SSH IoT Anywhere Examples: Connecting Your Devices Remotely
Connecting to your Internet of Things (IoT) devices from a distance can seem like a puzzle, yet it's often a very simple task with the right tools. Think about managing smart sensors in a far-off location or perhaps updating software on a tiny computer placed in a remote spot. For these kinds of situations, having a secure way to reach your devices, no matter where they are, makes a big difference. This is where the idea of `ssh iot anywhere examples` truly shines, offering a reliable path to remote access.
Today, with so many gadgets around us, the need to control them without being right next to them is growing. Whether it's a small single-board computer running a home automation system or a network of industrial sensors, getting access to these devices securely and easily is pretty important. This article will help you understand how SSH can be your go-to method for this, offering a lot of practical advice.
We'll look at how SSH helps you connect to your IoT devices from, well, just about anywhere. We will go through setting things up, dealing with common issues, and even some clever ways to make your remote connections more helpful. You will see how managing your devices, like a tiny Raspberry Pi or an industrial controller, becomes a lot more straightforward, so, let's explore this together.
Table of Contents
- The Heart of Remote IoT Access: SSH
- Setting Up SSH for Your IoT Devices
- Real-World SSH IoT Anywhere Examples
- Troubleshooting Common SSH IoT Issues
- Frequently Asked Questions
- Looking Ahead with SSH and IoT
The Heart of Remote IoT Access: SSH
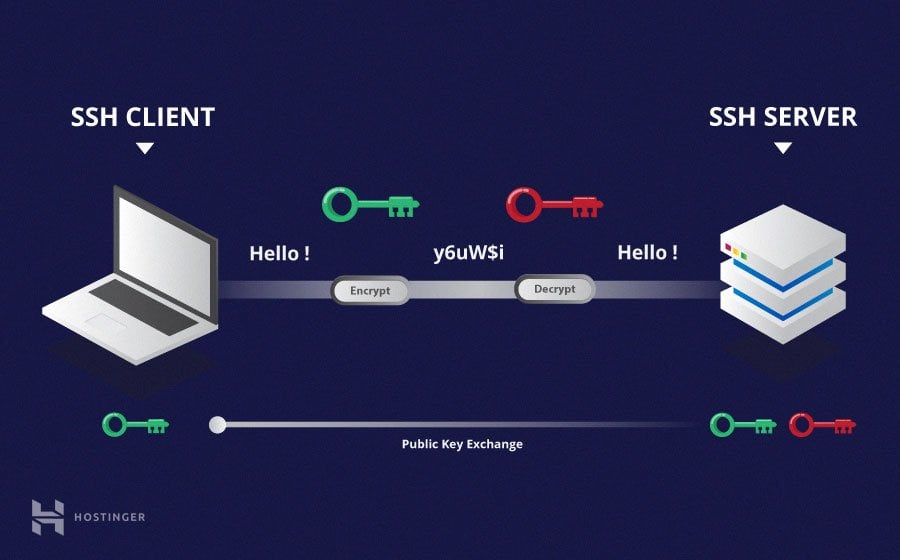
SSH, or Secure Shell, is a network protocol that gives you a safe way to operate network services over an unprotected network. It's like having a secure phone line directly to your device, even if that device is far away. For IoT, this means you can send commands, get information, and even change settings on a device without needing to be physically present. It's a very helpful tool for anyone with remote gadgets.
The main idea behind SSH is its strong security. It encrypts all communication between your computer and the IoT device. This helps keep your commands and the device's responses private, so no one can easily snoop on your connection. This security is a big reason why SSH is a top choice for `ssh iot anywhere examples` when you need to connect to things remotely, as a matter of fact.
You might be wondering what makes SSH so special for IoT. Well, many IoT devices, like a Raspberry Pi or an ESP32 with a Linux-like operating system, come with SSH built-in or can have it added quite easily. This means you don't need special software on the device itself, making it simpler to get started. It's a bit like having a universal remote for all your smart devices, you know.
Setting Up SSH for Your IoT Devices
Getting your IoT device ready for SSH access involves a few steps. It's not too difficult, but paying attention to the details helps make sure your connection is secure and works well. We'll go through the basics first, then look at how to manage keys and set up your Windows computer for SSH, too.
Basic Device Setup
Most IoT devices that run a Linux-based system, such as a Raspberry Pi, typically have SSH ready to go. You usually just need to enable it, sometimes through a simple command or a configuration tool. For example, on a Raspberry Pi, you might use `sudo raspi-config` and select the SSH option. Once it's on, your device is ready to listen for incoming SSH connections, which is pretty neat.
After enabling SSH, you'll need the device's IP address. If your device is on your home network, you can often find its IP address through your router's administration page or by using network scanning tools. This address is how your computer will find the device on the network, sort of like a street address for your smart gadget.
For connecting from outside your local network, things get a little more involved. You might need to set up port forwarding on your router, or use a VPN, or a service that helps tunnel connections. This allows outside traffic to reach your IoT device's SSH port. Remember, opening ports can have security risks, so always use strong passwords and SSH keys, basically.
SSH Key Management for IoT
Using SSH keys is a much safer way to connect than relying on just passwords. An SSH key pair has two parts: a private key that stays on your computer and a public key that you put on your IoT device. When you try to connect, the device checks if your private key matches its public key, creating a very secure handshake. This is a bit like having a special lock and key for your device.
Creating an SSH key pair is usually done with a command like `ssh-keygen` on your computer. Once you have the keys, you'll need to copy the public key to your IoT device. A common way to do this is using `ssh-copy-id`, or manually copying the contents of your public key file (often `~/.ssh/id_rsa.pub`) into the `~/.ssh/authorized_keys` file on the device. For instance, you might use a command like `pbcopy < ~/.ssh/id_rsa.pub` to copy your public key to your clipboard, then paste it into the device's `authorized_keys` file. This process is very important for security, you know.
When you're adding an SSH key, especially to a cloud platform VM that might be hosting some IoT services, you might notice it picks up a username and saves the key under it. This can sometimes be a bit confusing, as you might think it's just a general metadata key. However, it's actually tied to a user for connection purposes. This behavior is something to keep in mind when setting up access for your devices, to be honest.
Configuring SSH on Windows for IoT
Many people use Windows computers to manage their IoT devices. OpenSSH is now built into Windows 10 and 11, making it much easier to use SSH from PowerShell or the Command Prompt. This means you don't typically need extra software to get started, which is nice. You can just open PowerShell and start typing your SSH commands, like `ssh username@your_iot_device_ip`.
For more advanced setups, like setting a specific host name and port for your IoT device, you can use an SSH config file. This file, usually located at `C:\Users\YourUser\.ssh\config` on Windows, lets you create shortcuts and custom settings for your connections. You can edit or create this file by typing `notepad C:\Users\YourUser\.ssh\config` in PowerShell. This file is super helpful for organizing your connections, kind of.
Inside the config file, you can define specific hosts. For example, you might have:
Host my_iot_device HostName 192.168.1.100 Port 22 User pi IdentityFile C:\Users\YourUser\.ssh\id_rsa_iot This way, you can just type `ssh my_iot_device` to connect, and all the details are handled for you. It simplifies connecting to multiple devices, which is pretty convenient.
Real-World SSH IoT Anywhere Examples
Now, let's look at some practical ways you can use SSH to interact with your IoT devices, no matter where they are. These examples show how versatile SSH can be for different needs, from checking on sensors to running scripts.
Remote Monitoring and Control
One of the most common uses for `ssh iot anywhere examples` is to check on your devices and send them commands. Imagine you have a weather station running on a small computer in your garden. You can SSH into it from your office, check the sensor readings, or restart a service if something seems off. It's like having a direct line to your garden, you know.
For instance, you might SSH into your device and run a command like `cat /var/log/syslog` to check system logs, or `vcgencmd measure_temp` to see the CPU temperature on a Raspberry Pi. This gives you immediate feedback and control, which is very helpful for keeping your devices running smoothly. You can pretty much do anything you could do if you were sitting right in front of the device.
If you're dealing with multiple devices, perhaps in different locations, SSH helps you manage them all from one spot. You can set up your SSH config file with different host entries for each device, making it easy to jump between them. This helps a lot when you have a small farm of IoT sensors or smart home gadgets to look after, so.
Scripting IoT Tasks from a Distance
SSH isn't just for typing commands one by one. You can also use it in scripts to automate tasks on your IoT devices. This is incredibly powerful for things like scheduled data collection, software updates, or even deploying new code to many devices at once. It's like having a robot assistant for your remote gadgets.
Suppose you have a script on a central server that needs to execute some commands on an IoT device. You can use SSH with your private key file to run these commands without needing to type your password each time. The command might look something like `ssh -i ~/.ssh/my_private_key_file user@iot_device_ip 'sudo apt update && sudo apt upgrade -y'`. This allows for completely automated interactions, which is quite useful.
This kind of scripting is particularly good for maintaining many devices. You can write a single script that loops through all your IoT devices, checks their status, and applies any needed updates. This saves a lot of time and effort, especially as your number of devices grows, you know.
Secure File Transfers to Your Devices
Moving files to and from your IoT devices is another common need. Whether it's uploading a new program, downloading sensor data, or getting log files, doing it securely is important. SSH provides tools like `scp` (Secure Copy) and `sftp` (SSH File Transfer Protocol) for this purpose, which are very reliable.
With `scp`, you can copy files directly from your computer to your IoT device, or vice-versa, using commands like `scp my_new_program.py user@iot_device_ip:/home/user/`. This is great for quick transfers. For a more interactive experience, `sftp` gives you a file transfer interface that feels a bit like an old-school FTP client, but with all the SSH security built in.
Some people want to connect to an SFTP server using their Windows file explorer. While the explorer has an option for FTP, it typically doesn't directly support SFTP. You would generally need a separate SFTP client application, like WinSCP or FileZilla, to get that kind of direct file explorer integration for secure transfers. This is a common point of confusion, but there are good tools available, you know.
Graphical Access with X11 Forwarding
Sometimes, your IoT device might have a graphical interface or you might need to run a graphical application on it. SSH's X11 forwarding feature lets you display these graphical applications on your local computer's screen, even though the application is running on the remote device. It's like having a window into your device's desktop, pretty much.
To use X11 forwarding, you typically need an X server running on your local machine (like Xming for Windows or XQuartz for macOS) and you add the `-X` option to your SSH command: `ssh -X user@iot_device_ip`. If you run SSH and the display isn't set, it means SSH isn't forwarding the X11 connection. To confirm that SSH is forwarding X11, you can check for a line containing "requesting X11 forwarding" in the output when you connect with verbose mode (`-v`). This helps a lot when you need to see a visual output from your device, for example.
This feature is really useful for debugging graphical applications on your IoT device or for using tools that only have a graphical interface. It means you don't have to connect a monitor, keyboard, and mouse to your device every time you need to see something on its screen, which is very handy for devices in hard-to-reach spots, sort of.
Troubleshooting Common SSH IoT Issues
Even with a straightforward tool like SSH, you might run into a few bumps along the way. Knowing how to handle common problems can save you a lot of frustration. Let's look at some typical issues you might encounter when dealing with `ssh iot anywhere examples`.
Dealing with IP Changes and Warnings
One common issue happens when an IoT device's IP address changes. If you frequently log into a device via SSH and its IP address changes, you might get a "man in the middle attack" warning when you try to connect again. This happens because your computer remembers the old IP address and its associated host key. When the IP changes, the host key for that IP no longer matches what your computer expects, so it warns you, basically.
To fix this, you need to remove the old host key entry from your computer's `known_hosts` file. On Windows, this file is usually at `C:\Users\YourUser\.ssh\known_hosts`. You can open it with a text editor and delete the line that refers to the old IP address of your IoT device. Once removed, the next time you connect, SSH will add the new host key, and the warning will go away. This is a simple fix for a rather alarming message, you know.
It's important to understand that these warnings are there for your safety. They help protect you from actual malicious attacks. So, always check why you're getting such a warning before simply deleting the entry. If you know the IP address changed legitimately, then removing the old entry is fine, as a matter of fact.
Managing Multiple SSH Keys
As you work with more IoT devices or different services, you might find yourself needing to use multiple SSH keys. For example, you might have one key for your home automation devices and another for cloud-hosted IoT platforms. The challenge then becomes how to tell SSH which key to use for which connection. This is where your SSH config file becomes even more useful.
If you want to use multiple SSH keys, perhaps one key gets a name like `id_rsa_test`, you can configure your `.ssh/config` file under Windows to work with a usual Git server or any SSH connection. You simply add an `IdentityFile` line under each `Host` entry, pointing to the specific private key file for that connection. For example:
Host my_test_device HostName 192.168.1.101 User admin IdentityFile C:\Users\YourUser\.ssh\id_rsa_test Host another_device HostName 192.168.1.102 User root IdentityFile C:\Users\YourUser\.ssh\id_rsa_another This way, when you type `ssh my_test_device`, SSH knows exactly which key to use. The documentation might not always be clear on how to explicitly use only that key, but the `IdentityFile` option is the way to do it. This helps keep your keys organized and connections secure, too.
Understanding SSH Security Settings
SSH offers many options to fine-tune its security, including which MACs (Message Authentication Codes), ciphers, and key exchange algorithms (KEX) it supports. These settings determine how secure and compatible your SSH connections are. Knowing how to check and adjust these can be helpful for securing your `ssh iot anywhere examples`.
If you want to find out dynamically what MACs, ciphers, and KEX algorithms SSH supports, without looking at the source code, you can use verbose mode (`ssh -v`) or specific options. For example, OpenSSH 5.7 introduced the `KexAlgorithms` option, and you can add a `KexAlgorithms` knob to the client and server configuration to allow selection of which key exchange methods are used. This is important for ensuring your IoT connections use the strongest available encryption, you know.
For instance, to see what algorithms your client supports, you might try `ssh -Q cipher`, `ssh -Q mac`, or `ssh -Q kex`. This information helps you make informed choices about your SSH configuration, especially if you're connecting to older IoT devices that might only support less secure methods. It's a bit like picking the right lock for your door, you want the strongest one available, generally.
Frequently Asked Questions
Can I connect to my IoT device via SSH if it's behind a firewall or router?
Yes, you can, but it often requires some extra setup. You might need to configure port forwarding on your router to direct incoming SSH traffic to your IoT device's specific IP address on your local network. Another way is to use a VPN or a reverse SSH tunnel, which can help bypass strict firewall rules. These methods make it possible to reach your device from anywhere, you know.
Is SSH secure enough for all my IoT devices?
SSH is considered very secure when set up correctly. Using SSH keys instead of passwords, disabling root login, and keeping your SSH software updated are all important steps to make it as secure as possible. However, the overall security of your IoT device also depends on the device's operating system and other software running on it. So, while SSH is a strong part of the security, it's part of a bigger picture, basically.
What if my IoT device doesn't have a screen or keyboard? How do I set up SSH initially?
Many IoT devices, like Raspberry Pis, can be set up "headless" without a screen or keyboard. For example, you can flash the operating system image to an SD card and enable SSH by creating an empty file named `ssh` in the boot partition of the SD card. Once the device boots up, it will enable SSH, and you can then connect to it over the network using its IP address. This makes initial setup quite simple, you know.
Looking Ahead with SSH and IoT
The ability to connect to your IoT devices from anywhere using SSH is a very valuable skill. It gives you control, flexibility, and a strong sense of security over your remote gadgets. From basic monitoring to complex scripting and secure file transfers, SSH covers a lot of ground for `ssh iot anywhere examples`.
As IoT continues to grow, so will the need for reliable and secure remote access methods. SSH, with its long history of dependable service, remains a top choice for many. By understanding its features and how to handle common challenges, you're well-prepared to manage your smart devices, no matter where they are located. To learn more about secure remote access on our site, you can explore other resources. Also, feel free to check out this page for more technical details.
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

What is a Secure Shell Protocol (SSH)? Everything to Know