Securely Connect Remote IoT: Your Android Guide To P2P SSH
Connecting to your smart devices from far away, say, from your Android phone, feels pretty amazing, doesn't it? Yet, making sure those connections stay private and safe is, well, absolutely vital. Think about it: your smart home gadgets, industrial sensors, or even that little weather station in your backyard, they all hold pieces of your life or important information. You want to make sure the "door" to these devices is securely fastened, just like you'd want your offices securely guarded. This article shows you how to securely connect remote IoT P2P SSH download Android, giving you peace of mind.
You see, many people wonder how to get a good, firm grip on their internet-connected things when they're not right there. It's a common worry, you know, about someone else possibly peeking in or messing with your devices. We're talking about more than just convenience here; it's about making sure your private world stays private, and your device operations stay exactly as you intend them. That's where a peer-to-peer (P2P) setup with SSH, accessed right from your Android device, really shines, offering a way to keep things free from danger.
So, this guide will walk you through the ins and outs of making those distant IoT connections incredibly safe, using a clever method that brings your Android phone right into the picture. We'll explore why security is so important, how P2P and SSH work together, and then give you some clear steps to get everything set up. By the end, you'll have a much better idea of how to keep your smart devices securely managed, no matter where you happen to be, very much like keeping an important document securely, in a place where it cannot be lost or stolen.
Table of Contents
- Why Secure Remote IoT Connections Matter
- Understanding P2P SSH for IoT
- Getting Started: Securely Connecting Your IoT Device to Android
- Best Practices for Keeping Your IoT Connections Safe
- Common Hurdles and How to Clear Them
- Frequently Asked Questions
Why Secure Remote IoT Connections Matter
So, why bother with all this talk about keeping things safe when you just want to turn off a light or check a sensor? Well, it's pretty simple, actually. Every time an IoT device connects to the internet, it creates a pathway, and if that pathway isn't securely guarded, it could be like leaving a window open in your house. As of October 2023, the number of smart devices out there keeps growing, and so does the need to keep them protected.
The Risks of Unsecured IoT
Picture this: a smart camera in your living room, or perhaps a connected thermostat, is left without proper safety measures. Someone with bad intentions could, in a way, just walk right in. This could mean they see what your camera sees, change your home's temperature, or even use your device to cause trouble elsewhere on the internet. Your personal information, your daily routines, and even your home's physical safety could be at risk. It's a bit like having your front door not securely fastened, you know, just a slight push could open it.
Beyond personal risk, there's also the bigger picture. Many IoT devices, if not securely set up, can be gathered into what people call "botnets." These are large groups of hijacked devices used to launch attacks on websites or services, causing big problems for everyone. It's really about making sure your device isn't loosely connected, but rather firmly part of a safe network, free from danger for others too.
The Promise of P2P SSH
This is where securely connecting remote IoT P2P SSH download Android comes into its own. P2P, or peer-to-peer, means your Android phone talks directly to your IoT device, more or less bypassing central servers that could be a weak point. Then, you add SSH, which stands for Secure Shell. SSH is a method for secure remote access that makes sure the information exchanged between your phone and your device is encrypted, meaning it's scrambled so only the right people can read it. It's like having a secret code for your conversations, so no one can listen in. This combination means your connection is very much free from danger.
Using this method, you're building a connection that's not easily intercepted or messed with. Your data travels directly and privately. It gives you a kind of direct line, a very firm connection, between your Android device and your IoT gadget, making it feel like they're right next to each other, even when they're miles apart. This really helps to protect or ensure the privacy or secrecy of your connection, a bit like securing a telephone line.
Understanding P2P SSH for IoT
So, let's break down what P2P and SSH actually mean in this context, because, you know, these terms can sometimes sound a bit technical. It's really about understanding how they work together to make your remote IoT connection secure. This approach is, in a way, quite clever in how it handles security.
What is P2P Connectivity?
Normally, when your phone talks to a smart device, the message might go through a central server, like a cloud service. Think of it like sending a letter through a post office. P2P is different; it's like sending a letter directly to your friend's house, without a middle stop. In the world of IoT, this means your Android phone can communicate directly with your IoT device, assuming both can find each other on the network. This direct line can be faster and, arguably, less prone to certain types of attacks, since there's no central server to be compromised. It's a more direct way of doing things, you know, very efficient.
This directness means your data doesn't have to travel as far, or through as many different systems. It's a connection that feels very personal, just between your phone and your device. This directness also means you're not relying on a third party to manage your connection, which, for some people, offers a lot more control and a feeling of security. It's about being able to firmly connect without extra steps.
How SSH Adds a Layer of Safety
Now, SSH comes in to make sure that direct P2P letter is sent in a securely sealed envelope. SSH creates an encrypted tunnel between your Android phone and your IoT device. Any information that passes through this tunnel, whether it's commands you're sending or data you're receiving, is scrambled. This means if someone were to intercept it, they wouldn't be able to make sense of it. It's a powerful way to protect your communications, like having a very strong lock on that door.
SSH also helps confirm that you're talking to the right device, and that the device is talking to the right person (you!). It uses special keys, which are like very complex passwords, to verify identities. This makes sure your connection is not loosely set up, but rather very firmly established, so you know you're connecting to your actual device, and not some imposter. This certificate, the SSH key, is an important document, and should be kept securely.
Getting Started: Securely Connecting Your IoT Device to Android
Alright, so you're ready to get your hands dirty and make this secure connection happen. It's not as hard as it might sound, especially once you have the right tools and know the basic steps. We'll go through what you need on your IoT device and then how to get the right app on your Android phone, very straightforward stuff.
Prerequisites for Your IoT Device
First off, your IoT device needs to be ready for SSH. Most single-board computers like Raspberry Pi, or even some more advanced smart hubs, already have SSH capabilities built in, or you can add them. You'll want to make sure SSH is enabled on your device. Also, it's a really good idea to change the default password, if there is one, to something unique and strong. This is a basic step, but it's very important for keeping things securely guarded.
You'll also need to know your IoT device's IP address on your local network. This is how your phone will initially find it. If your device moves around or gets a new IP often, you might need a way for it to tell you its current address, perhaps through a dynamic DNS service, or by having it send its IP to a service you can check. This ensures you can always find it, even if its address changes, keeping your connection firm.
Choosing the Right Android App
This is where the "download Android" part comes in. You'll need an SSH client application for your Android phone. There are quite a few good ones available on the Google Play Store. When picking one, look for an app that has good reviews, is regularly updated, and offers features like key management, which is how you'll store those special SSH keys we talked about. Some popular choices might include Termius or JuiceSSH, but there are others, so, you know, check them out.
Make sure the app you choose allows for P2P connections, or at least supports port forwarding if you need to go through a router. The app should also make it easy to manage multiple connections, in case you have more than one IoT device you want to control. It's about finding something that feels right and is easy for you to use, so you can connect securely and without much fuss.
Step-by-Step Connection Guide
Here's a basic rundown of how to get your securely connected remote IoT P2P SSH download Android setup working:
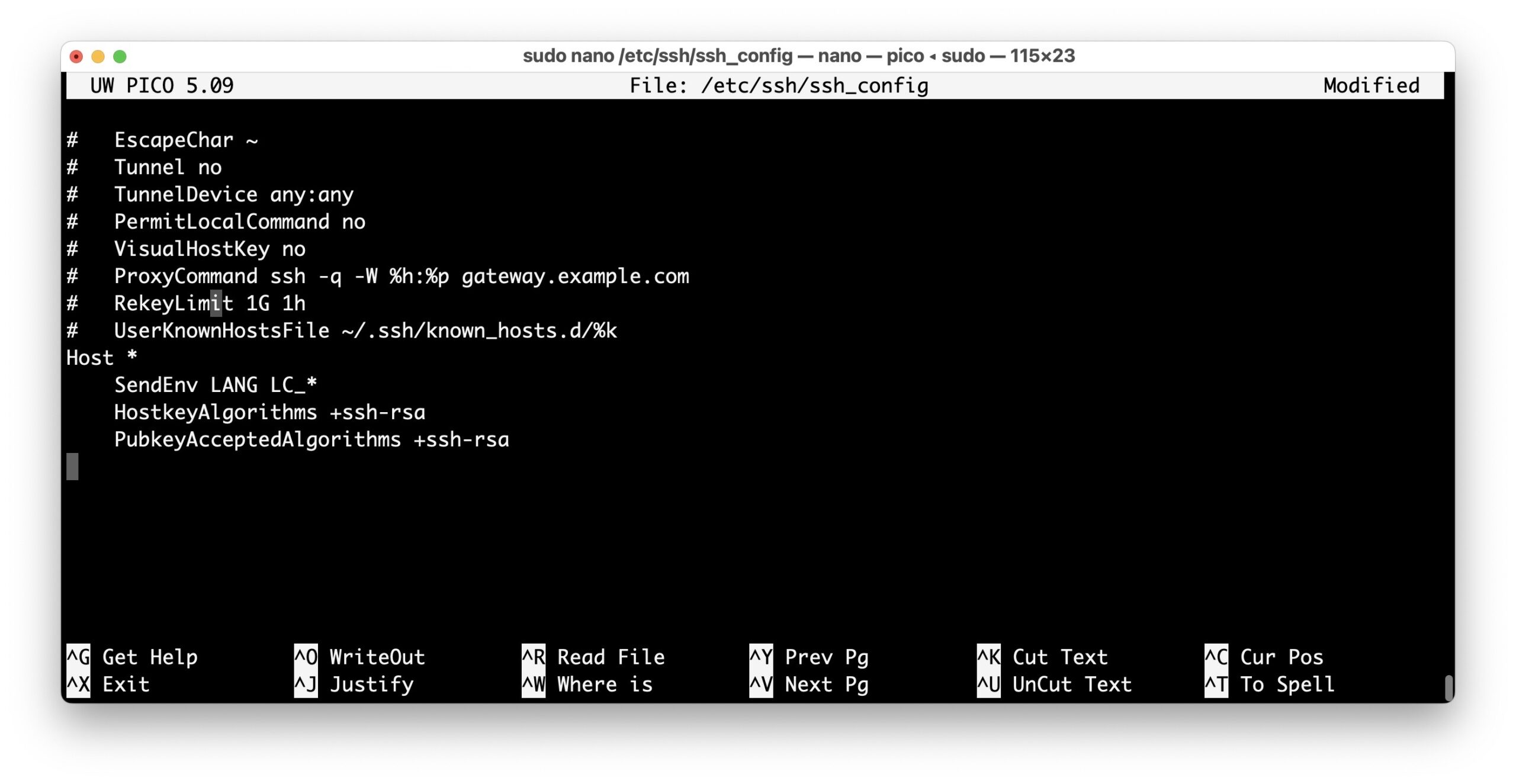
- Enable SSH on your IoT Device: This usually involves a simple command or setting change on the device itself. For a Raspberry Pi, it might be `sudo raspi-config` and then choosing the SSH option.
- Generate SSH Keys: On your Android SSH app, you'll typically find an option to generate a new SSH key pair. This creates a public key and a private key. The private key stays on your phone, kept securely, while the public key goes on your IoT device.
- Copy Public Key to IoT Device: This is a very important step. You'll need to copy the public key from your Android app to your IoT device's `~/.ssh/authorized_keys` file. Many SSH apps have a helper function for this, or you might do it manually using a command like `ssh-copy-id`. This makes sure your device recognizes your phone.
- Configure P2P Connection (if needed): For true P2P, both devices need to be able to find each other directly. This might involve network settings or using a service that helps devices discover each other without a central server. For simpler setups, if both are on the same local network, this might happen automatically.
- Connect from Android: Open your SSH app, create a new connection profile, enter your IoT device's IP address (or hostname), specify the SSH port (usually 22), and select the private key you just generated. Hit connect!
Once connected, you'll have a secure command-line interface to your IoT device, allowing you to send commands, check status, and manage it remotely. It's a direct, firm connection, giving you control. You can learn more about secure connections on our site, and also check out this page for more IoT security tips.
Best Practices for Keeping Your IoT Connections Safe
Setting up that initial secure connection is a big win, but keeping it that way, well, that requires a bit of ongoing care. Just like you'd want your personal items securely stowed, your IoT connections need constant attention. It's about staying free from danger, you know, really.
Strong Authentication is a Must
We talked about SSH keys, and they are, in fact, much better than just passwords alone. Always use SSH key-based authentication for your remote connections. If you absolutely must use a password, make it incredibly long and complex, a random string of characters, numbers, and symbols. Never use common words or personal details. Also, consider setting up two-factor authentication if your SSH server and Android app support it. This adds another layer of verification, making it much harder for someone to get in, even if they somehow got your key. It's about making sure the access is very firmly restricted.
Remember that certificate, the SSH key? It's an important document, and it should be kept securely. This means not sharing your private key with anyone and storing it in a safe place on your Android device, ideally protected by a strong password or biometric lock within the app itself. This step is, arguably, one of the most important for maintaining security.
Regular Updates, Always
Software, whether it's on your IoT device or your Android SSH app, gets updated for a reason. These updates often include fixes for security weaknesses that bad actors might try to exploit. So, make it a habit to regularly update the operating system on your IoT devices and keep your Android SSH client app current. It's a bit like making sure your offices are securely guarded with the latest alarm systems. Outdated software can leave open doors, which, you know, we want to avoid.
This also applies to any libraries or programs running on your IoT device that are exposed to the network. Keep them all patched and current. It's a continuous process, but it's very much worth the effort to keep your connections free from danger. A firm commitment to updates can really make a difference.
Monitoring Your Connections
It's a good idea to periodically check the logs on your IoT device for any unusual activity. Most operating systems keep a record of who tried to connect and when. If you see failed login attempts from unfamiliar IP addresses, that's a sign someone might be trying to get in. You can also set up alerts for certain activities, if your device or network allows it. This helps you catch potential issues early, so you can react quickly. Being aware is, in a way, another layer of security, making sure everything is securely guarded.
This kind of watchful eye helps ensure your remote connections remain not loosely managed, but very firmly controlled by you. It's about knowing what's happening on your network and being able to spot anything that looks out of place. This proactive approach helps keep your system free from danger.
Common Hurdles and How to Clear Them
Even with the best intentions, you might hit a few bumps along the road when trying to securely connect remote IoT P2P SSH download Android. But don't worry, most common issues have pretty straightforward solutions. It's just a matter of knowing what to look for, very often.
Dealing with Firewalls and NAT
One of the biggest challenges for P2P connections is often network address translation (NAT) and firewalls. Your home router uses NAT to share one public IP address among many devices on your private network. This means devices on the internet can't directly "see" your IoT device. For true P2P, both your Android phone and your IoT device might need to be able to initiate connections to each other, or you might need to use a technique called "hole punching" or a relay server to get around NAT. Some P2P SSH solutions handle this automatically, which is pretty handy.
If you're dealing with a strict firewall, either on your router or on your IoT device itself, it might block SSH connections. You'll need to configure the firewall to allow incoming connections on the SSH port (usually 22). This is often called "port forwarding" on your router. Just make sure to only open the specific port needed and direct it only to your IoT device's internal IP address. This helps keep the rest of your network securely guarded. It's about being very precise with your network settings, so things are not loosely configured.
Optimizing for Performance
Sometimes, even a secure connection can feel a bit slow, especially if you're trying to do something bandwidth-intensive, like streaming video from an IoT camera. Performance can be affected by your internet speed, the distance between your phone and the IoT device, and the processing power of the IoT device itself. If you find your connection sluggish, try to reduce the amount of data being sent. For example, if it's a camera, lower the resolution or frame rate. You could also look into SSH compression options, which can sometimes speed things up by making the data smaller before sending it. It's about finding a good balance, you know, so it feels firm and responsive.
Also, make sure your Wi-Fi signal is strong where your IoT device is located. A weak signal can cause dropped packets and slow down your connection, making it feel less reliable. A good, stable connection is key for a truly secure and usable remote setup. This helps ensure your device is free from danger of disconnects, and that your commands go through firmly.
Frequently Asked Questions
People often ask a few common things about securely connecting remote IoT P2P SSH download Android. Here are some answers to those very questions.
Is SSH secure for IoT?
Yes, SSH is considered very secure for IoT connections, provided it's set up correctly. It uses strong encryption to protect your data and authentication methods to verify identities. Using SSH keys instead of just passwords makes it even safer. It's like having a very strong lock on your device's connection, making sure it's securely fastened and free from danger.
How do I access my IoT device remotely without a static IP?
You can access your IoT device remotely without a static IP address by using dynamic DNS (DDNS) services. These services give your device a fixed hostname that automatically updates with its current, changing IP address. Some P2P SSH solutions also use relay servers or "hole punching" techniques to help devices connect without needing a static public IP. It's about finding a way for your device to tell the world where it is, even if its address changes, so you can always connect firmly.
Can I control my smart devices from my Android phone securely?

Securely Connect Remote IoT P2P SSH Android: A Comprehensive Guide For
Securely Connect Remote IoT P2P SSH Android: A Comprehensive Guide For

Securely Connect Remote IoT P2P Download Android: A Comprehensive Guide