, which is rather neat.
Understanding what SSH is and how it helps with IoT security can really make a difference for anyone who uses or works with connected devices. It provides a reliable way to manage and update these gadgets from afar, all while keeping things safe. So, we'll explore just what SSH brings to the world of IoT, and why it's so important for keeping our smart things, well, smart and secure.
Table of Contents
- What Exactly is SSH?
- Why IoT Devices Really Need SSH
- How SSH Keeps Your IoT Devices Safe
- Everyday Uses for SSH in IoT
- Setting Up SSH on Your IoT Gadgets
- Handling SSH Keys for Better IoT Security
- Common Hurdles When Using SSH with IoT
- The Future of SSH and IoT Security
- Frequently Asked Questions About SSH in IoT
- Wrapping Things Up
What Exactly is SSH?
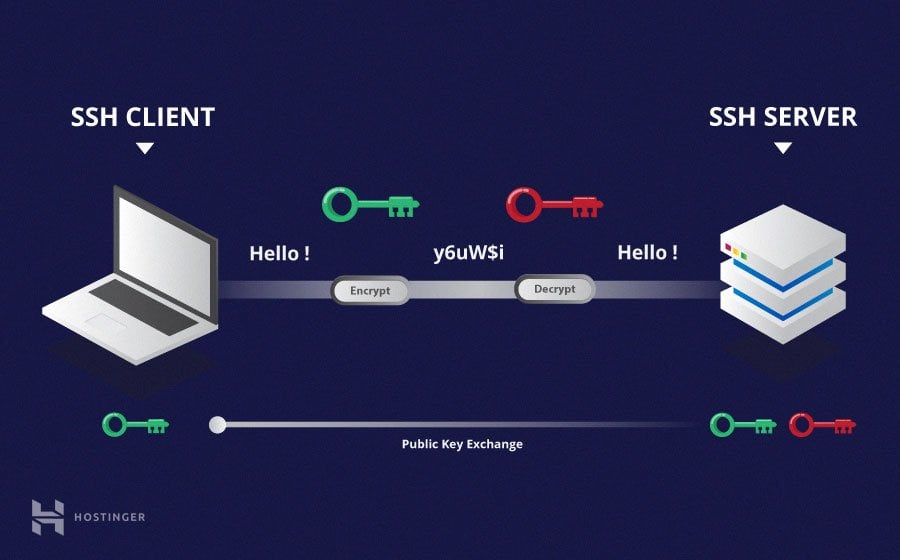
SSH, which stands for Secure Shell, is a network protocol. It allows you to connect to a computer or device over an unsecured network, but it does so in a way that is very secure. Think of it as a super-strong, encrypted tunnel that you can use to send commands and data. This tunnel makes sure that no one can peek at what you are doing or change the information you are sending. It's been around for a while, and it's trusted by many for remote access, which is why it's so useful for IoT devices, too.
When you use SSH, you're not just sending information out into the open. Instead, everything you send is scrambled up, or encrypted, before it leaves your computer. Then, on the other side, the receiving device unscrambles it. This way, even if someone intercepts the data, it will just look like a jumble of characters, completely meaningless to them. This level of protection is, honestly, a pretty big deal for anything connected to the internet.
The main idea behind SSH is to provide a safe way to control a remote computer or transfer files without worrying about security breaches. It replaces older, less secure methods like Telnet or FTP, which sent information in plain text, making it easy for others to read. So, in some respects, SSH is like a digital bodyguard for your data, making sure it gets where it needs to go without any trouble.
Why IoT Devices Really Need SSH
IoT devices are often placed in many different locations, sometimes far from where you are. Imagine trying to update the software on a smart sensor that is located across town or even in another country. Physically going to each device would be, well, nearly impossible and very time-consuming. This is where the ability to connect remotely becomes absolutely essential for managing these gadgets.
Beyond just convenience, security is a really big reason why IoT devices need SSH. Many IoT gadgets collect sensitive information, like video from security cameras, health data from wearables, or energy usage from smart meters. If this data were to fall into the wrong hands, it could lead to serious privacy problems or even physical harm. So, keeping that information safe during transmission is, frankly, paramount.
Also, IoT devices are often targets for cyber attacks. If a hacker can get into one device, they might be able to use it as a stepping stone to get into your entire network. SSH helps prevent this by providing a strong barrier against unauthorized access. It's a way to ensure that only authorized people can connect to and control these devices, which is, obviously, a good thing for everyone.
How SSH Keeps Your IoT Devices Safe
SSH works by setting up a secure channel between two devices. When you connect to an IoT device using SSH, a special handshake happens first. This handshake makes sure that both sides can trust each other and agree on how they will scramble and unscramble their messages. This process involves a couple of key steps that really help keep things private and secure.
Keeping Data Secret with Encryption
One of the most important things SSH does is encrypt all the data that passes through its connection. This means that every command you send, every piece of information your device sends back, gets turned into a secret code. If someone were to intercept this coded message, it would look like gibberish. They wouldn't be able to understand it without the right key, which is pretty clever, you know.
This encryption applies to everything. Whether you are typing commands into a terminal, transferring a file, or even just checking the device's status, it's all protected. This is a huge improvement over older methods where data was sent in plain text, like writing a postcard for everyone to read. With SSH, it's more like sending a sealed letter in a locked box, which is a much safer way to do things.
Making Sure It's Really You: Authentication
Another crucial part of SSH is authentication. This is how SSH makes sure that the person trying to connect is actually who they say they are. There are a few ways this can happen. One common method is using a password, but a much stronger way is with something called SSH keys. SSH keys are like a digital lock and key pair, where one part stays with you and the other part goes on the device.
When you use SSH keys, you create two parts: a public key and a private key. You put the public key on your IoT device. Your private key stays safely on your computer. When you try to connect, your computer uses your private key to prove its identity to the IoT device. The device then checks this against the public key it has. If they match, the connection is allowed. This method is much more secure than passwords, which can be guessed or stolen. As a matter of fact, many people prefer this method for sensitive devices.
Everyday Uses for SSH in IoT
SSH isn't just for super technical people; it has many practical uses that make managing IoT devices much simpler and safer. From checking on a device from your living room to updating its software, SSH provides the tools you need. It's a very versatile tool, you see.
Getting to Your IoT Device from Anywhere
Perhaps the most common use of SSH in IoT is for remote access. This means you can connect to your smart device from another computer, no matter where you are, as long as both devices have internet access. You can then use a command-line interface to control the device, just as if you were sitting right in front of it. This is incredibly handy for devices that are installed in hard-to-reach places or spread out over a large area.
For example, if you have a Raspberry Pi acting as a smart home hub, you can use SSH to log in and check its status, restart services, or change settings without ever touching the Pi itself. It's also how you'd typically connect to a cloud platform's virtual machine that hosts IoT services. I mean, it's pretty much standard practice. One might find that when adding an SSH key to a Google Cloud Platform VM, for instance, it often picks up the username and saves the key under it, even if you thought it was just a metadata key, and you were attempting to connect with it in a different way.
Moving Files Safely: SFTP and SCP
SSH also provides secure ways to move files between your computer and an IoT device. These methods are called SFTP (SSH File Transfer Protocol) and SCP (Secure Copy Protocol). Unlike old FTP, which sent files in the clear, SFTP and SCP use SSH's encryption to protect your data during transfer. This is very important when you need to send sensitive configuration files or software updates to your devices.
Sometimes, a client might need to connect to an SFTP server using a Windows file explorer. The explorer might have an option to connect to an FTP server but not an SFTP server, which can be a bit of a snag. In such cases, dedicated SFTP clients or command-line tools that leverage SSH are often the way to go. This ensures that any software updates or data logs you move are kept private and safe from interception, which is, obviously, a very good thing.
Creating Secure Tunnels for Other Services
SSH can also create secure "tunnels" for other types of network traffic. This is known as SSH tunneling or port forwarding. It means you can take an insecure connection or service and send its data through the encrypted SSH tunnel, making it secure. For example, if you have a web interface on your IoT device that isn't encrypted, you could use an SSH tunnel to access it securely through your browser.
This is also how SSH can forward graphical interfaces. If you run SSH and the display is not set, it means SSH is not forwarding the X11 connection, which is needed for graphical applications. To confirm that SSH is forwarding X11, you would check for a line containing "requesting X11 forwarding" in the output of your SSH connection. This capability allows you to run graphical applications from your IoT device and see them on your local computer, all while the connection remains completely secure. It's a pretty neat trick for certain tasks.
Setting Up SSH on Your IoT Gadgets
Getting SSH up and running on an IoT device, like a Raspberry Pi, is usually a straightforward process. Many devices come with SSH capabilities built-in, or you can add them easily. The first step is often to enable the SSH service on the device itself. This might involve a simple command or changing a setting in a configuration menu. It's often one of the first things people do when setting up a new IoT project, you know.
Once SSH is enabled, you'll need to know the device's network address, its hostname, or its IP address. This is how your computer will find the device on the network. Then, from your computer, you use an SSH client (like OpenSSH on Windows through PowerShell, or the terminal on Linux/macOS) to connect. You might wonder, for instance, "How do I set the host name and port in a config file for Windows, using OpenSSH through PowerShell?" This is where configuration files become very useful.
You can often create or edit a configuration file in your SSH folder (like `.ssh/config` on Windows or Linux). This file lets you save connection details for different devices, so you don't have to type them out every time. For example, you might type `Host myiotdevice` and then `Hostname 192.168.1.100` and `User pi` to make connecting simpler. You just edit or create the file now by typing the necessary lines. This variable sounds like what I am looking for, but it is not always defined in a straightforward way, so you might need to look up the exact syntax for your setup. It really helps to streamline your workflow, especially if you have many devices to manage.
Handling SSH Keys for Better IoT Security
Using SSH keys instead of passwords for authentication is a much safer way to connect to your IoT devices. Keys are much harder to guess or crack than even very complex passwords. This is because they are long, random strings of characters, and they work in pairs, as we discussed earlier. It's a pretty strong security measure, honestly.
To use SSH keys, you first generate a pair on your computer. Then, you copy the public part of the key to your IoT device. When you try to connect, your computer uses the private part of the key to prove who it is. The device checks this against the public key it has. If they match, you're in. It's a very simple yet effective system.
Sometimes, you might need to add your public key to a service or platform. For example, in a terminal, you might enter a command like `pbcopy < ~/.ssh/id_rsa.pub` to copy your SSH file name to your clipboard. Then, you open your GitHub account, go to settings, then "SSH and GPG keys," and paste it there. This allows you to securely interact with services like Git servers. If you want to use multiple SSH keys, perhaps one named `id_rsa_test`, you'd configure your `.ssh/config` file under Windows to work with a usual Git server by adding specific host entries for each key. This allows for a lot of flexibility and security, which is, you know, very helpful.
Common Hurdles When Using SSH with IoT
While SSH is a powerful tool, setting it up and managing it on IoT devices can sometimes present a few challenges. One common issue is simply making sure the device is reachable on the network. Sometimes, firewall settings or network configurations can block SSH connections, making it seem like the device isn't responding. This can be a bit frustrating, you know, when you're trying to connect.
Another challenge comes with managing SSH keys, especially if you have many devices or different users. Keeping track of which keys are on which devices, and making sure private keys are kept secure, requires a bit of organization. You might find yourself saying, "Not really sure where to add an SSH key" if you're dealing with a new system or platform. This can be particularly true when working with cloud services, where the key might be picked up by the username and saved under it, even if you thought it was merely a metadata key and were attempting to connect with a different setup.
Also, the limited resources of some very small IoT devices can sometimes affect SSH performance. While SSH itself is quite efficient, running many background processes or dealing with very slow network connections can make remote management feel sluggish. Plus, some users might expect a graphical interface, but SSH often defaults to a command-line experience. This variable sounds like what I am looking for, but it is not defined in a way that provides a graphical output, which can be a point of confusion for those used to visual dashboards. Despite these minor hurdles, the benefits of SSH for security and remote management usually outweigh the setup effort.
The Future of SSH and IoT Security
As the number of IoT devices continues to grow, the importance of secure communication methods like SSH will only increase. We're seeing more and more devices being designed with security in mind from the very beginning, and SSH is often a core part of that design. This means it will likely remain a standard tool for developers and administrators working with connected gadgets. It's pretty much a given, honestly.
New developments in SSH might focus on even more efficient ways to handle connections for devices with very limited power, or on making key management even simpler for large-scale IoT deployments. There's also a constant effort to improve the underlying encryption methods to stay ahead of new threats. So, in some respects, SSH is always evolving to meet the demands of the changing digital world. This ongoing development means that SSH will likely continue to be a cornerstone of secure IoT communication for many years to come.
The trend towards "zero-trust" security models, where no device or user is automatically trusted, also aligns well with SSH's strong authentication principles. This means that every connection, every time, is verified, which adds an extra layer of safety. This approach, you know, is becoming increasingly popular in all areas of cybersecurity, and IoT is no exception. Learn more about secure connections on our site.
Frequently Asked Questions About SSH in IoT
What makes SSH more secure than older methods for IoT?
SSH uses strong encryption to scramble all data sent between your computer and the IoT device, making it unreadable to anyone who might intercept it. It also uses robust authentication methods, like SSH keys, to make sure only authorized users can connect. Older methods, like Telnet or FTP, often send information in plain text, which is very easy for others to see and steal. This makes SSH a much safer choice for sensitive IoT data, which is, obviously, a good thing.
Can I use SSH to control my smart home devices?
Yes, absolutely! If your smart home device, like a Raspberry Pi or a custom-built gadget, runs an operating system that supports SSH, you can definitely use it to control the device remotely. You can issue commands, check its status, update its software, or even transfer files. This is particularly useful for more advanced smart home setups where you might want to automate tasks or troubleshoot issues without being physically present with the device. It's a very powerful way to manage your home tech, honestly.
Is SSH hard to set up for beginners in IoT?
For basic use, setting up SSH on many popular IoT platforms, like the Raspberry Pi, is fairly straightforward and there are many guides available. You just enable it, get the device's address, and connect. However, some advanced features, like X11 forwarding or setting up complex configuration files for multiple keys, might require a little more learning. For instance, if you're not sure where to add an SSH key, or how to configure the `.ssh/config` file under Windows for multiple keys, it might take a bit of searching. But the core functionality is generally quite accessible, and the benefits for security are well worth the effort, which is, you know, true.
Wrapping Things Up
SSH provides a vital layer of security and convenience for managing the growing number of IoT devices around us. From ensuring that sensitive data remains private to allowing remote control and updates, its role is, frankly, indispensable. By understanding how SSH works and applying its principles, we can help keep our connected gadgets and the information they handle safe from unwanted access. It really helps to create a more secure digital environment for everyone. You can learn more about device security on our site.
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know