Securely Connect Remote IoT P2P SSH On Ubuntu: Direct Access, Real Protection
Connecting to your remote Internet of Things (IoT) devices can feel like a tricky business, can't it? You want to check on things, send new instructions, or just make sure everything is running smoothly, but you also need to keep those connections safe from prying eyes. It's a bit like wanting to visit a distant relative's house without leaving the front door wide open for anyone to walk in, you know? This challenge is especially real when we talk about IoT devices, which often hold important data or control physical systems. Keeping them protected is not just a good idea; it's absolutely necessary.
Many people find themselves wondering how to get that direct line to their little computers out in the field without relying on big, central servers or complicated network setups. It's about having control and making sure that the path between you and your device is a private one, free from danger. We're talking about a way to make sure your important device, maybe a sensor or a tiny server, is kept securely, meaning it's in a place where its operations cannot be lost or tampered with, very much like keeping a valuable document in a safe spot.
This article will show you a straightforward path to securely connect remote IoT devices using a peer-to-peer (P2P) SSH method on Ubuntu. We will look at how to set up these connections so they are firm and protected, ensuring the privacy and secrecy of your device's communication. You'll learn the steps to make sure your remote IoT setup is guarded, allowing you to manage it with confidence and peace of mind, so to speak.
Table of Contents
- The Core Challenge: Why Secure Remote IoT Access Matters
- Understanding P2P SSH for IoT on Ubuntu
- Setting Up Your Secure P2P SSH Connection: A Step-by-Step Guide
- Best Practices for Keeping Your IoT Connection Securely Fastened
- Common Hurdles and How to Overcome Them
- Frequently Asked Questions About Secure IoT Connections
- Getting Started with Your Secure IoT Connections
The Core Challenge: Why Secure Remote IoT Access Matters
Remote access to IoT devices is something many people need, whether it's for a home project or a large-scale industrial setup. The ability to check on your devices from anywhere, perhaps thousands of miles away, is incredibly useful. Yet, this convenience comes with a significant responsibility: making sure those connections are safe. Leaving an IoT device exposed on the internet is, in a way, like leaving the door to your house unlocked, just waiting for someone to try and get in.
An insecure connection can lead to all sorts of problems. Someone with bad intentions could gain access to your device, steal information, or even use your device to cause harm to other systems. This is why the idea of connecting securely is so important. It's about protecting your data, your device, and the wider network it might be a part of, too. Think of it as putting a strong lock on that door, keeping everything protected.
The Importance of Keeping Things Securely Guarded
The very meaning of "securely" points to being free from danger, damage, or loss. When we talk about IoT, this means ensuring your devices are protected from unauthorized access. The offices where important work happens are securely guarded, and your IoT devices, which are often doing important work, should be too. This protection is not just about keeping things private; it's about maintaining the integrity and functionality of your entire system, so.
A connection that is securely fastened means it's not loosely put together, so it won't move or be removed easily. This applies to digital connections just as much as it does to physical ones. You want your connection to be firm, giving you confidence that your commands and data are traveling safely between your computer and the remote IoT device. This certificate, the secure connection itself, is an important document, and should be kept securely, meaning in a place where it cannot be lost or stolen, or compromised, really.
Understanding P2P SSH for IoT on Ubuntu
When we talk about securely connecting remote IoT P2P SSH on Ubuntu, we are looking at a specific way of linking up your devices. SSH, or Secure Shell, is a well-known method for getting remote access to a computer, but doing it "peer-to-peer" adds a special twist. It's about creating a direct, private line between two points without needing an intermediary server to manage the connection, which is pretty neat.
This approach gives you a lot of control and can simplify network setups for many people. Instead of opening up ports on your router or setting up complicated VPNs, P2P SSH aims to create a more direct link. It's like having a secret handshake that only your two devices know, allowing them to talk to each other directly and safely, just a little.
What Makes it "Peer-to-Peer"?
A "peer-to-peer" connection means that two devices, or "peers," talk to each other directly. There isn't a central server that acts as a middleman for all the communication. For IoT, this can be very useful. It means less reliance on cloud services, potentially lower costs, and often better privacy because your data isn't passing through a third party's servers. It's a direct line, much like a private conversation between two people, you know.
In the context of SSH, P2P often means using tools or techniques that help two devices behind different firewalls or Network Address Translation (NAT) devices find each other and establish a direct link. This might involve a temporary "hole punching" technique or specialized software that helps coordinate the initial connection. Once the connection is made, the data flows directly between your local machine and your remote Ubuntu IoT device, which is quite clever.
Why Ubuntu for Your IoT Devices?
Ubuntu is a very popular choice for IoT devices, and for good reason. It's a Linux-based operating system that is known for being reliable, having a large community for support, and offering a lot of tools for developers. Ubuntu Core, in particular, is designed specifically for embedded and IoT devices, providing a very secure and stable platform, too. It's pretty much a solid foundation for any smart device you might be building.
The operating system's strong security features and its ease of use make it a great fit for remote IoT deployments. With Ubuntu, you have access to all the standard Linux commands and applications, including SSH, right out of the box. This makes setting up secure connections much simpler than with some other, less feature-rich operating systems, so.
Setting Up Your Secure P2P SSH Connection: A Step-by-Step Guide
Getting your secure P2P SSH connection going on Ubuntu IoT devices involves a few important steps. We'll go through them one by one, making sure each part is handled carefully. The goal is to establish a connection that is firm and protected, ensuring your device's privacy, just like we discussed earlier, really.
Remember, the idea here is to make sure your connection is in a secure manner, free from danger. We want to protect or ensure the privacy or secrecy of your device's line, for example, just like you would protect a telephone line. This means using strong methods to authenticate and encrypt your communication, which is pretty important.
Prerequisites for a Smooth Setup
Before you begin, you'll need a few things in place. First, you need your remote IoT device running Ubuntu, of course. Make sure it's connected to the internet, even if it's behind a firewall or NAT. You also need a local machine, like your laptop or desktop, also connected to the internet, from which you'll initiate the connection. Both devices should have SSH installed, which is usually the case for Ubuntu, you know. If not, you can install it with sudo apt install openssh-server on the IoT device and sudo apt install openssh-client on your local machine, typically.
It's also a good idea to have basic command-line knowledge. You'll be typing commands into a terminal, so being comfortable with that environment helps a lot. Make sure you have administrative access (sudo privileges) on both your local machine and the IoT device, as well. This will allow you to make the necessary system changes, which is quite useful.
Generating SSH Keys (The Secure Way)
Using SSH keys is a much more secure method than relying on passwords alone. It's like having a very unique, complex lock and key system that is nearly impossible for someone else to guess. You'll generate a pair of keys: a private key that stays on your local machine and a public key that you'll put on your IoT device. The private key should be kept securely, meaning it should not be lost or stolen, as it's the key to your access, so.
On your local machine, open a terminal and type:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com"This command creates a new SSH key pair using a strong encryption type (RSA) and a good key length (4096 bits). It will ask you where to save the keys (just press Enter for the default location, usually ~/.ssh/id_rsa) and for a passphrase. A passphrase adds an extra layer of protection to your private key, making it even more secure. Choose a strong, memorable passphrase, by the way. This is very important for keeping your connection protected.
Transferring Your Public Key to the IoT Device
Once you have your key pair, you need to get the public key onto your Ubuntu IoT device. This tells the IoT device that your local machine is allowed to connect. The public key is not sensitive information; it's meant to be shared. There are a few ways to do this, but ssh-copy-id is often the easiest, you know.
From your local machine, run:
ssh-copy-id -i ~/.ssh/id_rsa.pub user@remote_iot_ipReplace user with the username on your IoT device and remote_iot_ip with its IP address. If you're connecting for the first time, you might be asked to confirm the connection and then enter the password for the user on the IoT device. After this, your public key will be placed in the ~/.ssh/authorized_keys file on the IoT device, which is where it needs to be, basically.
Configuring SSH on Your Ubuntu IoT Device
To make your SSH connection even more secure, you should adjust some settings on your IoT device. This is about making sure the "offices were securely guarded," as we mentioned before. You want to disable password authentication and only allow key-based access. This makes it much harder for someone to guess their way in, so.
On your IoT device (you can SSH in using the password for now, or connect directly if you have physical access), edit the SSH daemon configuration file:
sudo nano /etc/ssh/sshd_configFind these lines and make sure they are set as follows:
PasswordAuthentication no(This is very important.)PubkeyAuthentication yesPermitRootLogin no(Unless you absolutely need root login, which is rare.)ChallengeResponseAuthentication no
After making these changes, save the file and restart the SSH service for the changes to take effect:
sudo systemctl restart sshNow, your IoT device will only accept connections from clients with the correct private key, which is a much more secure manner of access, actually.
Enabling Direct P2P Connection (Without Port Forwarding)
This is where the "P2P" part really comes into play, especially if your IoT device is behind a NAT or firewall and you can't easily set up port forwarding. Tools like ZeroTier or Tailscale can help create a virtual private network (VPN) that makes your devices act as if they are on the same local network, even if they are geographically far apart. This effectively bypasses the need for manual port forwarding, which is often a pain, you know.
For example, with ZeroTier:
- Install ZeroTier on both your local machine and your Ubuntu IoT device.
- Create a ZeroTier network online and get its Network ID.
- Join both devices to this network using the Network ID.
- Authorize both devices in the ZeroTier central controller.
Once both devices are joined and authorized, they will each get a virtual IP address within the ZeroTier network. You can then SSH directly to your IoT device using its ZeroTier IP address, which is pretty much like connecting to a local machine. This creates a firm, invulnerable manner of connection, as the data is encrypted and routed within the virtual network, so.
Testing Your Connection
Now it's time to see if everything works. From your local machine, try to SSH into your IoT device using its ZeroTier IP address (or its public IP if you used port forwarding):
ssh -i ~/.ssh/id_rsa user@iot_zerotier_ipYou should be prompted for the passphrase you set for your private key, not the user's password on the IoT device. If you enter the correct passphrase, you should be logged into your remote Ubuntu IoT device. This means your connection is securely established, free from danger, and ready for you to use. It's a rather good feeling when it works, too.
Best Practices for Keeping Your IoT Connection Securely Fastened
Setting up a secure connection is a great first step, but keeping it secure requires ongoing attention. Just like a door that was securely fastened needs regular checks, your digital connections need care. These practices will help ensure your remote IoT access remains protected and private, very much like keeping your important documents in a place where they cannot be lost or stolen, you know.
It's about maintaining that secure manner of operation, making sure everything is firm and not loosely put together. These steps help protect or ensure the privacy or secrecy of your connection, for example, making it a reliable way to interact with your devices, so.
Regular Updates and Patches
Software vulnerabilities are discovered all the time. Keeping your Ubuntu IoT device's operating system and all its software up to date is one of the simplest yet most effective ways to stay protected. Updates often include security patches that fix known weaknesses, which is pretty important.
Make a habit of regularly running these commands on your IoT device:
sudo apt updatesudo apt upgradeThis ensures that your system has the latest protections available, keeping it free from danger, as it were. It's a bit like regularly checking the locks on your doors to make sure they are still strong, basically.
Disabling Password Authentication
As we did in the setup guide, making sure password authentication is completely off for SSH is a big deal. Passwords, even strong ones, can be guessed or cracked. SSH keys are much, much harder to compromise. This measure makes your connection incredibly secure, in a way, reducing the attack surface significantly, so.
Always double-check your /etc/ssh/sshd_config file to confirm that PasswordAuthentication no is indeed set. This ensures that only those with the correct private key can gain entry, which is a firm method of protection, really.
Using Strong Passphrases
Your SSH private key is protected by a passphrase. This passphrase is your last line of defense if someone somehow gets a hold of your private key file. A strong passphrase is long, complex, and not easily guessable. It's not just a password; it's a phrase, allowing for more words and symbols, which is quite helpful.
Think of a passphrase as a very important secret that should be kept securely. Don't use common phrases, personal information, or dictionary words. A good passphrase is something you can remember but is very hard for a computer to guess, you know.
Limiting User Access and Permissions
On your IoT device, make sure that only necessary users have access, and that those users have only the permissions they absolutely need. This is known as the principle of least privilege. If a user account is compromised, the damage it can do is limited if it doesn't have wide-ranging permissions, which is pretty smart.
For example, if a device only needs to run a specific sensor script, create a user account for that purpose and give it just the permissions needed for that script, and nothing more. This helps keep the system securely guarded from potential internal threats, even if an account is somehow breached, you see.
Firewalls: Your First Line of Defense
A firewall acts like a gatekeeper for your device's network traffic. It can block unwanted connections and only allow traffic that you specifically permit. Even with P2P tools like ZeroTier, having a local firewall on your Ubuntu IoT device adds an extra layer of protection, which is very helpful.

How To Securely Connect Remote IoT P2P SSH Ubuntu

How To Securely Connect Remote IoT P2P SSH Ubuntu
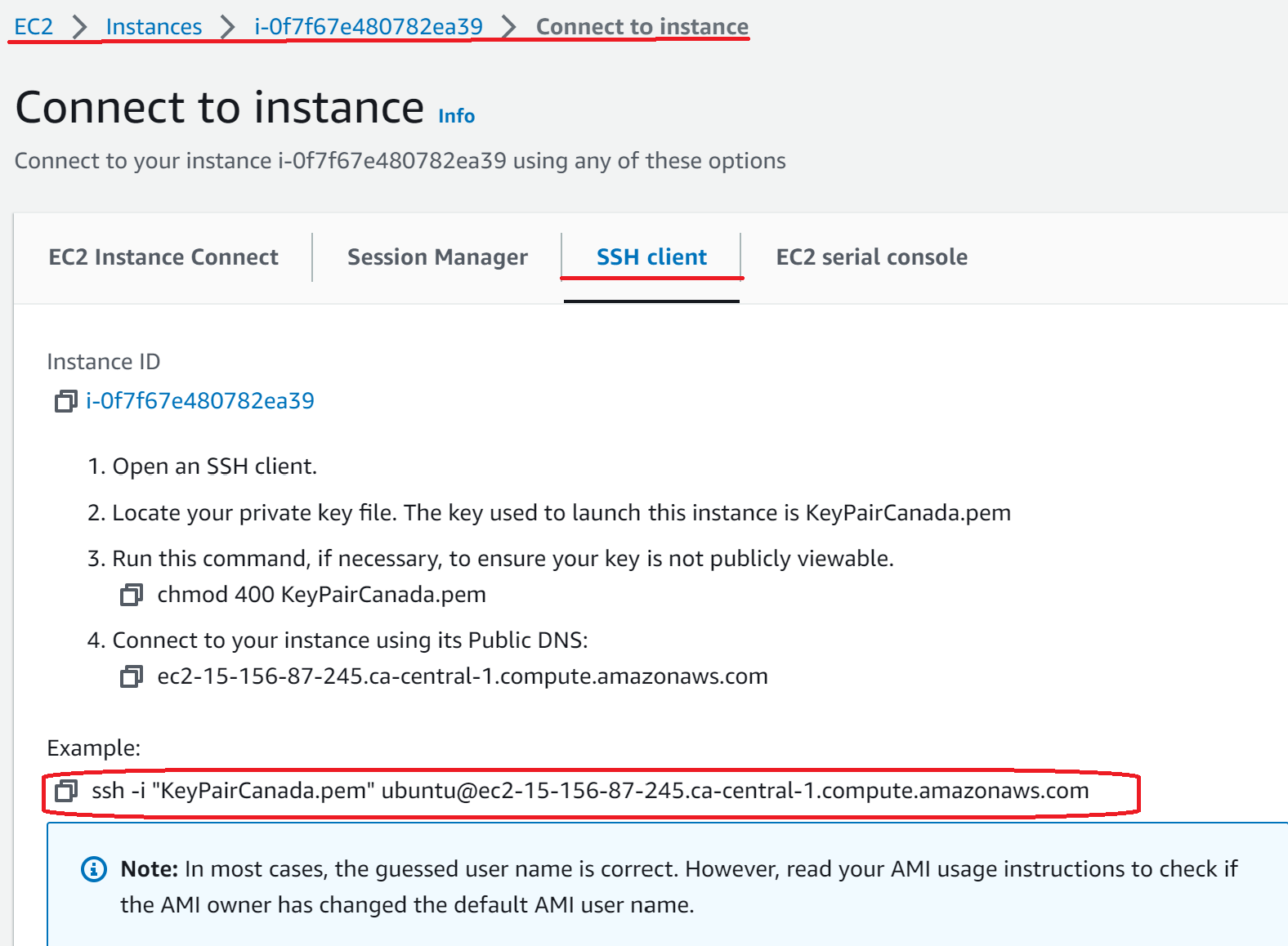
Connect ec2 ubuntu instance using Remote Desktop Connection (any RDP)