Unlock Safe Access: Securely Connect Remote IoT P2P SSH Ubuntu Server
It feels pretty unsettling, doesn't it, when a message pops up saying your device is at risk because it's out of date and missing important security and quality updates? Maybe you've seen those warnings, perhaps like the one saying, "This connection is untrusted you have asked firefox to connect securely to bay173.mail.live.com, but we can't confirm that your connection is secure." That kind of message, it really makes you think about how safe your digital world truly is. Especially with more and more smart devices, often called IoT, appearing everywhere, keeping them safe from afar becomes a very big deal. There's just a general worry, you know, about things not being as protected as they should be, and that's a feeling many of us share when we think about our digital lives.
Actually, this concern is even bigger when we talk about remotely managing IoT devices, especially those running on an Ubuntu server. Imagine you have a little computer, maybe a Raspberry Pi, tucked away somewhere, doing something important. You need to get to it, make changes, or just check on things, but you're not physically there. That's where the idea of a secure, peer-to-peer (P2P) SSH connection comes into play. It's about making sure that when you connect, it's not just working, but it's also truly safe, without those unsettling "untrusted connection" alerts popping up.
This piece is all about helping you figure out how to securely connect remote IoT P2P SSH Ubuntu server setups. We'll go through the steps, talk about what makes a connection genuinely safe, and give you some good ways to avoid those common problems connecting securely. So, you know, let's get you back on track so your remote IoT systems can run more securely, without all the fuss.
Table of Contents
- Why Security Matters for Your IoT Devices
- Understanding the Basics: IoT, P2P, and SSH
- Setting Up Your Ubuntu IoT Server for SSH
- Making Your P2P SSH Connection Secure
- Practical Steps for Secure P2P SSH
- Troubleshooting Common Connection Problems
- Frequently Asked Questions (FAQs)
- Final Thoughts on IoT Security
Why Security Matters for Your IoT Devices
Think about it, a device out there, maybe in your home or a business, that's connected to the internet. If it's not properly protected, it's almost like leaving a door unlocked. We often hear about how devices are at risk because they're out of date, missing important security updates. This is a very real problem. When a connection is untrusted, it can make you feel uneasy, and for good reason.
An insecure IoT device isn't just a small worry; it could be a way for bad actors to get into your entire network. This could lead to data theft, system damage, or even using your device to attack others. It's not just about protecting a single file, you know, but protecting the whole system and everything it connects to. So, keeping these devices safe is a very big deal, actually.
The risks are pretty varied, from simple annoyances to serious breaches. A lot of the time, the problem connecting securely to a website or device comes from not having the right protections in place. That's why setting up a truly secure connection, especially for something like a remote IoT P2P SSH Ubuntu server, is absolutely crucial. It's about building trust in your connections, which is something we all want.
Understanding the Basics: IoT, P2P, and SSH
Before we get too deep into the "how-to," it helps to have a clear idea of what we're talking about. These three terms – IoT, P2P, and SSH – are pretty central to our discussion about how to securely connect remote IoT P2P SSH Ubuntu server. Each one plays a distinct role, and together, they make up the foundation of what we're aiming for.
What is IoT in this context?
IoT, or the Internet of Things, basically refers to all those physical objects that have sensors, software, and other technologies built into them. These things connect and exchange data with other devices and systems over the internet. In our case, this could be anything from a smart thermostat to an industrial sensor, or even a small single-board computer like a Raspberry Pi running Ubuntu. These are the "things" we want to manage remotely, you know, securely.
Peer-to-Peer Connections Explained
A peer-to-peer (P2P) connection, in a way, is different from the usual client-server model. With P2P, devices talk directly to each other, rather than going through a central server. This can be really useful for IoT because it can reduce latency and sometimes even improve privacy, as data doesn't always need to travel through a third party. It's like two friends talking directly, without a middle person, which is pretty neat. However, setting up P2P securely, especially across different networks, can be a little tricky.
SSH: Your Secure Gateway
SSH stands for Secure Shell, and it's a network protocol that gives you a secure way to access a computer over an unsecured network. It provides strong authentication and encrypted data communication between two computers connecting over an open network, like the internet. For remotely managing an Ubuntu server, SSH is the standard, and it's a very good tool for keeping things safe. It's what helps us avoid those "untrusted connection" warnings, as a matter of fact.
Setting Up Your Ubuntu IoT Server for SSH
Getting your Ubuntu IoT server ready for a secure SSH connection involves a few initial steps. These steps are pretty basic, but they're absolutely essential for building a strong security foundation. You wouldn't want to skip them, really.
Initial Ubuntu Server Setup
First off, make sure your Ubuntu server installation is fresh and up-to-date. This means running updates right away. You know, like when your device is at risk because it's out of date and missing important security and quality updates? We want to avoid that from the start. So, open your terminal and run:
sudo apt update sudo apt upgrade -y This will fetch the latest package information and then install any available updates. It's a pretty good habit to get into, actually.
Installing and Configuring OpenSSH Server
Ubuntu usually comes with an SSH client, but for remote access, you need the SSH server component. If it's not already there, you can install it easily:
sudo apt install openssh-server -y Once installed, the SSH service should start automatically. You can check its status with:
sudo systemctl status ssh You'll want to make some changes to the SSH configuration file, which is located at `/etc/ssh/sshd_config`. It's a pretty important file, so be careful. Use a text editor like `nano`:
sudo nano /etc/ssh/sshd_config Inside this file, you can change the default port (usually 22) to a less common one. This is a simple step, but it helps a little bit with security by making your server less of an obvious target for automated scans. Find the line `Port 22` and change `22` to something like `2222` or another unused port number. Also, disable root login by changing `PermitRootLogin yes` to `PermitRootLogin no`. This is a very good security practice, as a matter of fact.
After making changes, save the file and restart the SSH service:
sudo systemctl restart ssh User Accounts and Permissions
It's always a good idea to create a dedicated user for SSH access rather than using the default `ubuntu` user, if you have one. This helps manage permissions more effectively.
sudo adduser your_new_username sudo usermod -aG sudo your_new_username The second command adds your new user to the `sudo` group, giving them administrative privileges when needed. This way, you're not logging in as root, which is generally less secure, you know.
Making Your P2P SSH Connection Secure
Just having SSH isn't enough; we need to make sure it's set up in the most secure way possible. This is where we really focus on keeping those connections from being untrusted.
The Importance of SSH Key Authentication
Passwords can be guessed or cracked, which is a pretty big risk. SSH key authentication is a much stronger method. It uses a pair of cryptographic keys: a public key that lives on your IoT server and a private key that stays securely on your local machine. When you try to connect, these keys essentially "shake hands" to verify your identity. This is far more secure than just a password. It's like having a very complex, unique digital fingerprint instead of a simple lock and key.
This method helps prevent issues like the "problem connecting securely to this website" because the authentication process is so robust. It basically means only someone with the correct private key can get in.
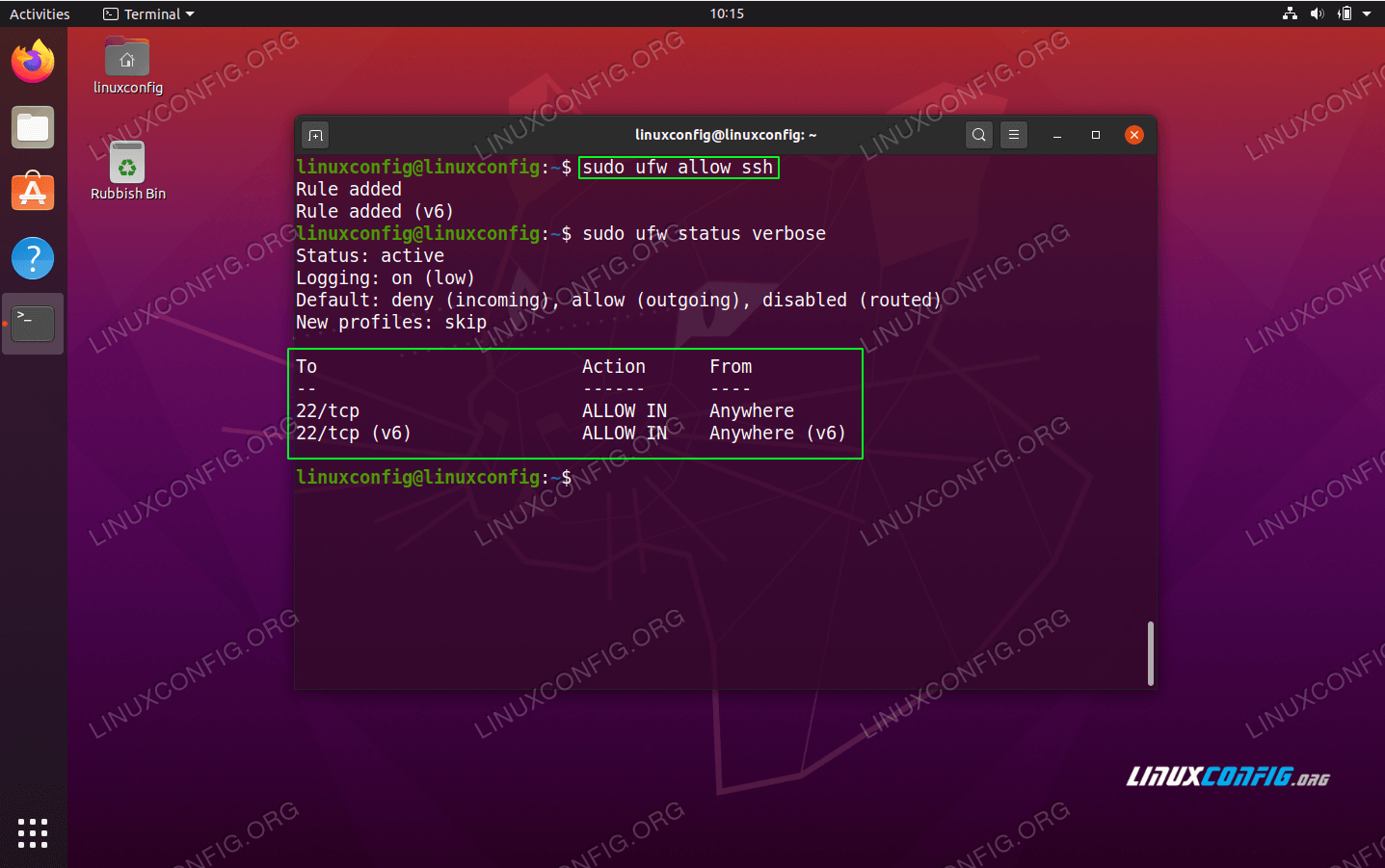
Firewall Rules for IoT Security
A firewall acts like a guard, controlling what traffic can come in and out of your server. Ubuntu typically uses `ufw` (Uncomplicated Firewall). You'll want to allow SSH traffic only on the port you configured earlier.
sudo ufw allow 2222/tcp # Replace 2222 with your chosen SSH port sudo ufw enable Make sure to allow only the necessary ports for your IoT applications. Blocking everything else is a very good security practice. You know, you don't want just any traffic getting through, actually.
Regular Updates and Maintenance
Remember that warning about your device being at risk because it's out of date? This is a continuous process for IoT devices. Regularly updating your Ubuntu server keeps it protected against newly discovered vulnerabilities. Set up a schedule for updates, or even consider automated updates if you're comfortable with that.
sudo apt update && sudo apt upgrade -y This simple command, run regularly, can prevent a lot of headaches down the line. It's a bit like routine maintenance for your car; it keeps everything running smoothly and safely.
Handling Dynamic IPs and NAT Traversal
Many remote IoT devices might have dynamic IP addresses, meaning their public IP changes over time. Also, they often sit behind a router using Network Address Translation (NAT), which can make direct P2P connections tricky.
For dynamic IPs, a Dynamic DNS (DDNS) service can help. This service maps a static hostname to your changing IP address. So, you always connect to `myiotdevice.ddns.net` instead of a fluctuating IP.
NAT traversal for P2P SSH can be more complex. Solutions often involve port forwarding on your router (mapping an external port to your IoT device's internal IP and SSH port) or using tools like reverse SSH tunnels or VPNs. For simple setups, port forwarding is often the easiest, but it does mean exposing a port to the internet, so security measures like SSH keys and firewalls are even more important. It's a pretty important consideration, as a matter of fact.
Practical Steps for Secure P2P SSH
Let's walk through the actual process of setting up SSH key authentication and making your first secure connection. This is where the rubber meets the road, you know.
Generating and Copying SSH Keys
On your local machine (the one you're connecting from), open a terminal and generate an SSH key pair:
ssh-keygen -t rsa -b 4096 Follow the prompts, and it's a very good idea to set a strong passphrase for your private key. This adds an extra layer of security.
Once generated, you need to copy your public key to your Ubuntu IoT server. The easiest way is with `ssh-copy-id`:
ssh-copy-id -i ~/.ssh/id_rsa.pub your_new_username@your_iot_device_ip -p 2222 Replace `your_new_username`, `your_iot_device_ip`, and `2222` with your actual details. You'll be asked for your user's password on the IoT device for this one time. After this, you should be able to connect using your key.
If `ssh-copy-id` isn't available or doesn't work, you can manually copy the public key:
cat ~/.ssh/id_rsa.pub | ssh your_new_username@your_iot_device_ip -p 2222 "mkdir -p ~/.ssh && chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys && chmod 600 ~/.ssh/authorized_keys" This command sends your public key to the server and puts it into the `authorized_keys` file, which is where SSH looks for public keys. It's a pretty neat trick, actually.
Configuring Your SSH Client
To make connecting easier, you can set up an SSH configuration file on your local machine (`~/.ssh/config`). This lets you use short aliases for your connections.
Host myiotdevice HostName your_iot_device_ip_or_ddns_hostname User your_new_username Port 2222 IdentityFile ~/.ssh/id_rsa Now, to connect, you just type `ssh myiotdevice`. This is much simpler than typing out the full command every time, and it helps you manage multiple devices, too it's almost.
Testing Your Secure Connection
After all these steps, it's time to try connecting. From your local machine, open a terminal and type:
ssh myiotdevice If you set a passphrase for your private key, you'll be prompted for it. If everything is set up correctly, you should get a command prompt for your remote Ubuntu IoT server. This confirms that you can securely connect remote IoT P2P SSH Ubuntu server, which is pretty exciting, you know.
Troubleshooting Common Connection Problems
Sometimes, you might run into a problem connecting securely. This is pretty common, actually. Here are a few things to check:
- Firewall Issues: Is your firewall on the Ubuntu server (and any network firewalls) allowing traffic on your chosen SSH port? This is a very frequent cause of connection failures.
- Incorrect IP Address or Port: Double-check the IP address or DDNS hostname and the port number you're trying to connect to. A simple typo can stop things from working.
- SSH Service Not Running: Make sure the OpenSSH server is actually running on your Ubuntu device (`sudo systemctl status ssh`). If it's not, try starting it (`sudo systemctl start ssh`).
- Permissions on Keys: Your SSH private key on your local machine needs to have very strict permissions (`chmod 600 ~/.ssh/id_rsa`). If the permissions are too open, SSH will refuse to use it, which is a security feature.
- User Account Issues: Is the username correct? Does the user have the necessary permissions on the IoT device?
- Network Connectivity: Can your local machine even reach the IoT device? Try pinging the device's IP address. If that doesn't work, it's a network issue, not an SSH one.
These checks can usually help you figure out what's going on when you have a problem connecting securely. It's often something pretty straightforward, as a matter of fact.
Frequently Asked Questions (FAQs)
How do I secure my IoT device from unauthorized access?
To keep your IoT device safe, you really want to use strong SSH key authentication instead of just passwords. Also, set up a firewall to block unnecessary ports, and always, always keep your software updated. It's also a good idea to disable root login and use a dedicated user account with limited privileges for daily tasks.
What are the best practices for remote access to Ubuntu server?
For remote access, it's best to use SSH key pairs for logging in, rather than passwords. Change the default SSH port, and make sure your firewall is configured properly. Regularly apply security updates, and perhaps consider two-factor authentication for an extra layer of protection. Using a VPN for connections can also add a lot of security, you know.
How can I ensure my P2P connection is encrypted?
When you use SSH for your P2P connection, the encryption is built right in. SSH uses strong cryptographic algorithms to protect all the data exchanged between your local machine and the remote IoT server. As long as you're using SSH, your connection is automatically encrypted, which is pretty much the point of it, actually.
Final Thoughts on IoT Security
Keeping your remote IoT devices safe and sound is a continuous effort, not just a one-time setup. The digital landscape is always changing, so what's secure today might need a little tweaking tomorrow. Just like those warnings about devices being at risk if they're out of date, staying on top of updates and security practices is pretty important.
By taking the time to securely connect remote IoT P2P SSH Ubuntu server setups, you're building a reliable foundation. This approach helps you avoid those frustrating moments where there's a problem connecting securely, or when a connection feels untrusted. It's about having peace of mind, knowing that your devices are doing their job without exposing you to unnecessary risks.
For more details on keeping your systems safe, you might want to check out
How To Use Ssh On Ubuntu Server

How To Securely Connect Remote IoT P2P SSH Ubuntu
Firewall Friday: SSH - Securely Connect to Your Remote Server