Securely Connect Remote IoT Devices With P2P SSH On Ubuntu Server
Connecting to your remote devices, especially those little IoT gadgets out in the field, can feel a bit like trying to talk to someone across a noisy room. You want to make sure your messages get through clearly and, perhaps more importantly, that no one else is listening in. For many folks with smart home tech, industrial sensors, or even just a Raspberry Pi doing cool things far away, keeping those connections private and safe is a big deal. It's really about making sure your digital conversations stay just between you and your machines, without any unwelcome guests.
The idea of having your device at risk because it's out of date or missing important security checks is a worry for anyone. Just like you want your computer to run more securely, those small internet-connected things need the same kind of careful attention. It's about getting everything back on track so your whole setup can operate with more peace of mind, allowing you to manage things from afar without feeling exposed.
Sometimes, you might see a message like "This connection is untrusted... we can't confirm that your connection is secure." That feeling of not trusting a link, even when you're just trying to do something simple, is a common frustration. This guide will show you a good way to get around those worries for your remote IoT devices, using a well-known method to make sure your connections are truly private and safe.
Table of Contents
- Why Secure IoT Connections Matter
- What is P2P SSH for IoT?
- Setting Up Your Ubuntu IoT Server
- Making P2P Connections Happen
- Extra Security Steps for Your IoT Setup
- Frequently Asked Questions About Secure IoT Connections
- Making Your IoT Connections Rock Solid
Why Secure IoT Connections Matter
The Challenge of Remote IoT
Imagine you have a small device, perhaps a temperature sensor or a camera, sitting in a far-off place. You need to check on it, maybe update its settings, or just see what it's doing. This is where the idea of securely connecting remote IoT p2p ssh ubuntu server comes into play. It's not always easy to get to these devices directly, especially if they are behind a tricky network or don't have a public address. This makes managing them a real puzzle, so you want a simple yet strong way to reach them.
Many times, these little gadgets are running a version of Linux, and Ubuntu Server is a common choice for them because it's light and reliable. Getting into these devices from your home computer or office, without leaving them open to just anyone, is the main goal. This is where a clever approach can make all the difference, giving you the control you need.
Common Security Worries
One big worry, and it's a very real one, is that your connection might be untrusted. You ask to connect securely, but there's no way to confirm it's truly safe. This can happen with various online services, as many people have found, leading to messages like "There is a problem connecting securely to this website." It's a sign that the basic way you're trying to link up might not be enough.
Another concern is that your devices might be out of date, missing important security and quality updates. This is a common issue that puts your whole setup at risk. We've all seen warnings about devices being vulnerable, and that applies just as much to your IoT gadgets. Keeping them current is part of a good security plan, and a secure connection helps with that.
Also, there's the privacy aspect. As community support specialists, we know privacy and security protocols are very important. We can't just access your account details. This highlights why you need a connection method that keeps your data truly private, so only you can see what's going on with your devices.
What is P2P SSH for IoT?
SSH: A Familiar Friend
SSH, or Secure Shell, is a very useful tool that many people know. It helps you get into a computer or server from a distance, and it does so in a way that keeps your information private. Think of it like a secure tunnel for your commands and data. When you use SSH, everything you send back and forth is scrambled, so anyone trying to peek in just sees a jumble of letters and numbers.
It's a standard way to manage Linux machines, including those running Ubuntu Server. This method is trusted for its ability to keep things secret and make sure the right people are connecting. It's the building block for what we want to do, and it's actually pretty simple to get started with.
P2P: The Direct Approach
P2P stands for "peer-to-peer," and it means connecting directly from one device to another without a central hub always in the middle. When you combine this with SSH, you're looking at a way to make a direct, secure path between your computer and your remote IoT device. This is especially handy when your IoT device is behind a network that makes it hard to reach from the outside.
Instead of trying to open up holes in your network or set up complicated forwarding rules, P2P SSH often uses a clever trick called a reverse tunnel. This allows the remote device, the IoT gadget, to initiate the connection out to a middle server you control. Then, you can connect to that middle server, and it sends you through to your IoT device. It's a bit like the IoT device calling you, then you can talk back to it through that call.
This approach is particularly good for IoT because these devices often have limited resources and might be on networks you don't control, like cellular data or public Wi-Fi. A P2P SSH setup helps you get around those common hurdles, making remote management much more straightforward.
Setting Up Your Ubuntu IoT Server
Preparing Your Ubuntu Device
First things first, your Ubuntu-based IoT device needs to be ready. This means having Ubuntu Server installed and making sure it's up to date. You can do this by running a couple of simple commands in the terminal. It's like giving your device a fresh start and making sure all its tools are current.
sudo apt update sudo apt upgrade -y This step is really important because it helps prevent issues later on, especially those related to security. An out-of-date system is more likely to have known weaknesses, so getting these updates done is a solid first move.
Installing SSH Server
Most Ubuntu Server installations come with the SSH server already in place, but if yours doesn't, it's easy to add. The package is called `openssh-server`. You can install it with a quick command. This is the piece of software that lets your device listen for incoming SSH connections.
sudo apt install openssh-server -y Once installed, the SSH service usually starts on its own. You can check its status to be sure it's running. This makes sure your IoT device is listening for your secure connection attempts, which is pretty vital.
sudo systemctl status ssh Key-Based Authentication: The Best Way
Using passwords for SSH is okay, but it's not the strongest method. The very best way to secure your SSH connections is with something called key-based authentication. This involves creating a pair of digital keys: a public key and a private key. You put the public key on your IoT device, and you keep the private key safe on your local computer.
When you try to connect, your local computer uses its private key to prove who it is to the IoT device. The IoT device checks this against the public key it has. If they match, you're in, without needing to type a password. This is much more secure because private keys are very hard to guess, unlike passwords.
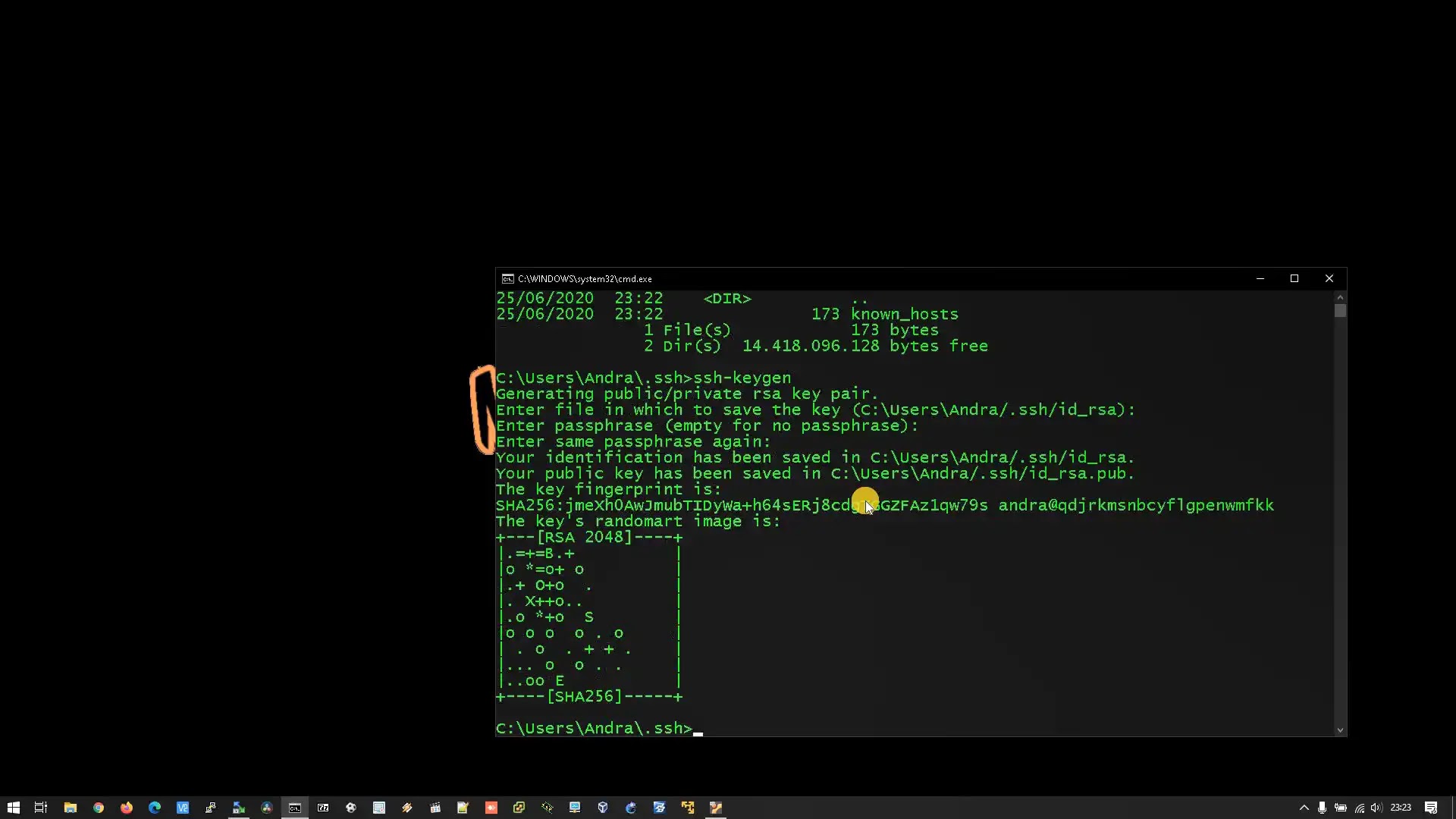
Here's how you generate a key pair on your local machine:
ssh-keygen -t rsa -b 4096 Follow the prompts, and you can choose to add a passphrase for extra security on your private key. This is a good idea. Then, you need to copy your public key (which usually ends in `.pub`) to your IoT device. The `ssh-copy-id` command makes this easy:
ssh-copy-id username@your_iot_device_ip Replace `username` with the user account on your IoT device and `your_iot_device_ip` with its IP address. This command will ask for your password one last time, then it sets up the key for you. After this, you should be able to connect using just your key, which is a much safer way.
Making P2P Connections Happen
Understanding Reverse SSH Tunnels
A reverse SSH tunnel is the clever trick that makes P2P SSH work for remote IoT devices, especially when they are behind a firewall or NAT that you can't easily change. Instead of you connecting *to* the IoT device directly, the IoT device connects *out* to a middle server you control. This middle server needs a public IP address so it can be reached from anywhere.
Once the IoT device makes this outgoing connection to your middle server, it creates a tunnel. You can then connect to a specific port on your middle server, and that connection will be forwarded through the tunnel directly to your IoT device. It's like the IoT device sets up a secret backdoor for you on your own server. This means you don't need to open any ports on the IoT device's local network, which is a big security plus.
This method is very useful for devices that are on networks you don't manage, like public Wi-Fi or cellular networks. It allows the IoT device to initiate the connection, which is often the only type of connection allowed out from restrictive networks.
Setting Up the Tunnel
To set up the reverse tunnel, you'll run a command on your IoT device. This command tells the IoT device to connect to your middle server and create the tunnel. You'll need the IP address or hostname of your middle server, a port on that middle server that you'll use to connect, and the port on the IoT device you want to reach (usually port 22 for SSH).
Here's what the command on your IoT device might look like:
ssh -N -R 2222:localhost:22 username@your_middle_server_ip Let's break that down:
ssh: The command to start an SSH connection.-N: This means "do not execute a remote command." It just sets up the tunnel.-R 2222:localhost:22: This is the core of the reverse tunnel. It says:2222: The port on your `your_middle_server_ip` that you will connect to.localhost:22: The destination on the IoT device side. `localhost` refers to the IoT device itself, and `22` is its SSH port.
username@your_middle_server_ip: The user and IP address of your middle server.
After running this command on your IoT device, it will establish the tunnel. Then, from your local computer, you can connect to your IoT device through your middle server like this:
ssh -p 2222 username_on_iot_device@your_middle_server_ip Notice you're connecting to `your_middle_server_ip` on port `2222`, but you're using the `username_on_iot_device` because that's who you're actually trying to reach through the tunnel. This setup is actually quite neat.
Keeping the Tunnel Alive
The reverse SSH tunnel, by default, will close if the connection drops or if there's no activity for a while. For a remote IoT device that needs to be reachable all the time, this isn't ideal. You need a way to keep the tunnel running constantly.
One common way to do this is to use a tool like `autossh`. `autossh` is designed to monitor an SSH connection and restart it if it drops. It's much better than just running the `ssh` command in a loop.
First, install `autossh` on your IoT device:
sudo apt install autossh -y Then, you can use `autossh` to create the tunnel. It takes similar arguments to `ssh`, but it adds a monitoring port to check the connection.
autossh -M 0 -N -R 2222:localhost:22 username@your_middle_server_ip -o "ServerAliveInterval 60" -o "ServerAliveCountMax 3" The `-M 0` tells `autossh` not to use a separate monitoring port, relying on SSH's built-in keep-alive messages. The `-o "ServerAliveInterval 60"` sends a null packet every 60 seconds to keep the connection alive, and `-o "ServerAliveCountMax 3"` means it will try 3 times before giving up.
To make sure this tunnel starts automatically when your IoT device boots up and runs in the background, you can set it up as a systemd service. This means the tunnel will always try to be open, making your remote IoT device consistently available for your secure connections. You can find many guides online about setting up systemd services, which is a good next step for a robust setup.
Extra Security Steps for Your IoT Setup
Firewall Rules
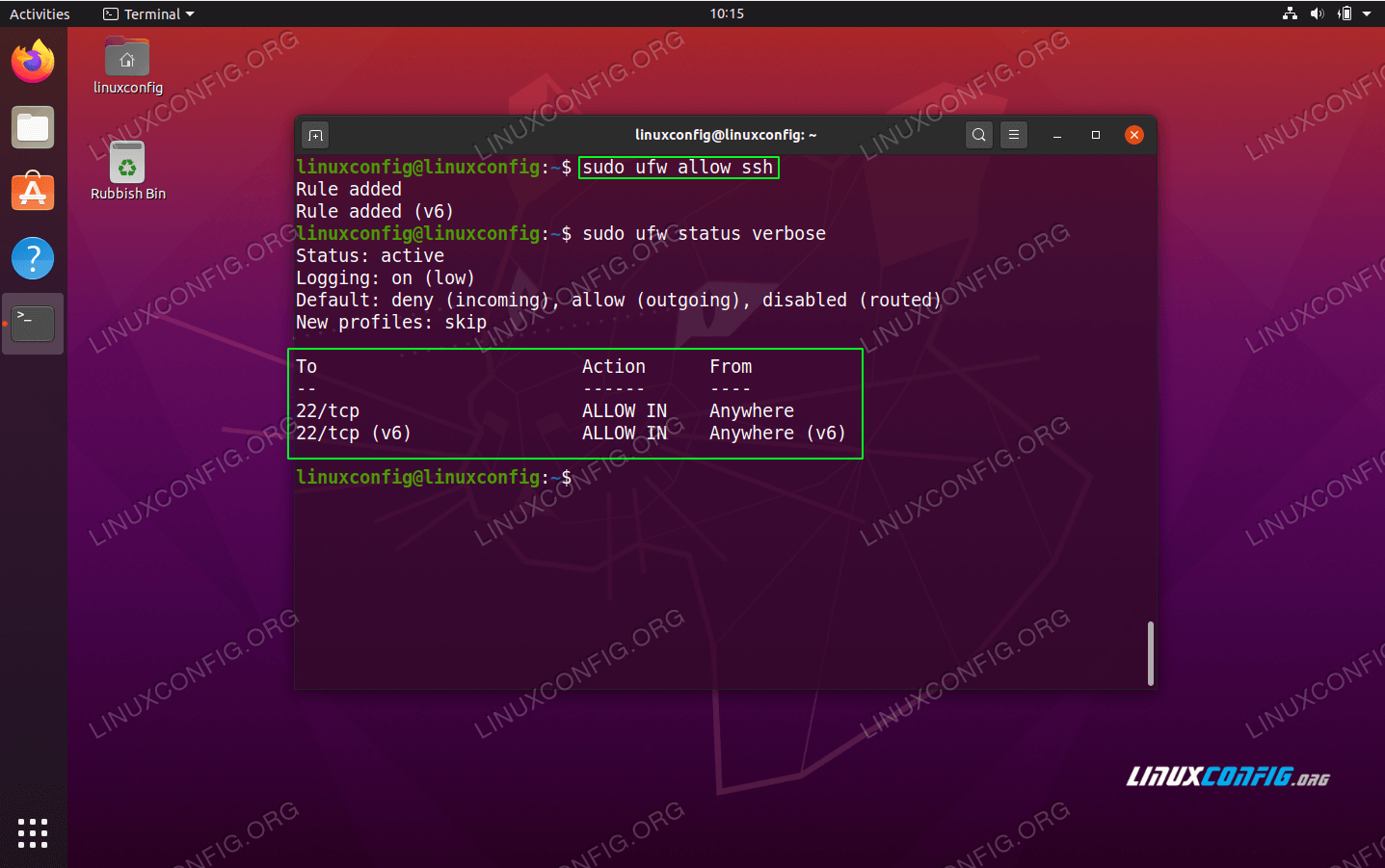
Even with secure SSH, it's a good idea to have a firewall on your Ubuntu IoT device. A firewall acts like a gatekeeper, only allowing specific types of network traffic in or out. For your IoT device, you generally want to block all incoming connections except for those you explicitly allow.
Ubuntu comes with `UFW` (Uncomplicated Firewall), which is easy to use. You can enable it and set rules. For example, if your IoT device is only making outgoing SSH connections for the reverse tunnel, you don't need to open any incoming ports on it for SSH. You might only need to allow outgoing connections to your middle server.
sudo ufw default deny incoming sudo ufw default allow outgoing sudo ufw enable If you need to allow other services on your IoT device, like a web server running on port 80, you would add specific rules for those. But for a P2P SSH setup, keeping incoming connections blocked is a very strong security measure. This helps prevent unwanted access, which is something you really want to avoid.
Regular Updates
Remember that warning about your device being at risk because it's out of date? This is not just a suggestion; it's a critical part of keeping your IoT setup secure. Software gets new versions all the time, and these updates often include fixes for security holes that have been found.
You should regularly update your Ubuntu IoT device. You can do this manually, as mentioned earlier, with `sudo apt update` and `sudo apt upgrade`. For remote devices, you might want to set up automatic updates, but be careful with those to avoid breaking something. A better approach might be to schedule a time to connect via your secure SSH tunnel and run the updates yourself. This way, you stay in control, and your device gets the latest protections.
Keeping your system updated is like putting on fresh, strong armor. It makes it much harder for bad actors to find a way in.
Monitoring Your Connections
Knowing what's happening on your IoT device is another key part of security. You can check who is connected via SSH and what they are doing. Tools like `last` or `w` can show you recent login activity. Looking at your system logs (like `/var/log/auth.log`) can also give you clues about connection attempts, successful or not.
If you see strange login attempts or activity you don't recognize, it's a sign that something might be wrong. Being able to monitor these things, thanks to your secure connection, helps you react quickly if there's a problem. It's a bit like keeping an eye on your front door, even when you're far away.
For more advanced monitoring, you could set up a simple script to alert you if the SSH tunnel goes down or if there are too many failed login attempts. This proactive approach adds another layer of protection to your remote IoT management.
Frequently Asked Questions About Secure IoT Connections
How can I connect to my IoT device if it's behind a strict firewall?
If your IoT device is behind a strict firewall, a reverse SSH tunnel is often the best way. The device makes an outgoing connection to a middle server you control, creating a path back to itself. You then connect to that middle server, and it sends you through to your IoT device. This avoids needing to open incoming ports on the IoT device's local network, which is a big help.
Is SSH key authentication really more secure than passwords?
Yes, absolutely. SSH key authentication is much more secure than using passwords. Keys are very long, complex, and almost impossible to guess. Passwords, even strong ones, can sometimes be cracked or stolen. With keys, you don't send your secret over the network, only a digital signature that proves you have the key. This makes it a far safer way to prove your identity when connecting.
What if my IoT device's internet connection is unreliable?
If your IoT device's internet connection is a bit shaky, the SSH tunnel might drop. To deal with this, you can use a tool like `autossh`. `autossh` is made to watch your SSH connection and automatically restart it if it goes down. This helps keep your remote IoT device reachable even with an unreliable network. You can also use SSH's built-in keep-alive options to help maintain the connection.
Making Your IoT Connections Rock Solid
Setting up a way to securely connect remote IoT P2P SSH Ubuntu server can feel like a big project, but it gives you a lot of control and peace of mind. By using SSH keys, reverse tunnels, and tools like `autossh`, you create a very strong link to your devices. This helps you avoid those frustrating "connection untrusted" messages and keeps your valuable data safe. It's about taking charge of your remote management.
Remember, keeping your systems updated and checking on your connections regularly are just as important as the initial setup. This whole process is a bit like building a very secure digital bridge to your far-off gadgets, allowing you to manage them as if they were right next to you. You can learn more about Ubuntu Server security on their official site, which is a great resource.
This approach means you can keep your remote IoT devices running smoothly and safely, no matter where they are. You can learn more about secure remote access on our site, and link to this page IoT P2P SSH Basics for more detail.
Securely Connect Remote IoT P2P SSH Ubuntu Server: A Comprehensive Guide
Securely Connect Remote IoT P2P SSH Ubuntu Server: A Comprehensive Guide

How To Securely Connect Remote IoT P2P SSH Ubuntu